The DoNot APT group, active since 2016 and linked to India, has targeted governmental and diplomatic entities using sophisticated multi-stage malware campaigns involving spear-phishing and custom malware such as LoptikMod. A recent campaign against a European foreign affairs ministry utilized malicious Google Drive links and scheduled tasks to maintain persistence and exfiltrate sensitive data. #DoNotAPT #LoptikMod #TrellixAdvancedResearchCenter
Keypoints
- DoNot APT group (AKA APT-C-35, Mint Tempest) targets government, military, and diplomatic organizations, primarily in South Asia and increasingly Europe.
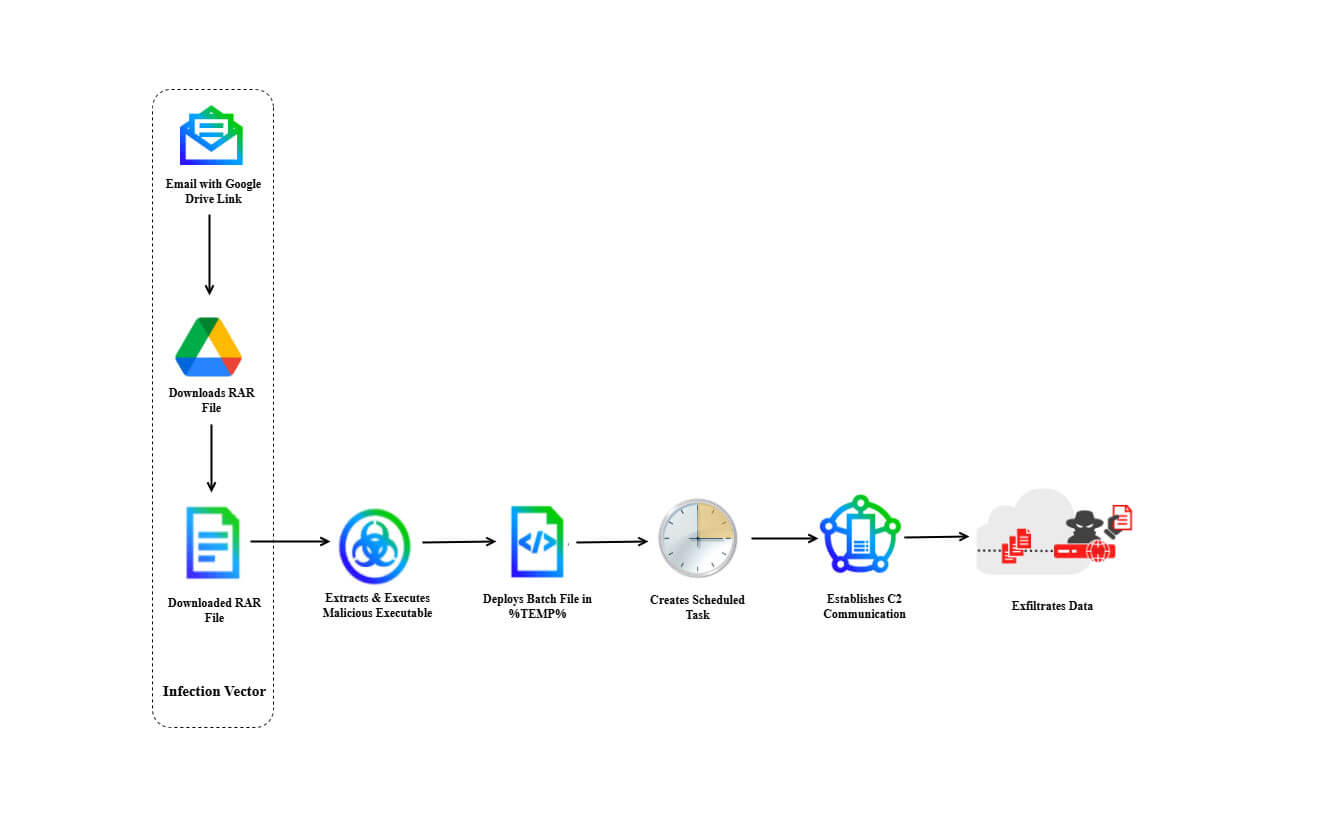
- Their recent campaign used spear-phishing emails with Google Drive links delivering password-protected RAR archives containing the LoptikMod malware.
- Infection involves execution of notflog.exe, creation of batch files, and scheduled tasks named “PerformTaskMaintain” and “MicorsoftVelocity” for persistence.
- LoptikMod malware employs obfuscation techniques including binary encoded strings, selective packing, minimal import tables, and anti-VM checks using x86 “IN” instruction.
- Command and Control communications use HTTPS POST requests to the domain totalservices[.]info, aiming to exfiltrate system data like usernames, hostnames, and processor IDs.
- Trellix Advanced Research Center blocked the initial spear-phishing email and identified Indicators of Compromise such as phishing email address, malicious URLs, malware hashes, and C2 server IP.
- Recommended defenses include enhanced email security, network traffic monitoring, endpoint detection and response, application whitelisting, and threat intelligence sharing.
MITRE Techniques
- [T1566.002] Phishing: Spearphishing Link – Attackers used an email containing a malicious Google Drive link (drive[.]usercontent.google[.]com/download?id=1t-fBZBgVtW_S81qYGn9loubWZwIXjI_T).
- [T1204.002] User Execution: Malicious File – Victim executed notflog.exe extracted from SyClrLtr.rar archive.
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – Executed batch files djkggosj.bat and sfs.bat for subsequent infection stages.
- [T1053.005] Persistence: Scheduled Task – Created scheduled tasks “PerformTaskMaintain” and “MicorsoftVelocity” to ensure malware persistence and execution.
- [T1497.001] Defense Evasion: Virtualization/Sandbox Evasion – Used x86 “IN” instruction to detect and evade virtual environments.
- [T1027.013] Defense Evasion: Obfuscated Files or Information – Encoded ASCII strings and selective packing in notflog.exe to hinder analysis.
- [T1071.001] Command and Control: Application Layer Protocol – Communicated with C2 server totalservices[.]info using HTTPS POST requests.
- [T1082] Discovery: System Information Discovery – Collected system details including CPU model, OS name, username, hostname, and ProcessorID.
- [T1083] Discovery: File and Directory Discovery – Searched and created directories such as %localappdata%TEMPFROX for staging.
- [T1041] Exfiltration: Exfiltration Over C2 Channel – Exfiltrated data via HTTPS POST requests to the C2 server endpoint.
Indicators of Compromise
- [Email Sender Address] Spear-phishing source – int[.]dte[.]afd[.]1@gmail[.]com
- [Email Subject] Lure used in phishing email – “Italian Defence Attaché Visit to Dhaka, Bangladesh”
- [URL] Malicious download link – drive.usercontent.google[.]com/download?id=1t-fBZBgVtW_S81qYGn9loubWZwIXjI_T
- [File Name] Password-protected archive and malware executables – SyClrLtr.rar, notflog.exe
- [File Hash – SyClrLtr.rar] SHA256 hash – 5317f22c60a4e08c4caa28bc84f653b1902fa082d2d1d7fcf2cd0ce1d29798d6
- [File Hash – notflog.exe] SHA256 hash – 4d036e0a517774ba8bd31df522a8d9e327202548a5753e5de068190582758680
- [C2 Domain] Command and control server domain – totalservices[.]info
- [C2 IP Address] Command and control server IP – 64[.]52[.]80[.]252
- [Scheduled Task Names] Persistence mechanism – PerformTaskMaintain, MicorsoftVelocity