A critical vulnerability, CVE-2025-53104, affecting the gluestack-ui GitHub repository can be exploited to execute arbitrary commands on GitHub Actions runners, leading to secret exfiltration and repository compromise. This vulnerability was patched on June 13, 2025, but poses serious risks to NPM package integrity and confidentiality. #CVE202553104 #gluestack #GitHubActions
Keypoints
- The Sysdig Threat Research Team discovered CVE-2025-53104, a critical vulnerability in the gluestack-ui GitHub repository that scored 9.1 on the CVSS v3.1 scale.
- This vulnerability allows attackers to inject malicious payloads into GitHub Discussion titles or bodies, triggering arbitrary command execution on GitHub Actions runners.
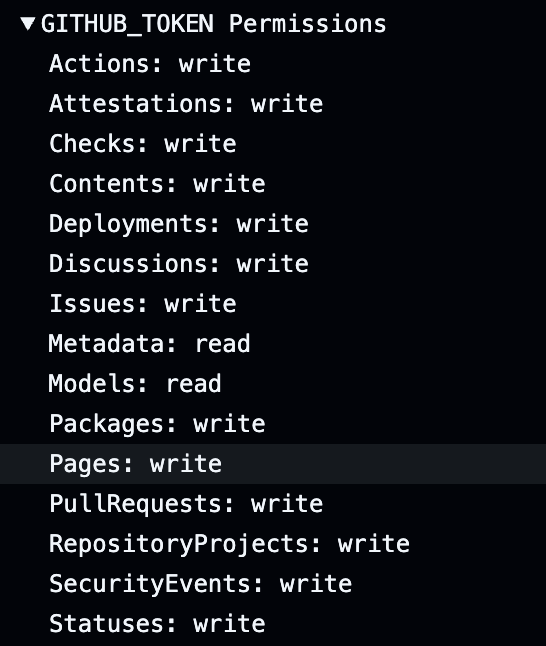
- Exploitation can lead to exfiltration of sensitive secrets like the GITHUB_TOKEN, unauthorized repository modification, and compromised NPM package releases.
- The vulnerability is distinct from previous supply chain incidents caused by stolen personal access tokens but can produce similar impacts.
- A patch fixing the vulnerability was released by gluestack maintainers on June 13, 2025, shortly after responsible disclosure by the Sysdig TRT.
- Secure handling of user-controlled GitHub Actions inputs via environment variables is recommended to prevent code injection attacks.
- The vulnerability underscores the growing threat of supply chain attacks targeting CI/CD workflows and package managers like NPM.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Attackers exploit command injection by submitting malicious payloads in GitHub Discussion inputs that are unsafely interpolated: “…an attacker can submit malicious payload as $(curl …)…and execute arbitrary code in the GitHub runner instance.”
- [T1552] Unsecured Credentials – Exfiltration of the GITHUB_TOKEN secret from the GitHub Actions environment to gain unauthorized access: “…exfiltrate the GITHUB_TOKEN and other sensitive repository secrets available in the environment upon execution.”
- [T1609] Container Administration Command Execution – Execution of arbitrary commands on the GitHub Actions runner environment leading to repository content modification and package compromise: “…execute arbitrary commands on the GitHub Actions (GHA) runner…unauthorized changes to repository contents.”
Indicators of Compromise
- [CVE Identifier] Vulnerability tracked as CVE-2025-53104 – critical flaw in gluestack-ui GitHub workflow causing code injection.
- [GitHub Actions Workflow] Vulnerable workflow file – discussion-to-slack.yml, which improperly handles discussion input variables.
- [Artifact] Exploited GITHUB_TOKEN – used to perform unauthorized actions on the repository, including code and release modifications.