In March 2025, critical remote code execution vulnerabilities were disclosed in Apache Tomcat (CVE-2025-24813) and Apache Camel (CVE-2025-27636 and CVE-2025-29891), exposing millions of developers to potential exploits. Following disclosure, widespread scanning and exploitation attempts were observed globally, emphasizing the urgent need for patching. #CVE2025-24813 #ApacheTomcat #CVE2025-27636 #CVE2025-29891 #ApacheCamel
Keypoints
- Apache Tomcat versions 9.0.0.M1 to 9.0.98, 10.1.0-M1 to 10.1.34, and 11.0.0-M1 to 11.0.2 are affected by CVE-2025-24813, which allows remote code execution via exploit of partial PUT requests and session persistence features.
- Apache Camel versions 4.10.0 to 4.10.1, 4.8.0 to 4.8.4, and 3.10.0 to 3.22.3 are vulnerable to CVE-2025-27636 and CVE-2025-29891, allowing remote code execution through manipulated HTTP headers bypassing case-sensitive filters.
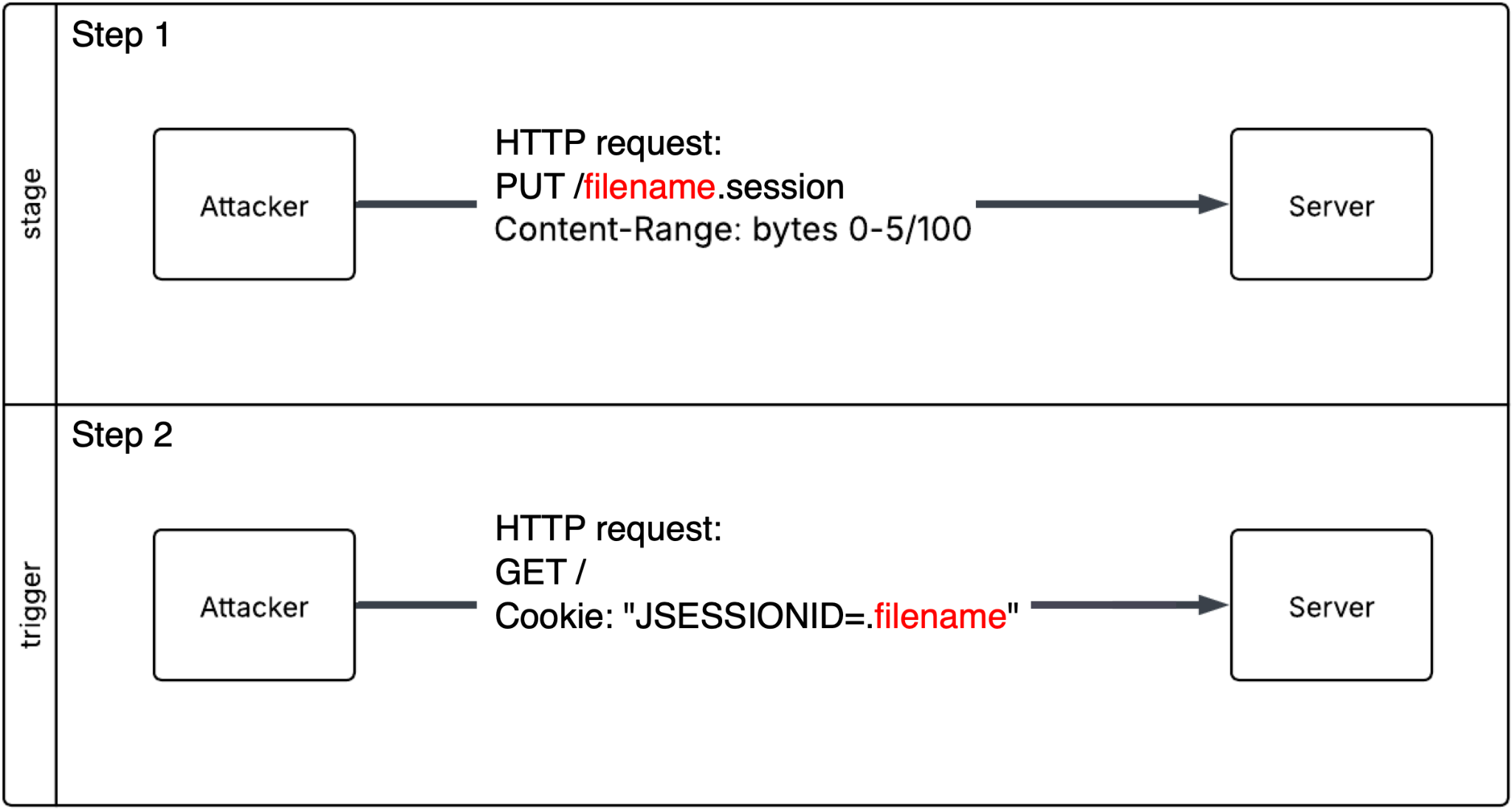
- Exploit of CVE-2025-24813 involves staging serialized malicious code with HTTP PUT requests followed by session-triggering GET requests using manipulated JSESSIONID cookies.
- Telemetry from March 2025 records over 125,000 scans and exploit attempts globally, with more than 7,800 specific attempts against CVE-2025-24813 using tools like the Nuclei Scanner.
- Apache Tomcat vulnerability exploitation requires specific configuration conditions including disabled readonly parameter and enabled session persistence.
- Apache Camel exploit leverages header filtering weaknesses allowing attackers to inject and execute arbitrary commands via manipulated header cases.
- Palo Alto Networks and Cyber Threat Alliance members have rapidly deployed protections and recommend immediate patching and incident response engagement.
MITRE Techniques
- [T1203] Exploitation for Client Execution – Used by attackers staging serialized malicious code via HTTP PUT requests to Apache Tomcat, enabling arbitrary code execution. (“stage the payload by ending it as a file through an HTTP PUT request… This file contains serialized malicious code for later deserialization.”)
- [T1071.001] Application Layer Protocol: Web Protocols – HTTP PUT and GET requests are used to upload malicious payloads and trigger deserialization in Apache Tomcat and to exploit header filtering in Apache Camel. (“sending a file of serialized malicious code as the body of an HTTP PUT request” and “follow-up HTTP GET request to trigger the exploit”)
- [T1548.003] Abuse Elevation Control Mechanism: Bypass User Account Control – Attackers bypass Apache Camel’s case-sensitive HTTP header filter to inject executable commands. (“the filter operates on a case-sensitive basis, an attacker could potentially bypass it by altering the case of the headers.”)
- [T1059.001] Command and Scripting Interpreter: PowerShell – Exploitation of Apache Camel can lead to remote command execution including reverse shells. (“The attacker can potentially get a reverse shell through the remote command execution.”)
Indicators of Compromise
- [IP Addresses] Source IPs involved in CVE-2025-24813 scanning and exploitation include 54.193.62[.]84, 96.113.95[.]10, 209.189.232[.]134 and others (total 13 listed).
- [IP Addresses] Source IPs involved in CVE-2025-27636 and CVE-2025-29891 include 30.153.178[.]49, 54.147.173[.]17, 54.120.8[.]214 and others (total 18 listed).
- [Activity URLs] Examples of HTTP PUT requests targeting CVE-2025-24813 include PUT /qdigu.session and PUT /UlOLJo.session for testing vulnerable Apache Tomcat servers.
- [File Hashes] SHA256 payload samples linked to CVE-2025-24813 exploitation attempts: 6a9a0a3f0763a359737da801a48c7a0a7a75d6fa810418216628891893773540, 6b7912e550c66688c65f8cf8651b638defc4dbeabae5f0f6a23fb20d98333f6b.
- [HTTP Headers] Malicious HTTP headers used in Apache Camel exploits include CAmelHttpResponseCode, CAmelExecCommandExecutable, CAmelExecCommandArgs, and CAmelBeanMethodName.
Read more: https://unit42.paloaltonetworks.com/apache-cve-2025-24813-cve-2025-27636-cve-2025-29891/