Malicious browser extensions disguised as popular games and useful tools are increasingly targeting users across major browsers, employing tactics like redirects to scam sites, affiliate hijacking, and OAuth credential theft. The threat actor mre1903 leads a coordinated campaign of fake gaming extensions, while others like GimmeGimme and CalSyncMaster perform affiliate fraud and steal Google authentication tokens, respectively. #mre1903 #CalSyncMaster #GimmeGimme
Keypoints
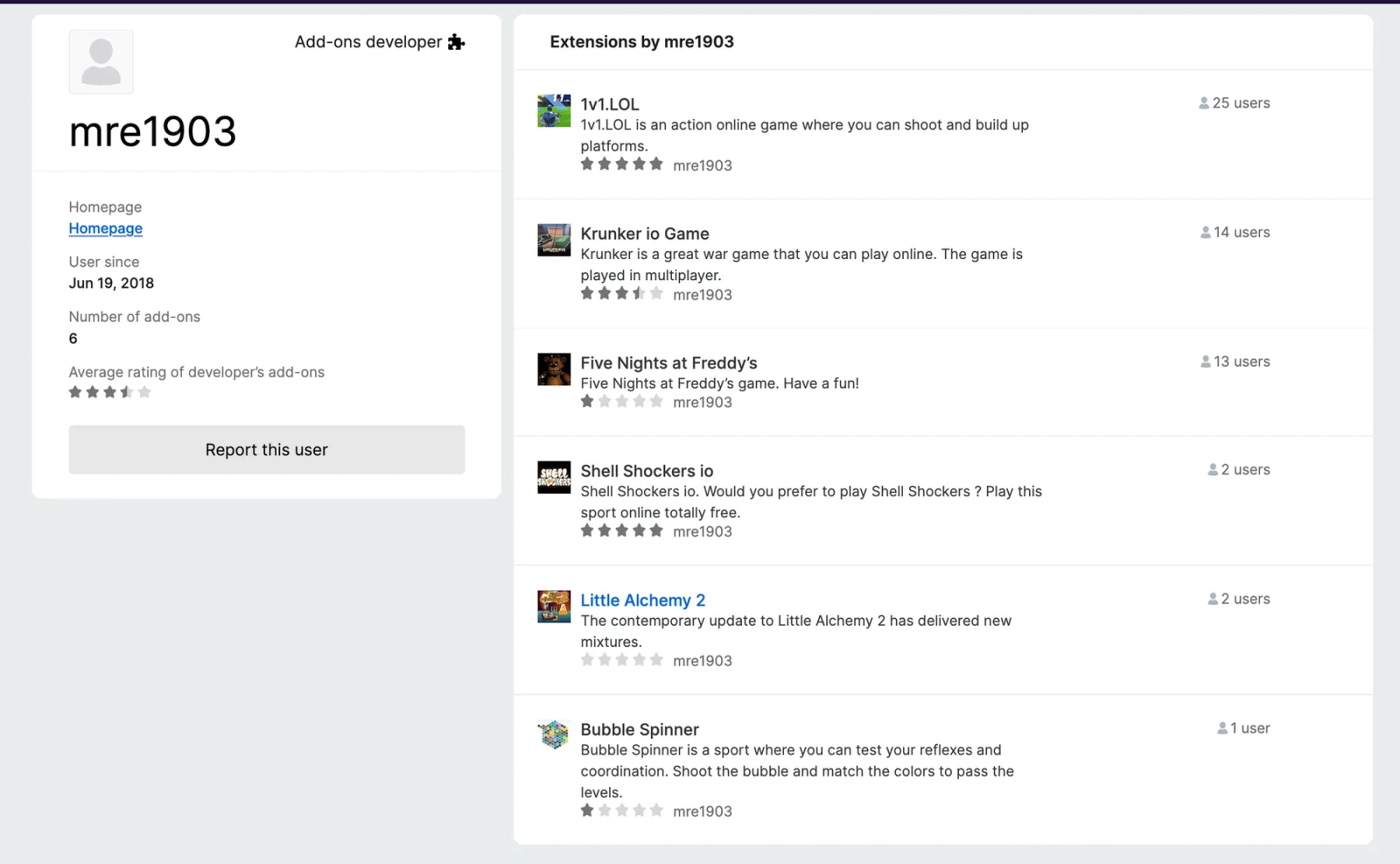
- A network of fake gaming extensions operated by threat actor mre1903 impersonate popular games and redirect users to gambling and scam websites.
- The extensions exploit user trust by using familiar game names like Little Alchemy 2 and Five Nights at Freddy’s, delivering immediate popup scams upon installation.
- The GimmeGimme extension secretly hijacks affiliate sessions on major European shopping sites, generating revenue for attackers while denying promised functionality.
- VPN Grab A Proxy Free injects invisible tracking iframes and routes user traffic through attacker-controlled proxies, exposing all web activity to interception.
- The CalSyncMaster extension steals OAuth tokens via Google Calendar synchronization, providing persistent read-only access to sensitive user data.
- Malicious extensions misuse broad permissions and social engineering to evade detection and escalate attacks within browser environments.
- Recommendations include regular audits of browser extensions, permission reviews, monitoring proxy configurations, and implementing extension allow-lists.
MITRE Techniques
- [T1176.001] Software Extensions: Browser Extensions – Used by malicious extensions to perform unauthorized actions within browser security contexts: “Malicious gaming extensions… redirect users to gambling websites and fake Apple virus alert scam pages.”
- [T1539] Steal Web Session Cookie – Employed by GimmeGimme to hijack user sessions on shopping sites for affiliate revenue: “…it secretly redirects shopping sessions through affiliate tracking links.”
- [T1090] Proxy: External Proxy – VPN Grab A Proxy Free routes traffic through attacker-defined proxies allowing interception: “Routing all traffic through attacker-controlled proxies…”
- [T1566] Phishing – Extensions deliver fake virus alerts designed to extract personal information and money: “Redirected users are exposed to scam operations including fake Apple virus alerts with error codes…”
- [T1036.005] Masquerading – Extensions impersonate popular games to gain user trust and avoid suspicion: “Each extension masquerades as popular, well-known games to exploit user familiarity and trust.”
Indicators of Compromise
- [Malicious Domains] Used for redirect and data collection – funformathgame[.]com, polar-shore-05125-b49ae913d73c[.]herokuapp[.]com
- [Malicious Extensions] Identified threats – CalSyncMaster, VPN Grab A Proxy Free, GimmeGimme, Five Nights at Freddy’s, Little Alchemy 2, Bubble Spinner, 1v1.LOL, Krunker io Game
- [Threat Actor] mre1903 – Operator of multiple fake gaming extensions active since 2018
Read more: https://socket.dev/blog/8-more-malicious-firefox-extensions