TA829 is a cybercriminal actor that also conducts espionage campaigns aligning with Russian state interests, utilizing custom malware like SingleCamper and DustyHammock. A separate cybercriminal cluster, UNK_GreenSec, operates a similar infrastructure and tactics deploying the TransferLoader malware, which has been observed delivering Morpheus ransomware. #TA829 #UNK_GreenSec #TransferLoader #SingleCamper #DustyHammock #MorpheusRansomware
Keypoints
- TA829 conducts both financially-motivated cybercrime and espionage campaigns, using a custom toolset based on the RomCom backdoor.
- Proofpoint identified a separate cybercriminal cluster named UNK_GreenSec deploying the TransferLoader loader and backdoor, with overlapping infrastructure and tactics similar to TA829.
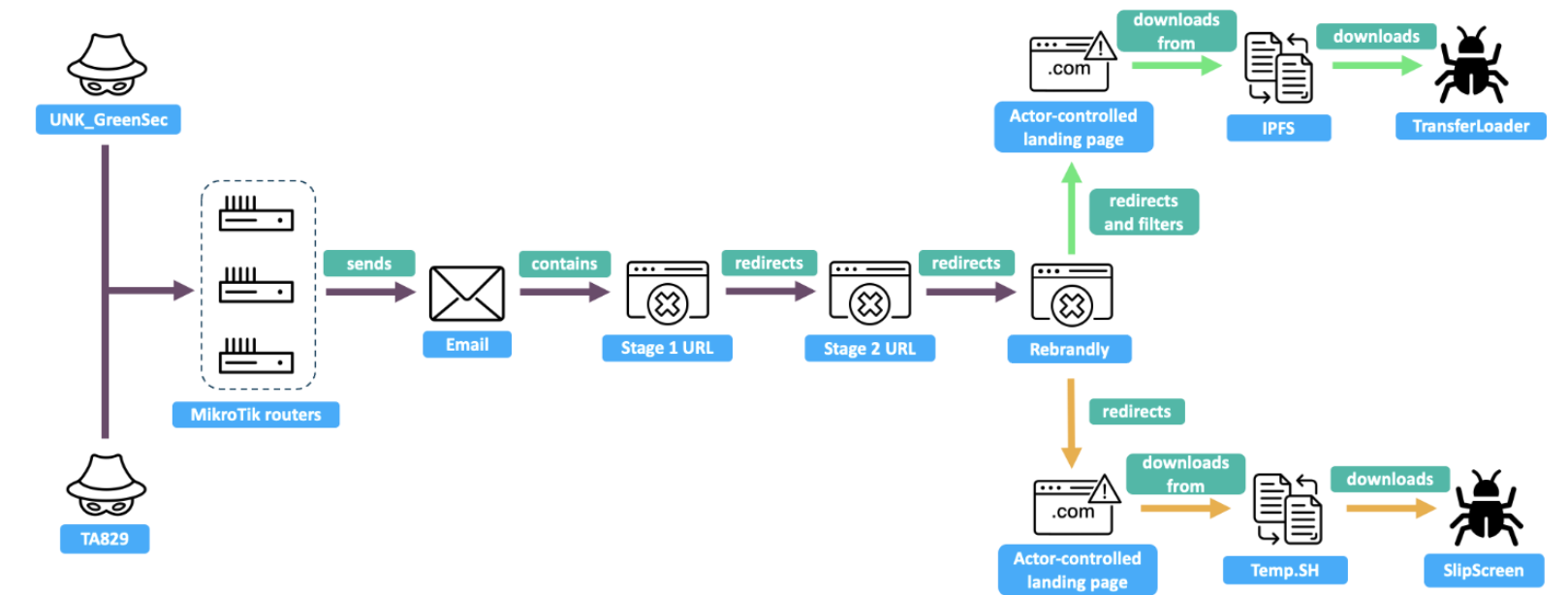
- Both groups abuse compromised MikroTik routers hosting REM Proxy services to send phishing emails with job application lures leading to malicious payloads.
- TA829’s malware families include SingleCamper (espionage and criminal use) and DustyHammock (minimalist backdoor), sharing similar communication structures and infrastructure.
- UNK_GreenSec’s TransferLoader uses sophisticated filename checks, encryption, API hash resolution, and delivers additional malware such as Metasploit and Morpheus ransomware.
- Both clusters employ redirectors like Rebrandly, elaborate landing pages spoofing OneDrive or Google Drive, and use hosting on IPFS webshares for payload delivery.
- The investigation leaves open hypotheses about the relationship between TA829 and UNK_GreenSec, including shared infrastructure providers or them being the same actor testing new malware.
MITRE Techniques
- [T1566] Phishing – Both TA829 and UNK_GreenSec conduct phishing campaigns using email lures themed around job seeking and complaints, containing links or PDFs to malicious domains (’email bodies contain a link to an actor-controlled domain … themed around job seeking or complaints’).
- [T1071] Application Layer Protocol – Actors use HTTP(S) and TCP-based communications for C2 interactions and data exfiltration (‘C2 domains are fronted by CloudFlare … TransferLoader traffic uses custom HTTP headers as well as a TCP-based protocol’).
- [T1204] User Execution – Malware payloads use social engineering, dropping signed executables with spoofed PDF icons upon victim download (‘malware payload spoofs PDF reader’, ‘signed loader that spoofs a PDF’).
- [T1562] Impair Defenses – Use of filtering and anti-analysis techniques such as Cloudflare checks and sandbox evasion via filename validation (‘uses Cloudflare & server-side filtering’, ‘malware will only run if the strings expected remain in the filename’).
- [T1213] Data from Information Repositories – Malware uses Windows Registry to store payloads and achieve persistence (‘registry used for storing additional payloads, persistence, and validating the loader is not running in a sandbox’).
- [T1176] Browser Extensions – Use of redirectors and spoofed sites resembling OneDrive or Google Drive for infection chain (‘landing page that spoofs OneDrive or Google Drive’).
- [T1036] Masquerading – Use of signed binaries with legitimate-looking icons and filenames to evade detection (‘SlipScreen is invalidly signed and uses a PDF reader icon to convince the target to execute it’).
- [T1059] Command and Scripting Interpreter – Malware executes shell commands and network reconnaissance commands automatically (‘DustyHammock execute commands from a C2 that followed the beacon structure and automated reconnaissance commands’).
Indicators of Compromise
- [Domain] TA829 first stage and landing domains – examples include 1drv[.]site, 1drv[.]zone, onedr[.]expert, pdf-share[.]pub, and many others used from October 2024 to April 2025.
- [Domain] UNK_GreenSec first stage and landing domains – examples include 1drive[.]bio, onedrivecloud[.]live, 1drv[.]world, active primarily February to June 2025.
- [Domain] TA829 command and control domains – examples include journalctl[.]website, drivedefend[.]com, consulvprivacy[.]com, supportcausems[.]com.
- [Domain] UNK_GreenSec and TransferLoader C2 domains – examples include temptransfer[.]live and cdngateway[.]us.
- [Certificate] SlipScreen code signing certificates – associated with entities like GMC CONSTRUCTION AND TRADING COMPANY LIMITED, TC SOYUZPLIT LLC, APPRAISAL PHARMACEUTICALS (OPC) PRIVATE LIMITED.
- [File Hashes] Malware samples SHA256 – examples include MeltingClaw (1c6a5476d485…), ShadyHammock (3a234b49b834…), DustyHammock (6d5226cba687…), SingleCamper (54a94c7ec259…).
- [File Hashes] TransferLoader SHA256 – examples include 00385cae3630…, 33971df8f5c3…