Between March and June 2025, multiple China-aligned threat actors conducted targeted phishing campaigns against Taiwan’s semiconductor industry, focusing on espionage and intelligence gathering. The campaigns employed custom malware like Voldemort and HealthKick, leveraging sophisticated delivery methods including DLL sideloading and adversary-in-the-middle phishing kits. #UNK_FistBump #UNK_DropPitch #Voldemort #HealthKick #TA415 #UNK_SparkyCarp
Keypoints
- Between March and June 2025, three China-aligned threat actors targeted the Taiwanese semiconductor industry using spearphishing campaigns focused on espionage.
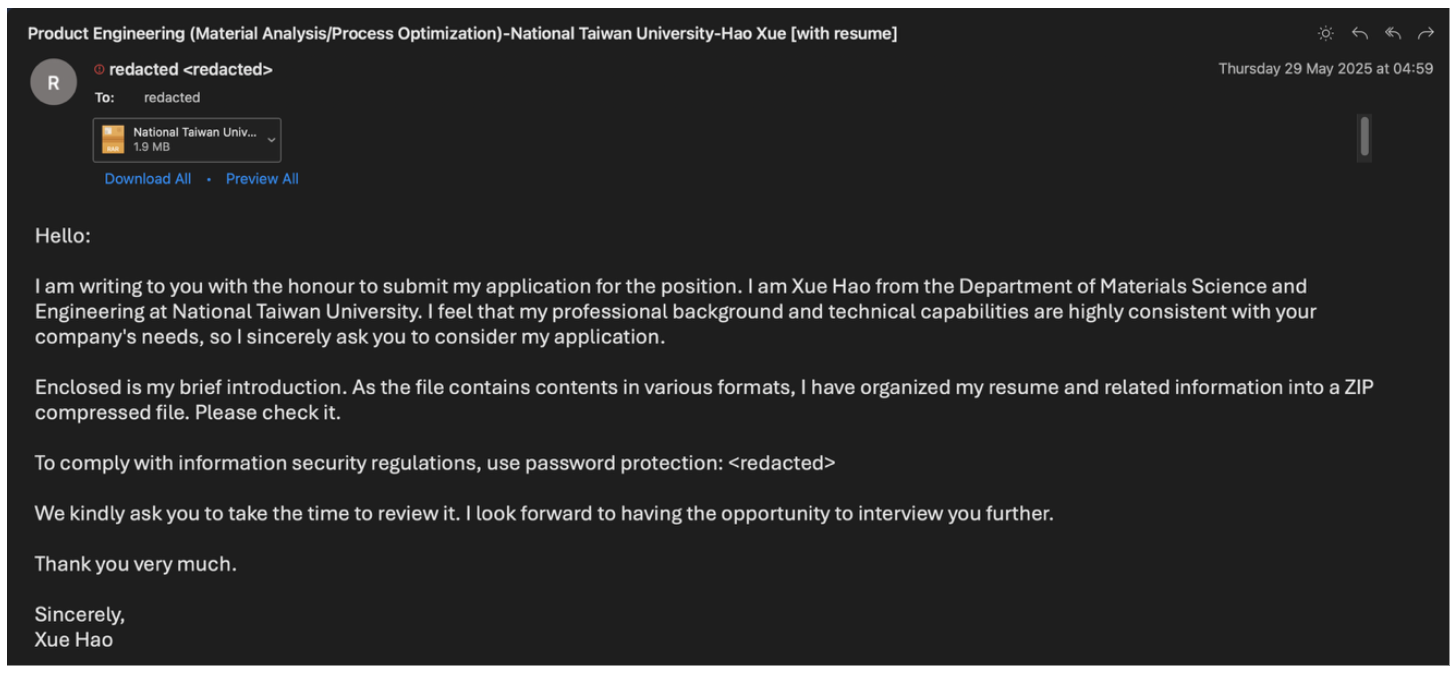
- UNK_FistBump deployed Cobalt Strike Beacon and a custom backdoor called Voldemort through employment-themed phishing emails using compromised university accounts.
- UNK_DropPitch targeted investment analysts with phishing emails delivering a custom backdoor named HealthKick and a TCP reverse shell, using scheduled tasks for persistence.
- UNK_SparkyCarp employed a custom adversary-in-the-middle (AiTM) phishing kit for credential theft against Taiwanese semiconductor firms.
- The campaigns utilized sophisticated infection chains involving DLL sideloading, encrypted payloads, and Google Sheets or VPS-based command and control servers.
- Evidence suggests some malware overlaps with known China state-sponsored actor TA415, though UNK_FistBump is tracked as a distinct cluster due to differences in TTPs.
- Infrastructure analysis revealed use of Russian VPS providers, SoftEther VPN servers, and TLS certificates historically associated with Chinese state-sponsored malware SideWalk.
MITRE Techniques
- [T1566] Phishing – Employed spearphishing emails disguised as employment applications or financial collaboration requests to deliver malware payloads (“phishing campaigns targeting… employment-themed phishing campaigns”).
- [T1204] User Execution – Executed malicious scripts and executables contained in password-protected archives and PDFs (“Execution of the first LNK file named… runs a VBS script”).
- [T1574] Hijack Execution Flow – DLL sideloading used to load malicious DLLs via signed executables (“…signed executable javaw.exe, which is vulnerable to DLL-sideloading”).
- [T1105] Ingress Tool Transfer – Downloaded malicious files from URLs hosted on file-sharing services and actor-controlled domains (“PDF attachments contained URLs leading to an archive file hosted on… Zendesk or Filemail”).
- [T1071] Application Layer Protocol – Used Google Sheets and FakeTLS protocol for command and control communication (“Voldemort backdoor, which uses Google Sheets for command and control”).
- [T1053] Scheduled Task/Job – Established persistence by creating scheduled tasks on infected hosts (“scheduled task named SystemHealthMonitor is created to execute… every five minutes”).
- [T1110] Brute Force – Conducted credential phishing using custom adversary-in-the-middle phishing kits (“credential phishing campaign using a custom adversary-in-the-middle (AITM) framework”).
Indicators of Compromise
- [IP Address] Command and control servers – 166.88.61[.]35 (Cobalt Strike C2), 82.118.16[.]72 (HealthKick C2), 80.85.156[.]234 (Intel EMA C2)
- [URLs] Malware delivery and C2 – hxxps://api[.]moctw[.]info/Intro.pdf, hxxps://brilliant-bubblegum-137cfe[.]netlify[.]app/files/Introduction%20Document.zip, hxxps://sheets[.]googleapis[.]com:443/v4/spreadsheets/1z8ykHVYh9DF-b_BFDA9c4Q2ojfrgl-fq1v797Y5576Y
- [Domains] Credential phishing and tracking – accshieldportal[.]com (phishing domain), ema.moctw[.]info (C2 domain), acesportal[.]com (tracking pixel domain)
- [File Hashes] Malware samples – 1a2530010ecb11f0ce562c0db0380416a10106e924335258ccbba0071a19c852b (協助確認.rar), 7bffd21315e324ef7d6c4401d1bf955817370b65ae57736b20ced2c5c08b9814 (Intro.zip), 82ecfe0ada6f7c0cea78bca2e8234241f1a1b8670b5b970df5e2ee255c3a56ef (CiscoSparkLauncher.dll)
- [Emails] Used for malware delivery – john.doe89e@gmail[.]com, amelia_w_chavez@proton[.]me