The U.S. Department of Justice seized 114 domains linked to a major information-stealing campaign using Lumma Stealer. Analysis revealed the domains were recently created, primarily registered through PDR and originating mostly from Russia, with many domain and IP indicators confirmed as malicious. #LummaStealer #DOJ #PDR
Keypoints
- The DOJ seized 114 domains related to an information-stealing campaign employing Lumma Stealer on May 21, 2025.
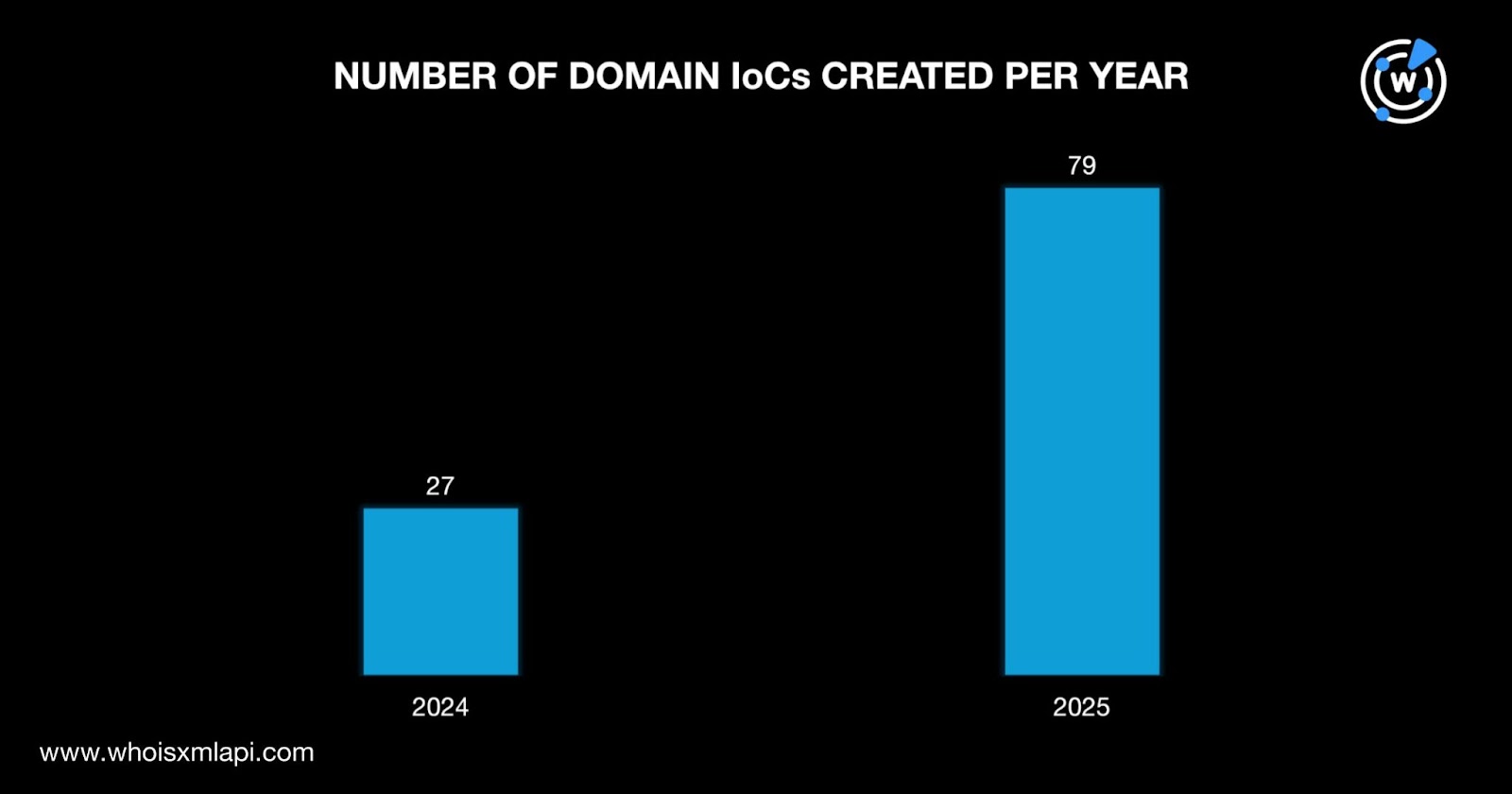
- 106 of these domains had active WHOIS records, mostly created between 2024 and 2025, indicating recent weaponization.
- PDR Registrar managed 56 of the 106 domains; other registrars included MarkMonitor and Dynadot among others.
- Russia was the dominant registrant country with 46 domains, followed by the U.S., Malaysia, Sweden, and Germany.
- First Watch data showed 28 of the 114 domains were detected as malicious on average 97 days before public disclosure.
- Eight additional .digital domains related to ferromny.digital shared WHOIS details and were flagged as potentially malicious by VirusTotal.
- DNS data revealed 265 unique domain-to-IP resolutions with 68 unique IPs identified before May 2025, 62 of which were malicious.
- Active IP addresses resolving domains were mainly hosted in the U.S. across Amazon, Linode, and Microsoft ISPs.
MITRE Techniques
- [T1071] Application Layer Protocol – Domains and IPs used for command and control, as highlighted by the malicious resolutions and attack activity (‘…was associated with malware distribution, generic threats, command and control (C&C), and attacks.’)
- [T1588] Obtain Capabilities – The creation and registration of new domains between 2024-2025 to support the Lumma Stealer campaign (‘…created between 2024 and 2025, making them relatively new when they were weaponized for attacks.’)
Indicators of Compromise
- [Domain ] 114 domains seized by DOJ including ferromny.digital, tv-serial.digital, and 112 others associated with Lumma Stealer attacks
- [IP Address ] 68 unique IPs resolving malicious domains before May 2025 including 52.26.80.133 linked to malware distribution and C&C
- [Registrar ] PDR (56 domains), MarkMonitor, Dynadot, Web Commerce Communications, Stichting Registrar of Last Resort Foundation, and Gandi managing the identified domains
- [VirusTotal Detection ] Eight additional .digital domains detected as malicious by up to 16 VirusTotal engines, e.g., tv-serial.digital
Read more: https://circleid.com/posts/shining-the-dns-spotlight-on-lumma-stealer