North Korean threat actor Lazarus Group and its financially motivated subgroup APT38 (Bluenoroff) have conducted extensive cyberattacks targeting financial institutions worldwide, including the notable 2016 Bangladesh Bank heist. The malware family Cosmic Rust, associated with APT38, targets macOS and communicates with known command and control servers, aiding threat hunting efforts using identified IPs and domains. #LazarusGroup #APT38 #CosmicRust
Keypoints
- Lazarus Group is a North Korean state-sponsored threat actor linked to the Reconnaissance General Bureau (RGB) and active since at least 2009, conducting espionage, data theft, and destructive cyberattacks globally.
- APT38 (Bluenoroff) is a financially motivated subgroup of Lazarus, specializing in targeting banks, financial institutions, casinos, cryptocurrency exchanges, SWIFT endpoints, and ATMs since around 2014.
- Notable APT38 operations include the 2016 Bangladesh Bank heist, which exfiltrated $81 million, and cyberattacks on Bancomext and Banco de Chile in 2018 involving theft and destructive payloads.
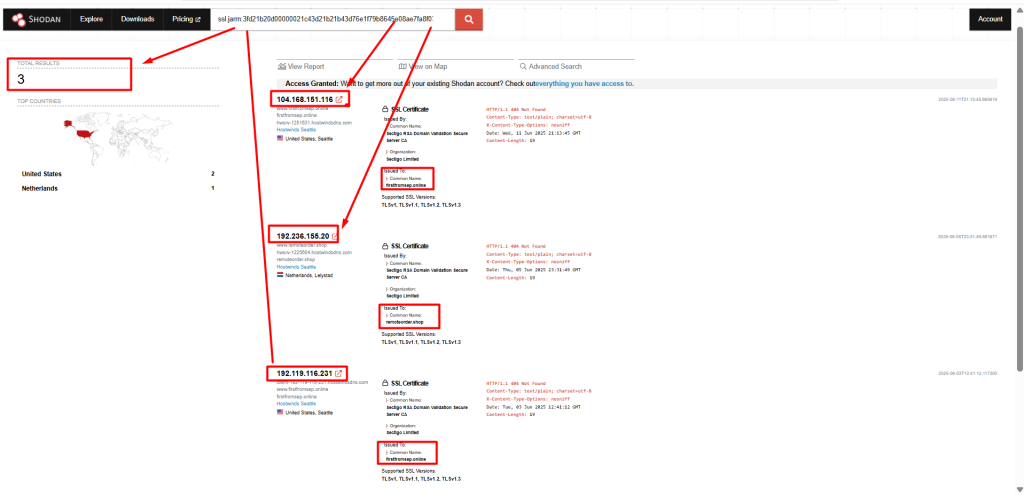
- The IP address 104[.]168[.]151[.]116 has been identified as a pivot point for APT38 infrastructure, linked to phishing domains and additional suspicious IPs such as 140[.]82[.]20[.]246 and 198[.]54[.]117[.]242.
- Cosmic Rust malware, attributed to APT38, targets macOS platforms and communicates with a known command and control server at 104[.]168[.]136[.]24.
- Security researchers are using HTTP header patterns and JARM fingerprints to identify and hunt for APT38 infrastructure across the internet.
- The overlap in tools and infrastructure among North Korean subgroups complicates attribution, leading some analysts to group all activities under the Lazarus Group name.
MITRE Techniques
- [T1071] Application Layer Protocol – APT38 uses HTTP/1.1 protocols with specific headers to pivot and communicate with infrastructure (“HTTP/1.1 404 Not Found Content-Type: text/plain; charset=utf-8 X-Content-Type-Options: nosniff”).
- [T1486] Data Encrypted for Impact – APT38 has deployed destructive payloads during attacks on Bancomext and Banco de Chile to disrupt incident response (“some of which involved destructive payloads aimed at covering traces and disrupting incident response efforts”).
- [T1587] Develop Capabilities – APT38 utilizes the Cosmic Rust malware family targeting macOS systems as part of their toolkit (“Cosmic Rust malware family, which is attributed to APT38… specifically targets macOS platforms”).
- [T1566] Phishing – Phishing domains structurally similar to those resolved by the initial IP address 104[.]168[.]151[.]116 are used in APT38 operations (“The newly identified phishing domains are structurally and thematically similar to those previously resolved by the initial IP address 104[.]168[.]151[.]116”).
Indicators of Compromise
- [IP Address] APT38 infrastructure and command and control servers – 104[.]168[.]151[.]116, 104[.]168[.]136[.]24, 140[.]82[.]20[.]246, 156[.]154[.]132[.]200
- [Domain] Phishing and campaign domains attributed to APT38 – firstfromsep.online, socialsuport.com, gost.run
- [File Hash] Cosmic Rust malware sample (macOS) SHA-256 – dbe48dc08216850e93082b4d27868a7ca51656d9e55366f2642fc5106e3af980
- [Email] Internal identifiers linked to infrastructure – huang-5@1581526809, huang-6@1581526872
Read more: https://darkatlas.io/blog/bluenoroff-apt38-live-infrastructure-hunting