Since late 2024, the CL-STA-1020 threat group has targeted Southeast Asian government entities using a novel Windows backdoor named HazyBeacon that communicates via AWS Lambda URLs for command and control. The campaign highlights advanced techniques such as DLL sideloading and data exfiltration through legitimate cloud services like Google Drive and Dropbox. #HazyBeacon #CL-STA-1020 #AWSLambdaURLs
Keypoints
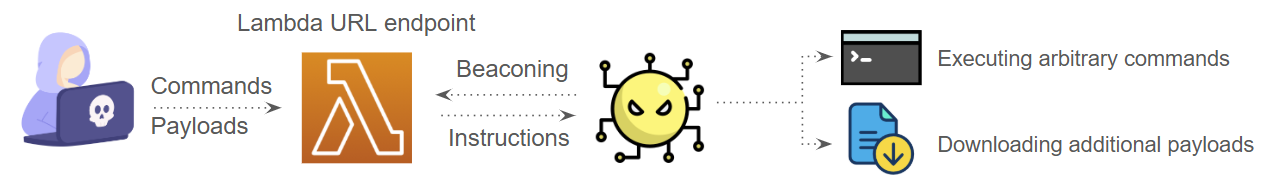
- Researchers identified a new Windows backdoor called HazyBeacon that uses AWS Lambda URLs as a covert command and control channel.
- The CL-STA-1020 threat actor targets Southeast Asian governmental entities to collect sensitive information related to tariffs and trade disputes.
- The malware is deployed via DLL sideloading by replacing the legitimate mscorsvc.dll used by the Windows service mscorsvw.exe.
- Persistence is achieved through the creation of a Windows service named msdnetsvc that loads the malicious DLL after reboot.
- Data exfiltration is conducted through legitimate cloud services including Google Drive and Dropbox, blending with normal network traffic to evade detection.
- The backdoor downloads multiple payloads including file collectors and custom uploaders to archive and transmit stolen data.
- Palo Alto Networks provides detection and mitigation through Advanced WildFire, Cortex XDR, XSIAM, and Cortex Cloud solutions, as well as the Unit 42 Cloud Security Assessment service.
MITRE Techniques
- [T1070] Indicator Removal on Host – The threat actor executed cleanup commands to delete archive files and payloads to remove evidence of their activity (“They deleted the archive files they had created, along with all the payloads.”)
- [T1543] Create or Modify System Process – Persistence was established by creating the Windows service msdnetsvc to load the malicious DLL (“the threat actor created a Windows service named msdnetsvc, which ensured that the HazyBeacon DLL would be loaded even after rebooting the system.”)
- [T1176] Browser Extensions – Use of cloud storage services like Google Drive and Dropbox for exfiltration to blend with normal traffic (“The threat actor also used Google Drive and Dropbox as exfiltration channels, blending in with normal network traffic.”)
- [T1218] Signed Binary Proxy Execution – DLL sideloading was leveraged to deploy the backdoor by substituting mscorsvc.dll loaded by mscorsvw.exe (“They planted a malicious DLL in C:Windowsassemblymscorsvc.dll, alongside a legitimate Windows executable, mscorsvw.exe.”)
- [T1567] Exfiltration Over Web Service – Data was exfiltrated using Google Drive and Dropbox upload tools (“the malware used utilities to upload the files to Google Drive and Dropbox.”)
Indicators of Compromise
- [File Hash] backdoor DLL – 4931df8650521cfd686782919bda0f376475f9fc5f1fee9d7cf3a4e0d9c73e30 (C:Windowsassemblymscorsvc.dll)
- [File Hash] Google Drive uploader variants – d20b536c88ecd326f79d7a9180f41a2e47a40fcf2cc6a2b02d68a081c89eaeaa, 304c615f4a8c2c2b36478b693db767d41be998032252c8159cc22c18a65ab498, f0c9481513156b0cdd216d6dfb53772839438a2215d9c5b895445f418b64b886
- [File Hash] Dropbox file uploader – 3255798db8936b5b3ae9fed6292413ce20da48131b27394c844ecec186a1e92f
- [File Hash] File collector – 279e60e77207444c7ec7421e811048267971b0db42f4b4d3e975c7d0af7f511e (C:ProgramDataigfx.exe)
- [File Hash] Google Drive connect tool – d961aca6c2899cc1495c0e64a29b85aa226f40cf9d42dadc291c4f601d6e27c3 (C:ProgramDataGoogleGet.exe)
Read more: https://unit42.paloaltonetworks.com/windows-backdoor-for-novel-c2-communication/