A threat actor using aliases such as Bùi nam published malicious Ruby gems that impersonate legitimate Fastlane plugins to exfiltrate Telegram bot tokens and message data through a proxy server. These supply chain attacks coincided with Vietnam’s nationwide Telegram ban, targeting developers seeking proxy workarounds. #fastlane-plugin-telegram-proxy #Buidanhnam #RubyGems
Keypoints
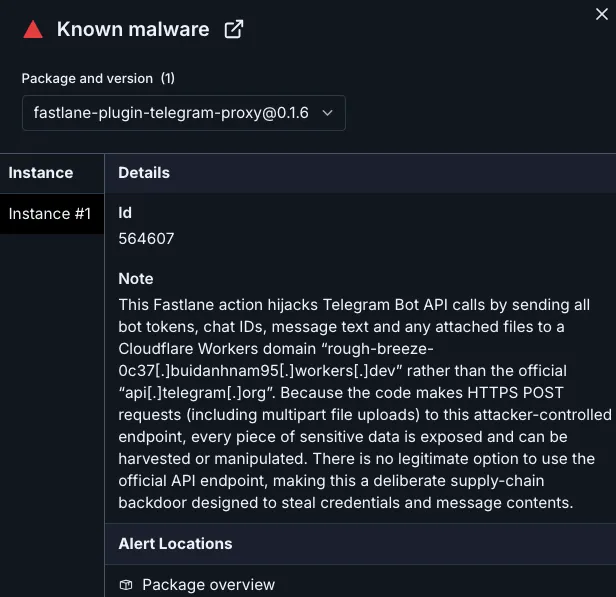
- The threat actor published two malicious Ruby gems, fastlane-plugin-telegram-proxy and fastlane-plugin-proxy_teleram, that impersonate legitimate Fastlane plugins to steal Telegram API data.
- The malicious gems redirect Telegram API calls through a hardcoded, threat actor-controlled proxy server hosted on Cloudflare Workers.
- This proxy silently exfiltrates bot tokens, chat IDs, message contents, and attached files from CI/CD pipelines without detection.
- The campaign was timed to exploit the increased demand for Telegram proxies following Vietnam’s nationwide ban on Telegram on May 21, 2025.
- The malicious gems use typosquatting techniques, including slight name misspellings and forked repositories, to blend into the RubyGems ecosystem and evade suspicion.
- The threat actor’s identity and campaign themes strongly indicate a connection to Vietnam, though the malware itself lacks geographic restrictions and can impact global users.
- Security recommendations include immediate removal of the malicious gems, revocation and rotation of compromised Telegram bot tokens, and configuring network egress rules to block the malicious proxy endpoint.
MITRE Techniques
- [T1195.002] Supply Chain Compromise – The attacker compromised the software supply chain by publishing malicious gems that impersonate legitimate Fastlane plugins and modify network endpoints (“the only malicious logic” was replacing the API URI with their proxy).
- [T1036.005] Masquerading – The malicious gems closely mimic legitimate plugin names and repositories, using slight misspellings and forks to evade detection (“typosquatting of a trusted Fastlane plugin”).
- [T1041] Exfiltration over C2 channel – Sensitive Telegram bot tokens, chat IDs, messages, and files are exfiltrated through a hardcoded Cloudflare Workers proxy endpoint (“the relay silently exfiltrates the bot token, chat ID, message text, and any attached files”).
- [T1078] Valid Accounts – The attacker uses stolen valid Telegram bot tokens to maintain persistent access until the tokens are manually revoked (“Stolen tokens remain valid until manually revoked”).
Indicators of Compromise
- [Malicious Ruby Gems] supply chain attack – fastlane-plugin-telegram-proxy, fastlane-plugin-proxy_teleram
- [C2 Endpoint] exfiltration proxy – rough-breeze-0c37.buidanhnam95.workers.dev
- [Threat Actor Aliases] attributed identities – Bùi nam, buidanhnam, si_mobile
- [GitHub Repository] malicious source code hosting – github.com/buidanhnam/fastlane-plugin-telegram