In 2024, ESET researchers identified BladedFeline, an Iran-aligned APT group active since 2017, targeting Kurdish and Iraqi government officials with advanced malware including the Whisper backdoor and PrimeCache IIS module. The group is assessed as a subgroup of OilRig, utilizing sophisticated tools and maintaining long-term access for cyberespionage purposes. #BladedFeline #Whisper #PrimeCache #OilRig
Keypoints
- BladedFeline has targeted the Kurdistan Regional Government (KRG) since at least 2017, deploying malware linked to OilRig.
- In 2023, the group was discovered after using the Shahmaran backdoor against Kurdish diplomatic officials.
- BladedFeline maintains access to Iraqi government officials and has exploited a telecommunications provider in Uzbekistan.
- The group uses advanced tools such as two reverse tunnels (Laret and Pinar), the Whisper backdoor, and the PrimeCache malicious IIS module.
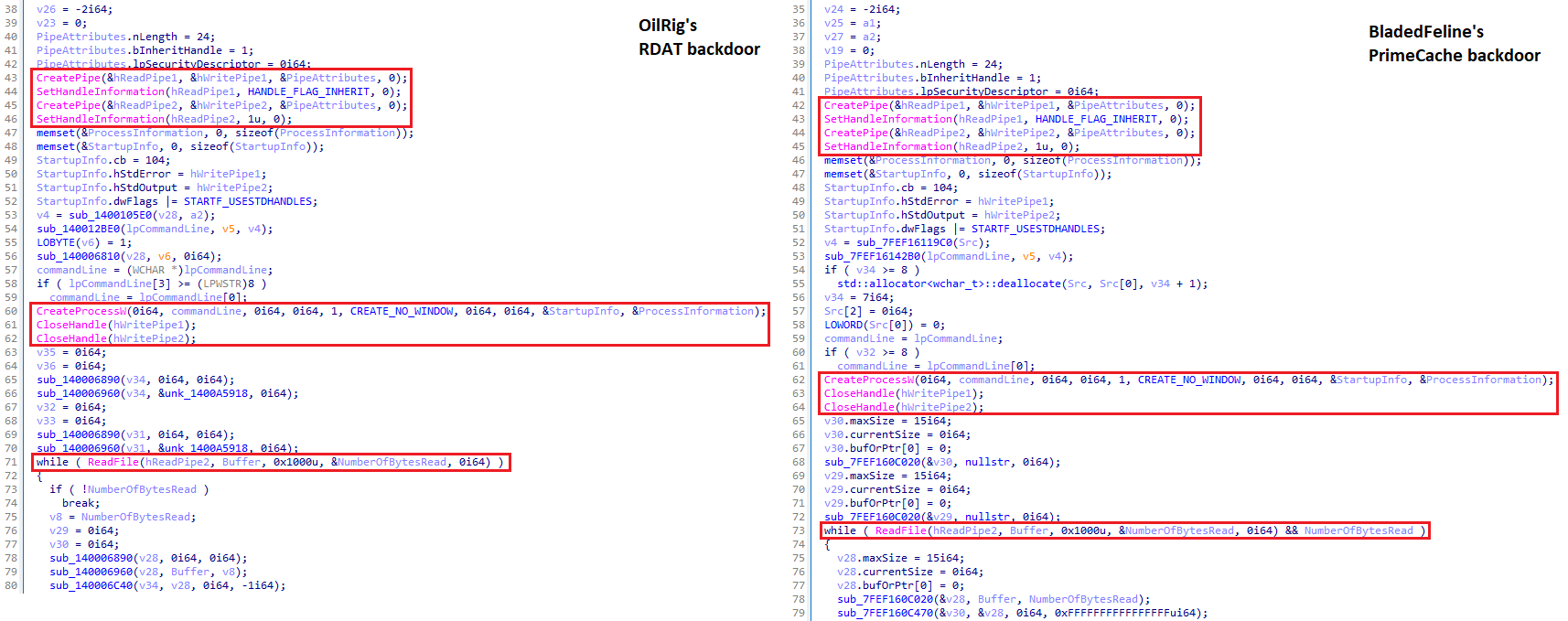
- PrimeCache shares code similarities with OilRig’s RDAT backdoor, supporting the assessment that BladedFeline is a subgroup of OilRig.
- Whisper communicates via compromised Microsoft Exchange webmail accounts by sending and receiving encrypted email attachments.
- BladedFeline conducts operations likely focused on cyberespionage to maintain strategic influence in the Middle East.
MITRE Techniques
- [T1595.002] Active Scanning: Vulnerability Scanning – BladedFeline likely performs vulnerability scanning against targets to identify exploitable public-facing applications.
- [T1583.001] Acquire Infrastructure: Domains – The group registers domains for use as command and control servers.
- [T1583.003] Acquire Infrastructure: Virtual Private Server – VPS services are employed to host C2 infrastructure.
- [T1583] Acquire Infrastructure – Use of IP addresses supports network infrastructure for distribution and command and control.
- [T1586.002] Compromise Accounts: Email Accounts – Use of compromised email accounts as part of command and control communication.
- [T1190] Exploit Public-Facing Application – Probable exploitation of vulnerabilities in public-facing applications to gain initial access.
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – Execution of commands on endpoints via Windows shell.
- [T1059.007] Command and Scripting Interpreter: JavaScript – Use of JavaScript webshells to remotely execute commands.
- [T1059.001] Command and Scripting Interpreter: PowerShell – Execution of PowerShell commands on compromised systems.
- [T1059.006] Command and Scripting Interpreter: Python – Usage of Python-based droppers for deploying backdoors.
- [T1559] Inter-Process Communication – IPC techniques employed within malicious IIS modules.
- [T1569.002] System Services: Service Execution – Use of Windows services to execute malware such as Whisper and PrimeCache.
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Whisper achieves persistence by creating shortcuts in startup folders.
- [T1546] Event Triggered Execution – PrimeCache loads via IIS Worker Process upon receiving HTTP requests.
- [T1078] Valid Accounts – Use of legitimate credentials to exfiltrate data and maintain stealth.
- [T1140] Deobfuscate/Decode Files or Information – Use of base64 encoding to obfuscate data in Whisper backdoor communications.
- [T1070.004] Indicator Removal: File Deletion – The Whisper Python dropper deletes itself and supporting files after installation.
- [T1070.006] Indicator Removal: Timestomp – Frequent timestomping of malware compilation timestamps to evade detection.
- [T1003.001] OS Credential Dumping: LSASS Memory – Credential dumping via LSASS memory from compromised systems.
- [T1573.001] Encrypted Channel: Symmetric Cryptography – AES encryption used by Whisper for command and control data transfer.
- [T1071.001] Application Layer Protocol: Web Protocols – PrimeCache communicates using standard web protocols.
- [T1132.001] Data Encoding: Standard Encoding – Use of base64 encoding for C2 communications in PrimeCache.
- [T1573.002] Encrypted Channel: Asymmetric Cryptography – Use of RSA and AES-CBC encryption in PrimeCache communications.
- [T1105] Ingress Tool Transfer – PrimeCache can download and execute additional files from C2 servers.
- [T1048.001] Exfiltration Over Alternative Protocol: Symmetric Encrypted Non-C2 Protocol – Whisper uses encrypted email channels for exfiltration.
- [T1041] Exfiltration Over C2 Channel – PrimeCache exfiltrates data via C2 communication channels.
Indicators of Compromise
- [File Hashes] Malware samples – examples include 562E1678EC8FDC1D83A3F73EB511A6DDA08F3B3D (RDAT backdoor), 6973D3FF8852A3292380B07858D43D0B80C0616E (Whisper backdoor), 3D21E1C9DFBA38EC6997AE6E426DF9291F89762A (Flog webshell), and BE0AD25B7B48347984908175404996531CFD74B7 (VideoSRV reverse shell).
- [Domains] Command and control and infrastructure – olinpa[.]com (Shahmaran C2 domain), zaincell[.]store (Slippery Snakelet C2 disguised as Arabian Gulf E-Learning site).
- [IP Addresses] Distribution and C2 servers – 178.209.51[.]61 (Laret reverse tunnel distribution server), 185.76.78[.]177 (C2 used by Spearal backdoor).
- [File Names] Examples include adobeupdater.exe (Shahmaran backdoor), Protocol.pdf.exe (Whisper Protocol dropper), flogon.aspx (Flog webshell), and cachehttp.dll (PrimeCache malicious IIS module).
Read more: https://www.welivesecurity.com/en/eset-research/bladedfeline-whispering-dark/