Taiwan MacKay Memorial Hospital was hit by the CrazyHunter ransomware, which used a USB-borne infection vector to deploy its payload through exploited vulnerable drivers and privileged escalation techniques. CrazyHunter targets primarily Taiwanese organizations in healthcare, technology, and manufacturing sectors by leveraging publicly available tools and methods such as Bring Your Own Vulnerable Driver (BYOVD) and SharpGPOAbuse. #CrazyHunter #MacKayMemorialHospital #BYOVD
Keypoints
- On February 9, 2025, Taiwan MacKay Memorial Hospital suffered a major ransomware attack affecting over 500 computers at two campuses.
- The attack was initiated via an infected USB device introducing CrazyHunter ransomware using BYOVD techniques exploiting the zam64.sys driver to disable endpoint protection.
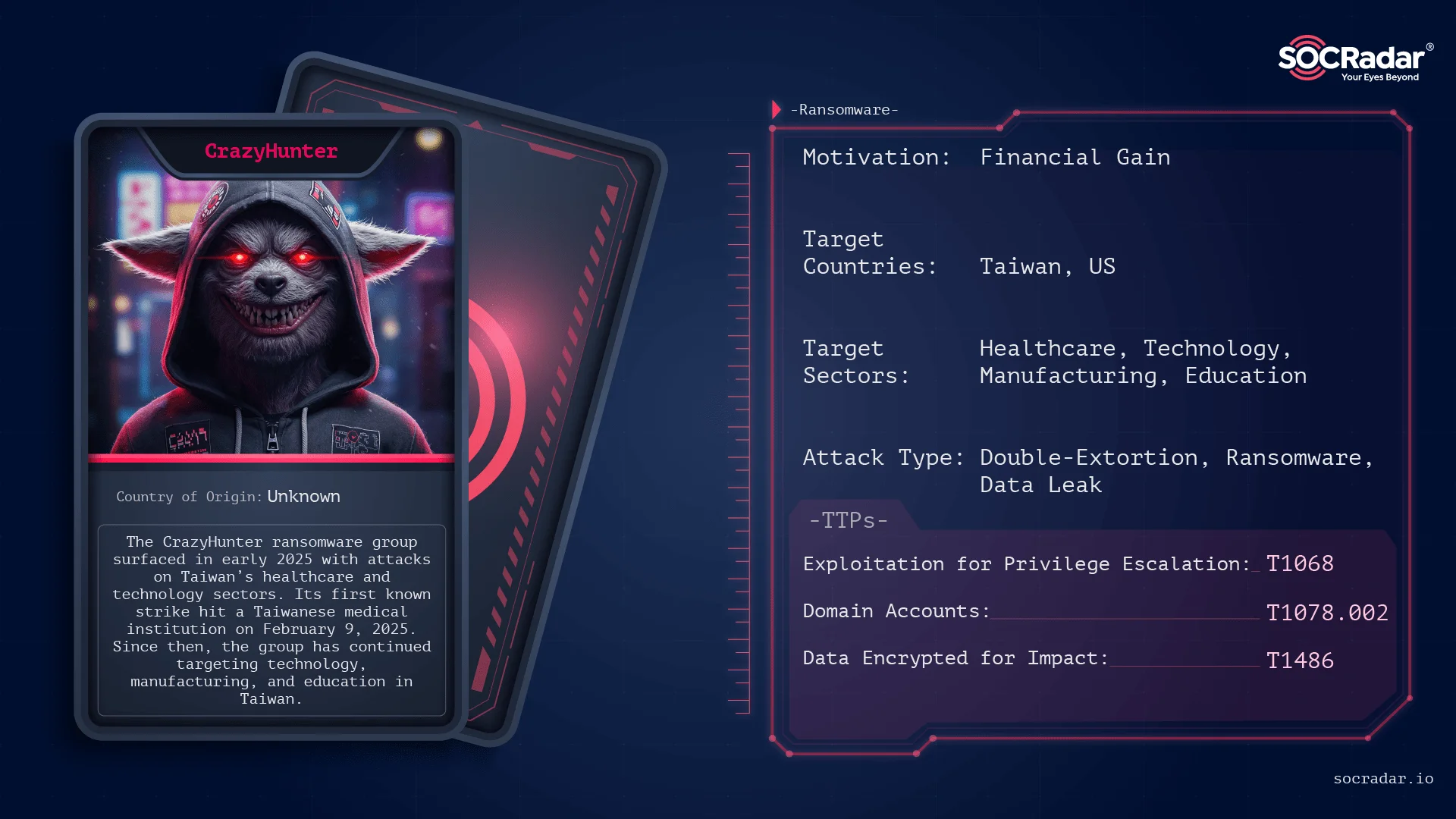
- CrazyHunter ransomware is built using the publicly available Prince Ransomware builder and primarily targets Taiwanese organizations in healthcare, technology, manufacturing, and education.
- It employs privilege escalation through SharpGPOAbuse, lateral movement, defense evasion via vulnerable drivers, and encrypts files with ChaCha20 and ECIES, appending the .Hunter extension.
- The group runs a data leak site to pressure victims and has a strong geographic focus on Taiwan, with 90% of victims based there.
- Key mitigation strategies include enforcing multi-factor authentication, endpoint protection with driver enforcement, restricting Group Policy modification, and robust backup practices.
- SOCRadar offers advanced threat intelligence and monitoring solutions to detect, analyze, and defend against CrazyHunter ransomware campaigns.
MITRE Techniques
- [T1059.003] Windows Command Shell – Used via batch scripts to coordinate execution of ransomware components (‘A batch script coordinates the launch of multiple components’).
- [T1547] Boot or Logon AutoStart Execution – Persistence through drivers and services like crazyhunter.sys and ZammOcide service (‘Driver loaded at boot via crazyhunter.sys’).
- [T1068] Exploitation for Privilege Escalation – Exploits vulnerable driver zam64.sys to escalate privileges (‘Uses zam64.sys…to raise its privileges’).
- [T1484.001] Group Policy Modification – Abuse of GPOs via SharpGPOAbuse to deploy malicious scripts and escalate privileges (‘Exploits Group Policy Objects (GPOs) where attackers have edit rights’).
- [T1562.001] Disable or Modify Tools – Disable Microsoft Defender and AV products using vulnerable drivers (‘Uses zam64.sys…to disable Microsoft Defender, Avira, Other EDR/AV products’).
- [T1211] Exploitation for Defense Evasion – Abusing legitimate drivers to evade defenses (‘BYOVD…exploited a legitimate driver zam64.sys from Zemana AntiMalware’).
- [T1083] File and Directory Discovery – Discovery to avoid encrypting critical system paths and file types (‘Whitelisting strategy: The ransomware avoids encrypting critical system directories and certain file types’).
- [T1570] Lateral Tool Transfer – Uses tools to move laterally through the network (‘Allows deployment of malicious scripts across the domain’).
- [T1005] Data from Local System – Collects data locally before exfiltration (‘file.exe: A Go-based utility functioning in two modes including monitoring file changes’).
- [T1048] Exfiltration Over Alternative Protocol – Uses custom tools and web server on port 9999 for exfiltration (‘Runs a web server on port 9999’).
- [T1486] Data Encrypted for Impact – Uses ChaCha20 and ECIES encryption with .Hunter extension for files (‘Encrypted files end with .Hunter extension’).
- [T1078.002] Domain Accounts – Uses weak Microsoft Active Directory accounts for access (‘Try to access Microsoft AD accounts using weak passwords’).
Indicators of Compromise
- [File Hashes] Various malware components used by CrazyHunter – go.exe, bb.exe, hunter.exe, crazyhunter.sys, av-1m.exe, and more hashes such as 6bb811e2fbb498f466980a176caefbfb, 5cc2523816a184fed135f0119756c337, 7f3d07220529742bdc1827186b73666a.
- [File Names] Ransomware and auxiliary files – crazyhunter.exe, crazyhunter.sys, hunter.exe, go.exe, av-1m.exe, bb.exe, a.ashx (Webshell), tunnel.aspx (SOCKS tunnel).
- [Domains/Communication] Cobalt Strike beacon infrastructure including graph.microsoft.com and DevTunnels for domain-fronting and command-and-control.
- [File Extensions] Encrypted files appended with .Hunter extension and ransom note named “Decryption Instructions.txt”.
Read more: https://socradar.io/dark-web-profile-crazyhunter-ransomware/