Attackers target WordPress websites by brute forcing admin access to post hidden spam pages, often focused on blackhat SEO such as online casino promotions. They use malicious plugins to maintain access and conceal spam posts, making detection and removal difficult. #WordPressSpam #YoastSEOLinks #PerformanceLabs
Keypoints
- WordPress sites are commonly infected by spam posts created after brute forcing wp-admin access, exploiting weak default protections.
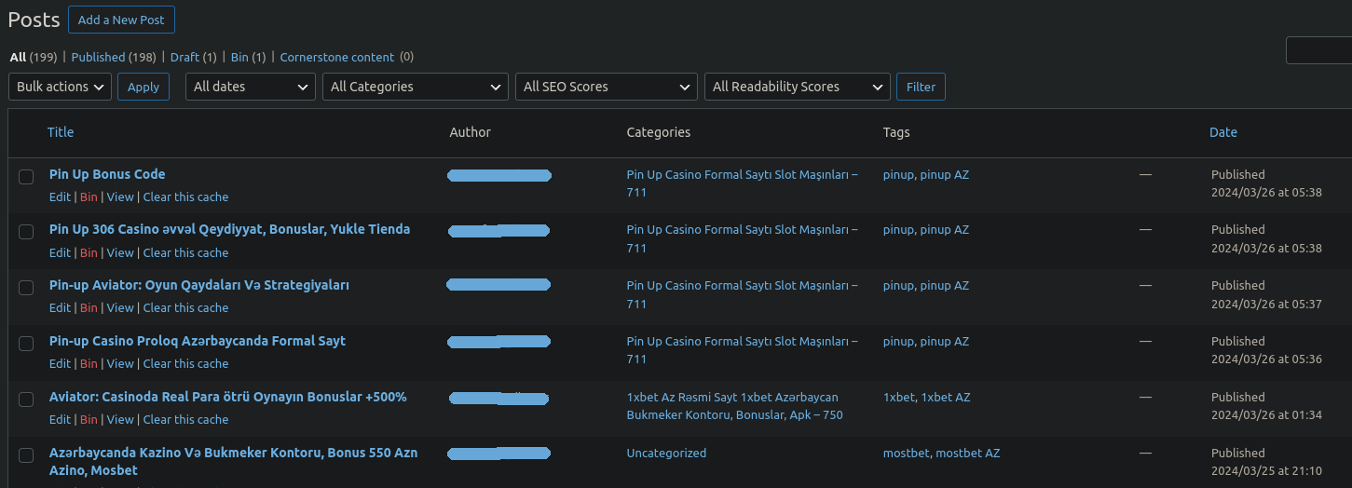
- Attackers post large volumes of spam pages, sometimes in the hundreds of thousands, impacting SEO negatively.
- The spam pages were hidden using malicious plugins that concealed posts from wp-admin search results and admin visibility.
- The backdoor plugin named “yoast-seo-links.php” provides attackers with passwordless admin login and prevents plugin deactivation or deletion.
- The “performance-labs.php” plugin hides specified page/post IDs via admin-only settings and CSS tricks, preventing discovery of spam content.
- Malicious actors exploit plugin tampering to maintain persistent access and disguise blackhat SEO spam on compromised WordPress sites.
- Strong restrictions on wp-admin access, such as IP whitelisting, are essential to prevent such low-sophistication brute force attacks.
MITRE Techniques
- [T1110] Brute Force – Attackers brute forced wp-admin login to gain unauthorized access (“…the attack is very low-level in terms of sophistication: All that is required of the attacker is to brute force their way into the wp-admin panel…”).
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Malicious plugins maintain persistence (“…two culprits… working in tandem to both bury the spam from view and, naturally, to ensure continued admin access to the attackers…”).
- [T1190] Exploit Public-Facing Application – Attackers exploit default WordPress vulnerabilities, such as unlimited login attempts and user enumeration (“…an out-of-the-box WordPress website contains no protection on admin access other than a password…and the admin users can often be discovered via enumeration…”).
- [T1564.001] Hide Artifacts: Hidden Files and Directories – The spam posts were hidden in wp-admin using CSS tricks and concealed plugin options (“…everything was done by adding some additional functionality to wp-admin and just using some simple .CSS tricks…”).
- [T1071.001] Application Layer Protocol: Web Protocols – The attackers use POST requests containing admin_login to log in without a password (“…If the attacker sends a POST request containing admin_login to the infected website the attacker is logged in as the first administrator found…”).
Indicators of Compromise
- [File Names] Malicious WordPress plugin files – ./wp-content/plugins/yoast-seo-links/yoast seo links.php, ./wp-content/plugins/performance-labs/performance labs.php
- [Database Table] Hidden spam post IDs – entries in wp_posts table containing online casino and Farming Simulator spam content
Read more: https://blog.sucuri.net/2025/06/the-case-of-hidden-spam-pages.html