Since 2024, North Korean remote IT workers have been leveraging AI technologies like image manipulation and voice-changing software to enhance fraudulent employment operations worldwide. Microsoft tracks these activities under the codename Jasper Sleet and advises organizations to strengthen vetting and monitoring procedures to defend against this sophisticated insider threat. #JasperSleet #NorthKoreanITWorkers #Faceswap #AstrillVPN
Keypoints
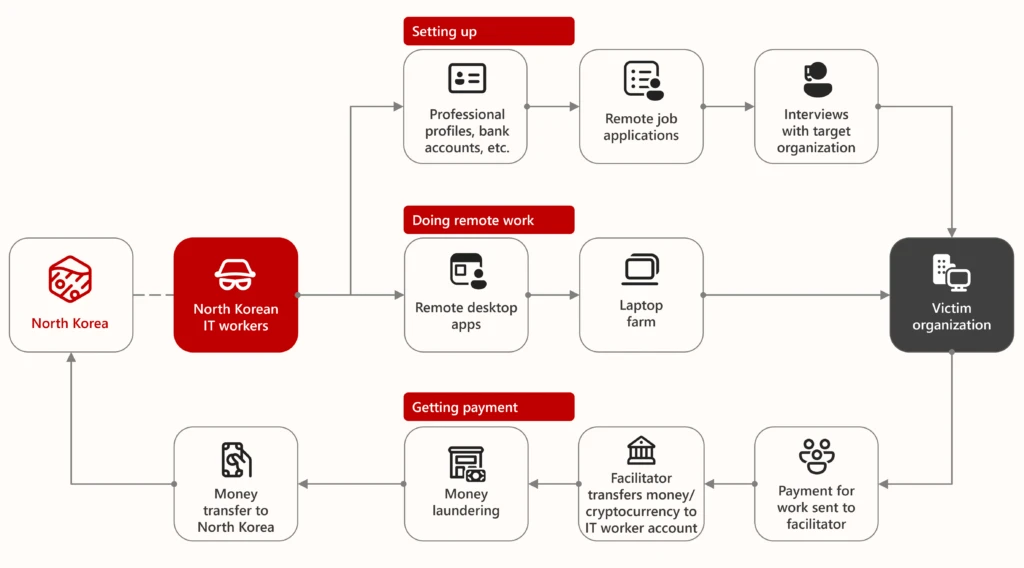
- North Korea deploys thousands of remote IT workers globally to infiltrate technology-related roles and generate revenue for the regime using fraudulent identities and AI tools.
- These workers use AI-enhanced photos, voice-changing software, stolen or rented identities, VPNs like Astrill, and remote access tools such as TeamViewer and Rust Desk to evade detection.
- Facilitators assist workers by validating fraudulent identities, managing logistics, and standing in for interviews or hardware handling.
- Microsoft tracks this activity under the cluster Jasper Sleet (formerly Storm-0287), also monitoring other groups like Storm-1877 and Moonstone Sleet.
- Since 2020, thousands of these North Korean workers have infiltrated multiple industries worldwide, including hundreds of U.S. companies and government agencies.
- Microsoft uses machine learning and threat intelligence to detect and disrupt these operations, suspending thousands of accounts linked to this activity.
- Recommended defenses include strict pre-employment vetting, monitoring for suspicious VPN/RMM use, video verification during hiring, and insider risk management strategies.
MITRE Techniques
- [T1589] Gather Victim Identity Information – North Korean workers create fake personas using stolen or generated identities to apply for jobs (“The workers create, rent, or procure stolen identities that match the geo-location of their target organizations”).
- [T1586] Compromise Accounts – Use of stolen or rented email and social media accounts to establish fraudulent digital footprints (“They create email accounts and social media profiles, and establish legitimacy through fake portfolios”).
- [T1071] Application Layer Protocol – Use of VPNs (e.g., Astrill VPN), VPSs, and proxy services to connect remotely and evade detection (“These workers use VPNs, virtual private servers (VPSs), and proxy services as well as RMM tools to connect to a device housed at a facilitator’s laptop farm”).
- [T1021] Remote Services – Use of remote monitoring and management tools such as TeamViewer, Rust Desk, AnyDesk, and JumpConnect to maintain persistence and conduct remote work (“Workers typically use VPNs… RMM tools including TeamViewer, Rust Desk, AnyViewer, Anydesk”).
- [T1606] Forge Web Credentials – Use of AI tools like Faceswap to forge or enhance images on employment documents and profiles (“North Korean IT workers appear to conduct identity theft and then use AI tools like Faceswap to move their pictures over to the stolen employment and identity documents”).
- [T1036] Masquerading – Use of fake resumes and profiles tailored to specific job requirements to avoid suspicion (“They tailor their fake resumes and profiles to match the requirements for specific remote IT positions”).
Indicators of Compromise
- [Email Accounts] Known fraudulent accounts – Microsoft suspended 3,000 consumer accounts (Outlook/Hotmail) created by North Korean IT workers.
- [IP Addresses] VPN and VPS IPs – Usage of Astrill VPN IPs and VPSs located in China or Russia linked to suspicious remote logins.
- [Software Names] Remote Access Tools – TeamViewer, Rust Desk, AnyViewer, Anydesk, JumpConnect, TinyPilot, PiKVM associated with remote access or control of compromised machines.
- [Social Media Profiles] Fake LinkedIn and GitHub profiles – Profiles used by North Korean workers to establish legitimacy and communicate with recruiters (“Example of a North Korean IT worker LinkedIn profile that has since been taken down”).
- [Documents] Fraudulent identity documents – Fake or stolen driver’s licenses, social security cards, passports, and residency IDs used for employment verification.