This article explores methodologies for detecting fileless malware that leverages the Windows Registry for staging payloads and persistence, focusing on analytics using Microsoft Defender for Endpoint (MDE). It emphasizes identifying registry-based anomalies through behavioral and statistical techniques, especially involving LOLBins and indirect execution chains. #FilelessMalware #RegistryThreats
Keypoints
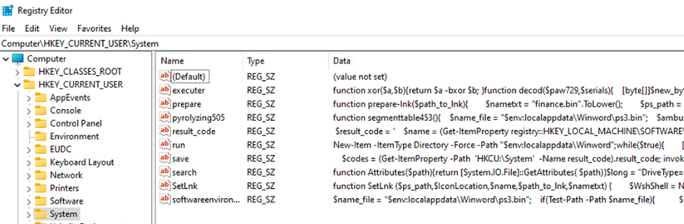
- Fileless malware can store payloads and maintain persistence using Windows Registry keys.
- LOLBins play a critical role in direct and indirect registry modifications in fileless attacks.
- Detection techniques include outlier analysis of registry write lengths and pattern recognition of hex or blob data.
- Threat hunting involves analyzing registry activity from indirect processes like WMI, service processes, and scheduled tasks.
- Multiple analytical approaches, such as behavior correlation and structural pattern matching, enhance detection accuracy.