The “PM KISAN YOJNA” Android malware masquerades as an official government app to steal sensitive user information through multi-stage droppers and advanced evasion techniques. It installs fake updates, requests dangerous permissions, and exfiltrates data via a covert VPN connection and C2 server communication. #PMKISANYOJNA #Salvador #K7MobileSecurity
Keypoints
- The malware disguises itself as the official “PM KISAN YOJNA” government app and uses a multi-stage dropper technique to avoid detection.
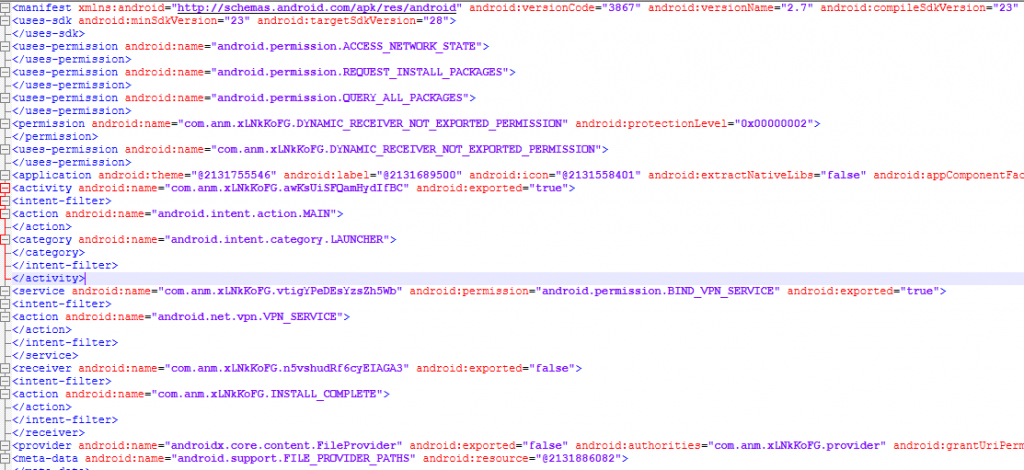
- It requests high-risk permissions including QUERYALLPACKAGES, REQUESTINSTALLPACKAGES, VPN setup, and SMS access to perform malicious activities.
- Emulator, Frida, and root detection are incorporated to evade dynamic analysis and sandbox environments.
- The app prompts users to install a fake update, which is actually a separate malicious app that hides its icon and mimics legitimate app names.
- Collected sensitive data include personal identification information such as Name, Mobile Number, Aadhaar Card, PAN Card, Date of Birth, and SMS messages.
- The malware transmits stolen data to a command-and-control (C2) server, though some servers were unavailable during analysis.
- The new variant named “Salvador” indicates ongoing refinement by attackers to improve stealth and data theft efficiency.
MITRE Techniques
- [T1543] Create or Modify System Process – The malware installs another APK “decryptedapp.apk” to carry out its payload through persistence. (‘installs another APK “decryptedapp.apk” with package name com.service.shop’)
- [T1071] Application Layer Protocol – Data is exfiltrated to a command-and-control server via network connections established by the app. (‘transmits them to the C2 server’)
- [T1204] User Execution – The malware relies on user interaction to install updates and grant permissions. (‘app immediately prompts the user to install an update for the app’)
- [T1056] Input Capture – The malware collects personal information and SMS messages from the device. (‘collects personal information like Name, Mobile Number, Aadhaar Card, PAN Card, and Date of Birth’)
- [T1606] Obfuscated Files or Information – The dropper payloads were deliberately malformed to evade static and APK analysis tools. (‘malware author intentionally crafted these dropper payloads to bypass static analysis’)
- [T1620] Reflective Code Loading – The malware uses a multi-stage dropper technique to install additional malicious components stealthily. (‘uses a multi-stage dropper technique’)
- [T1057] Process Discovery – Emulator, Frida, and root checking techniques are used to detect analysis environments. (‘app incorporates emulator check, Frida check and root check to avoid being analysed’)
Indicators of Compromise
- [File Hash] Dropper APK hash – a6e03e3fbe4eefffea8167c711f516ac
- [File Hash] Payload APK hash – 39ecbe64e324d7ed9001a001a1a02edd
- [Package Name] Malicious APK package names – com.service.shop, com.anm.xLNkKoFG, com.YMQ.jUe3SzqW1
- [Detection Name] Spyware detections for multiple package names including com.reg.wIDTSOQCc and com.aeJ.aKAC3He4c