In May 2025, eSentire’s Threat Response Unit detected a sophisticated attack targeting a U.S. accounting firm using the Ghost Crypt crypter to deliver PureRAT malware via a social engineering phishing tactic. The malware employed advanced obfuscation, process injection, and targeted cryptocurrency-related browser extensions and applications to maintain persistence and gather sensitive data. #PureRAT #GhostCrypt #eSentireTRU
Keypoints
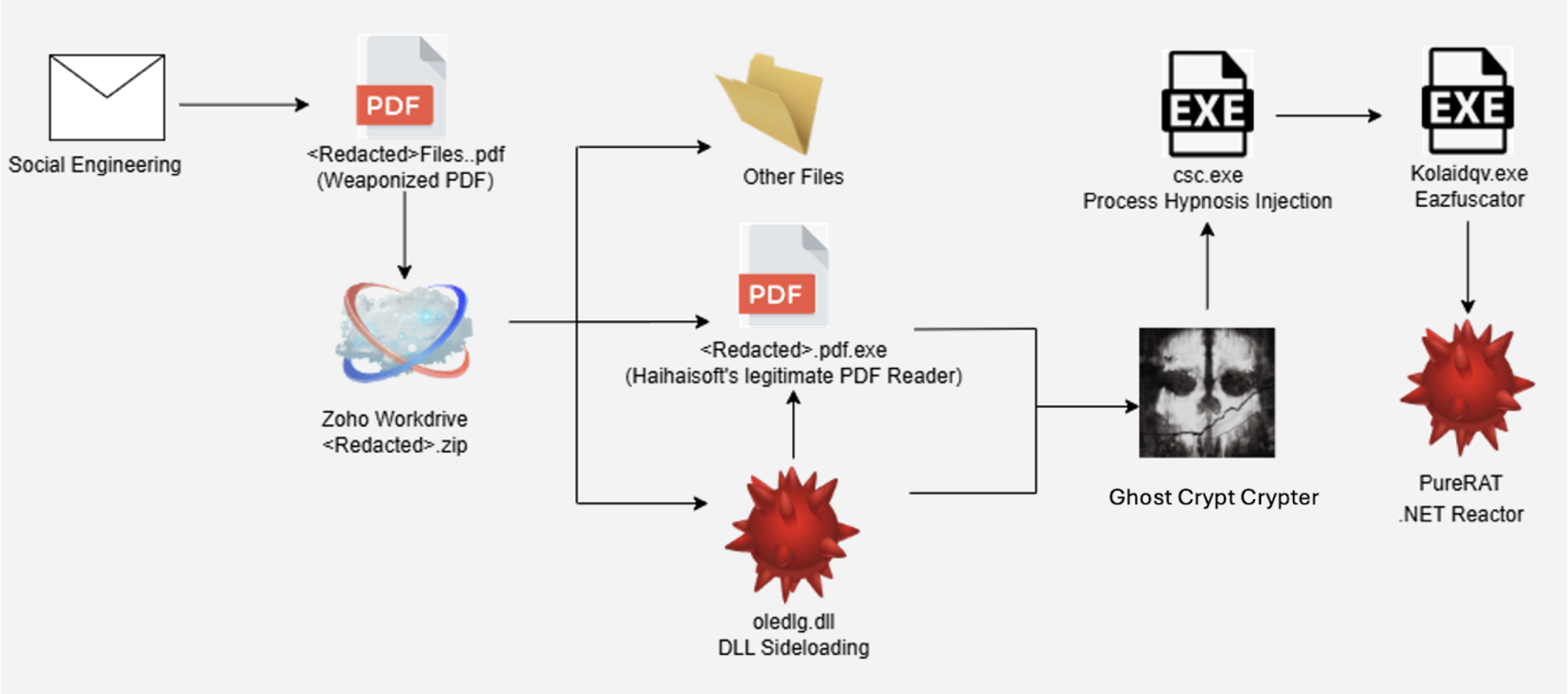
- An attack targeting a U.S. accounting firm used social engineering with a malicious PDF linked to a Zoho WorkDrive folder to deliver malware.
- The newly emerged Ghost Crypt crypter was used to encrypt and sideload a malicious DLL, injecting PureRAT into the legitimate Windows process csc.exe.
- Ghost Crypt uses a custom ChaCha20 variant and “Process Hypnosis” injection to evade detection and antivirus solutions.
- PureRAT, a Remote Access Trojan linked to PureCoder, was delivered and loaded via obfuscated .NET binaries, using AES-256 decryption and GZIP decompression techniques.
- Malware targeted Chromium-based browsers’ cryptocurrency wallet extensions and desktop crypto applications, focusing on data theft related to crypto assets.
- Persistence was established by registry run keys and thread execution state API calls to prevent system sleep during operations.
- The TRU emphasized user caution regarding urgent, impersonation-based attacks and recommended verification of links, updating security software, and using EDR solutions.
MITRE Techniques
- [T1566] Phishing – Initial access was gained via social engineering where an attacker impersonated a client and sent a PDF with a malicious link to download malware (‘security analysts described the attacker posing as a new client and sending a PDF with a link to a Zoho WorkDrive folder’).
- [T1055] Process Injection – PureRAT was injected into csc.exe using “Process Hypnosis,” a debugging-based injection technique (‘calls the CreateProcessW API with DEBUG_ONLY_THIS_PROCESS flag to start the process in debug mode and injects code’).
- [T1036] Masquerading – The malicious DLL was renamed and sideloaded through a legitimate program hpreader.exe to evade detection (‘used hpreader.exe to sideload the malicious DLL renamed as CriticalUpdater0549303.dll’).
- [T1112] Modify Registry – Persistence was established by creating registry run keys to launch the DLL at user login (‘the DLL creates a registry entry to ensure launch on each login’).
- [T1480] Execution Guardrails – The malware used SetThreadExecutionState API to prevent system sleep or display off during execution (‘malware uses API flags to keep the system awake during operations’).
- [T1083] File and Directory Discovery – The malware scanned the system for cryptocurrency wallets, messaging apps, and browser extensions (‘targeted extensions in 30+ Chromium-based browsers and desktop crypto wallet installation folders’).
- [T1071] Application Layer Protocol – Communication to C2 servers involved sending collected sensitive data including system details and crypto info (‘sends extensive system and user data to the Command and Control server’).
Indicators of Compromise
- [File Hashes] Malicious DLL and executables – Examples include “CriticalUpdater0549303.dll” (malicious DLL renamed from oledlg.dll), and “1040_Scan___Files_Organizer2024__Tax_Organizer___2024.pdf.exe”.
- [Domains] Malicious download link – zohoexternal[.]com used as a cloud-hosted malicious payload delivery platform.
- [Registry Keys] Persistence mechanism – Registry Run Key entry created to launch DLL on user login (specific key names redacted in article).
- [Certificates] Embedded X.509 certificate – Includes serial number 1071913861427099792278749970483054303 with SHA256 fingerprint cbbda2edde38162e49f7578512c015640392342a26ea0e5cd90705bb66a7ba81.
Read more: https://www.esentire.com/blog/ghost-crypt-powers-purerat-with-hypnosis