Wazuh Ruleset as Code (RaC) enables security teams to manage Wazuh detection rulesets using DevOps practices such as version control and CI/CD pipelines for automated deployment. This approach improves collaboration, change tracking, and minimizes manual errors by automating ruleset integration and validation processes. #WazuhRaC #DetectionEngineeringAsCode
Keypoints
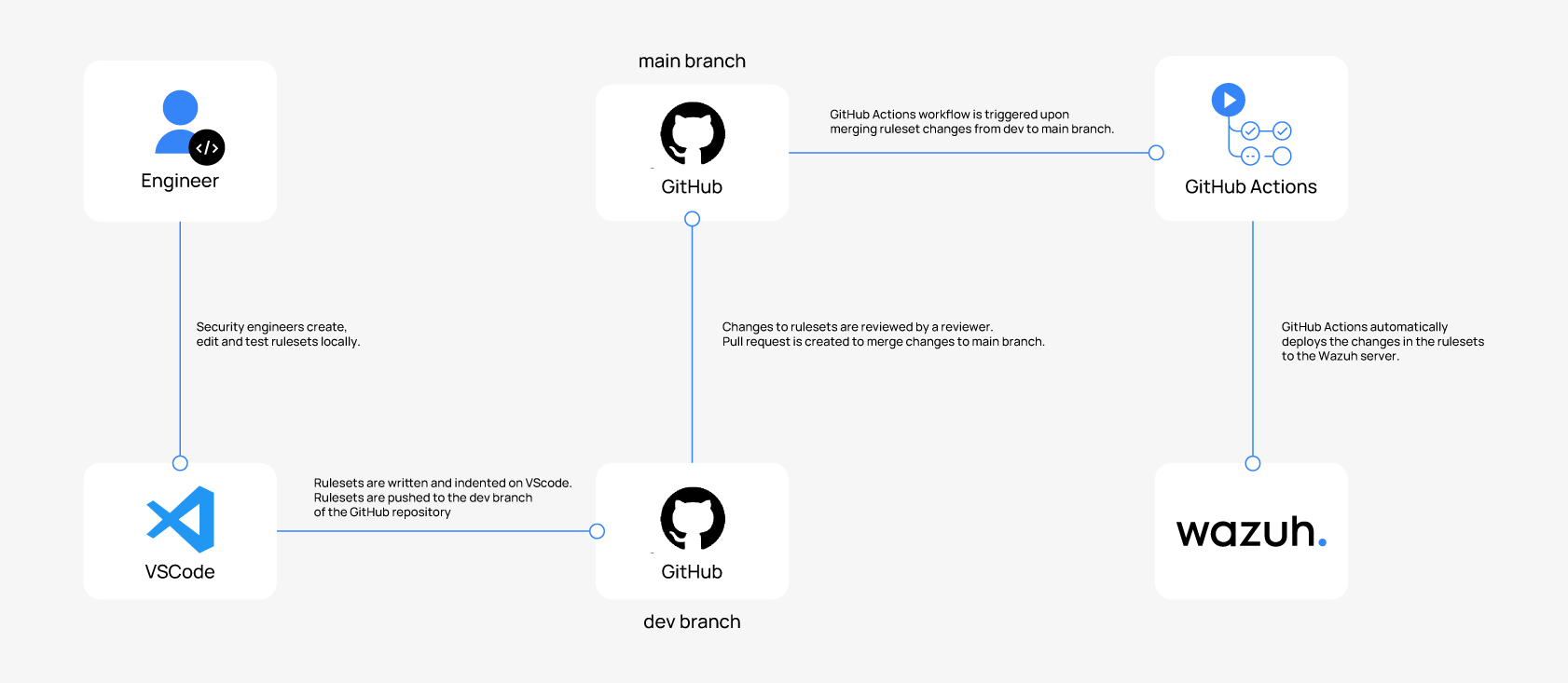
- Wazuh RaC leverages infrastructure as code principles to manage threat detection rulesets via Git version control and CI/CD pipelines.
- Security engineers develop and test rulesets locally in directories /var/ossec/etc/decoders and /var/ossec/etc/rules, which are tracked by Git.
- Changes are pushed to a dev branch on GitHub, peer-reviewed via pull requests, and merged into the main branch to trigger automated deployment workflows.
- GitHub Actions workflows automate rule synchronization to Wazuh server, file permission adjustments, and restart the Wazuh manager service.
- A Python script and corresponding GitHub workflow ensure rule ID conflicts are detected and prevented during pull request reviews.
- The setup requires an Ubuntu 24 server with Wazuh 4.12.0, Git 2.34.1, and VSCode IDE on any client endpoint.
- Error handling within CI/CD workflows helps identify issues such as SSH connection errors or syntax problems in rulesets before deployment.
MITRE Techniques
- [T1609] Container Administration Command – GitHub Actions workflow automates deployment commands to manage configuration files and restart the Wazuh manager: ‘git pull origin main’, ‘chown’, ‘chmod’, and ‘systemctl restart wazuh-manager’.
- [T1598] Phishing for Information – Use of SSH keys and SSH port configuration to securely authenticate and remotely manage Wazuh servers as part of CI/CD automation.
- [T1566] Phishing – Creation and management of SSH key pairs for secure authentication of automated workflows to the Wazuh server platform.
Indicators of Compromise
- [File Hashes] Rule and decoder XML files – Examples include demo_decoder.xml and demo_rule.xml representing custom rulesets used in Wazuh deployments.
- [SSH Keys] SSH authentication keys for secure access to Ubuntu endpoint hosting the Wazuh server – stored with .pem extension for workflow use.
- [IP Addresses] Public IP addresses or DNS names of Ubuntu endpoints hosting Wazuh components – used as host values for GitHub Actions workflows.
Read more: https://wazuh.com/blog/wazuh-ruleset-as-code-rac/