The article analyzes the advanced Android packer named Ducex, used by the Triada malware to obfuscate and encrypt its payload, complicating detection and analysis. It reveals Ducex’s use of modified RC4 encryption, self-debugging, anti-debugging techniques, and payload storage within the classes.dex file. #Triada #Ducex #libducex #SM4
Keypoints
- Triada malware uses Ducex, an advanced Chinese Android packer, to conceal its payload and hinder analysis.
- Ducex encrypts functions with a modified RC4 algorithm and all strings with a sequential XOR using a changing 16-byte key.
- The packer enforces APK signature verification and employs self-debugging via fork and ptrace to prevent external debugging.
- Ducex actively detects tools like Frida, Xposed, and Substrate, terminating execution if identified.
- The Triada payload is embedded within the Ducex classes.dex file in a large additional section after the main code to avoid detection.
- Ducex uses both modified RC4 and Chinese SM4 encryption algorithms to decrypt payload modules stored inside the APK.
- The packer implements heavy control flow obfuscation and dynamic function decryption to complicate static and dynamic analysis.
MITRE Techniques
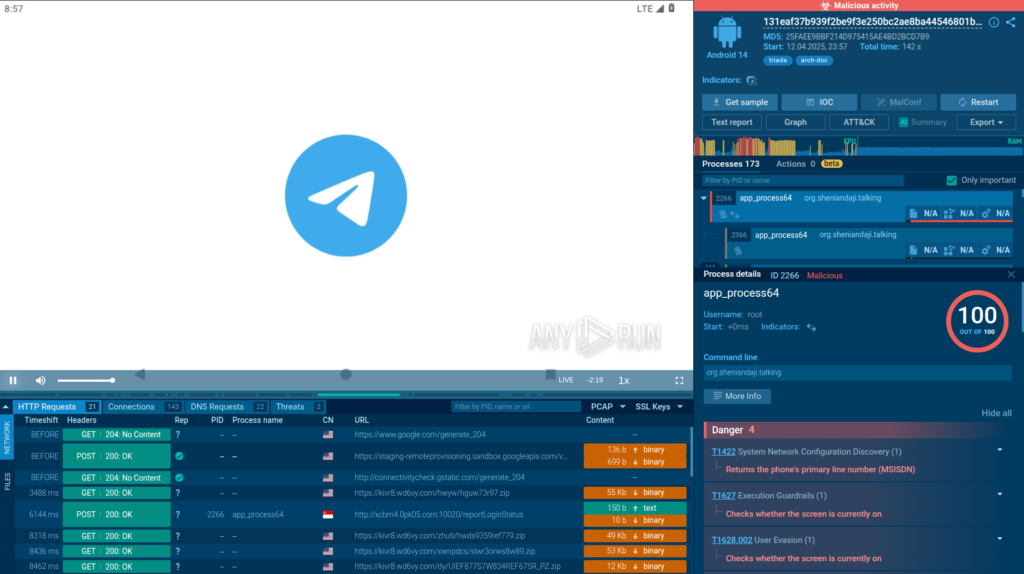
- [T1036] Masquerading – The packer uses a fake Telegram app to disguise the Triada malware payload (‘sample in question was embedded in a fake Telegram app’).
- [T1553] Subvert Trust Controls – Ducex performs APK signature verification and terminates execution if signatures do not match, preventing tampering (‘app checks the APK signature and terminates if it doesn’t match’).
- [T1620] Reflective Code Loading – Triada stores its payload as additional dex modules inside classes.dex which are decrypted and executed at runtime (‘stored within Ducex’s own classes.dex file in a large, additional section’).
- [T1218] Signed Binary Proxy Execution – The packer uses library “libducex.so” with encrypted functions loaded dynamically (‘most methods of this class are native, and they are implemented in the “libducex.so” library’).
- [T1064] Scripting – Custom decryption scripts and native code functions are used to decode encrypted functions and strings (‘function decryption occurs in .init_proc’).
- [T1622] Debugger Detection – Ducex detects debugging tools like Frida, Xposed, and Substrate and terminates the process upon detection (‘if any of these strings are found in memory, the process terminates execution’).
- [T1059] Command and Control – Triada communicates with characteristic domains identified during sandbox analysis (‘recognizing the characteristic domains it communicated with’).
- [T1055] Process Injection – Self-debugging is implemented by parent and child processes monitoring each other using ptrace and fork system calls (‘parent process uses fork and ptrace to block external tracing’).
Indicators of Compromise
- [File Hashes] Malicious APK samples – MD5: 25faee9bbf214d975415ae4bd2bcd7b9, SHA256: 131eaf37b939f2be9f3e250bc2ae8ba44546801b5ca6268f3a2514e6a9cb8b5c
- [File Name] Malicious file – 131eaf37b939f2be9f3e250bc2ae8ba44546801b5ca6268f3a2514e6a9cb8b5c.apk
- [Domain] C2 communication domains – characteristic domains contacted by Triada identified during sandbox analysis (not explicitly named but referenced)
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/ducex-packer-analysis/