UNC5174, a Chinese-affiliated threat actor, has updated its attack toolkit with new open-source tools named “SNOWLIGHT” and “VShell,” expanding their command-and-control infrastructure and cyberattack capabilities. Recent investigations revealed more than 70 indicators of compromise (IoCs), including domains and IP addresses distributed globally, some of which have been weaponized in active attacks. #UNC5174 #SNOWLIGHT #VShell
Keypoints
- UNC5174 has deployed new tools SNOWLIGHT and VShell alongside their previous use of SUPERSHELL for cyber operations in 2025.
- The research uncovered 25 initial IoCs comprising 13 domains and 12 IP addresses linked to the latest campaign.
- Further analysis expanded the list with dozens more IoCs, including 67 IP-connected domains and 199 string-connected domains, several actively used in malicious activities.
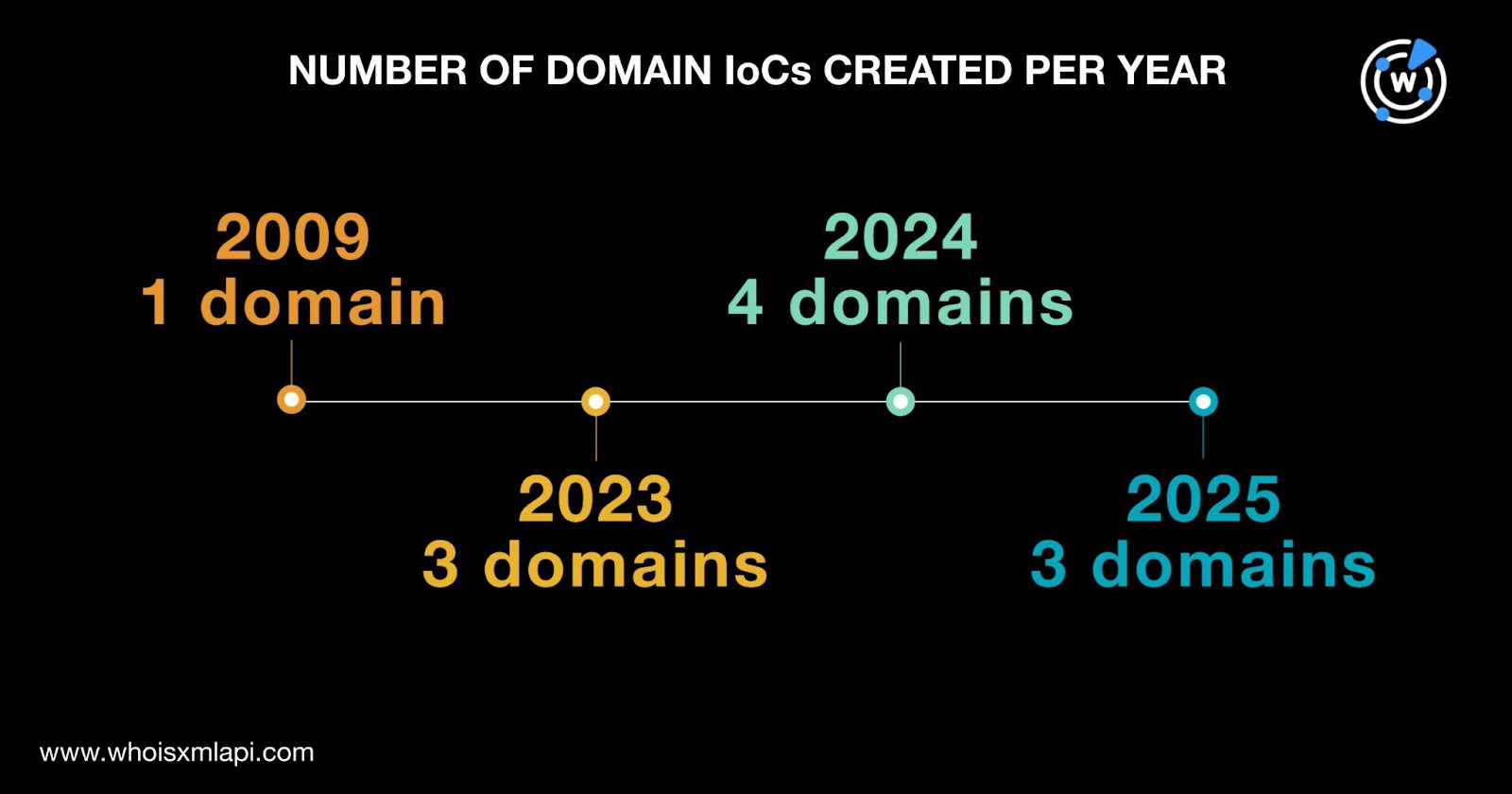
- The identified domains were registered between 2009 and 2025, managed by multiple registrars, primarily GoDaddy, and mostly registered in the U.S.
- Twelve IoC IP addresses were geolocated mainly in China and were administered predominantly by Google and Alibaba ISPs.
- Historical DNS data showed extensive domain-to-IP resolutions and IP-to-domain mappings, indicating long-term infrastructure use by the threat group.
- Analysis of WHOIS data found public and historical email connections, helping expand the IoC list and detect further malicious domains and IPs linked to UNC5174.
MITRE Techniques
- [T1071] Application Layer Protocol – UNC5174 used open-source reverse shell tools such as “SUPERSHELL” and “VShell” for command and control (“…using the open-source reverse shell tool named ‘SUPERSHELL’…”).
- [T1588] Obtain Capabilities – The group incorporated new tools SNOWLIGHT and VShell to enhance their attack infrastructure (“In January 2025, they used a new open-source tool and command-and-control infrastructure dubbed ‘SNOWLIGHT’… began using another tool dubbed ‘VShell.’”).
- [T1598] Phishing for Information – Email-connected domains and historical email addresses were identified, pointing to reconnaissance and operational support activities (“…three domains had 15 email addresses in their records…”).
Indicators of Compromise
- [Domains] UNC5174 campaign-related domains – c1oudf1are[.]com, bing-server[.]com, ciscocdn[.]com, plus 10 more domains linked to malicious activity.
- [IP Addresses] Threat actor infrastructure IPs – 104[.]18[.]52[.]126 (historical DNS resolution), 45[.]43[.]208[.]31 (suspected victim connection), and 10 additional weaponized IPs.