The SideWinder APT group has updated its toolset and expanded attacks targeting maritime, logistics companies, and nuclear power plants in Asia and Africa. Securelist identified multiple domains and IP addresses linked to these attacks, revealing new infrastructure and weaponized IPs. #SideWinder #Djibouti #Egypt #NuclearPowerPlants
Keypoints
- SideWinder, active since 2012, targets government, military, and businesses mainly in Asia, notably in Pakistan, China, Nepal, and Afghanistan.
- The group increased attacks on maritime and logistics companies in Djibouti and Egypt, as well as nuclear power plants in South Asia and Africa.
- Securelist identified 35 domains as indicators of compromise (IoCs) connected to the latest SideWinder operations.
- Expanded analysis uncovered 35 email-connected domains, 10 IP-connected domains, and 532 string-connected domains related to SideWinder.
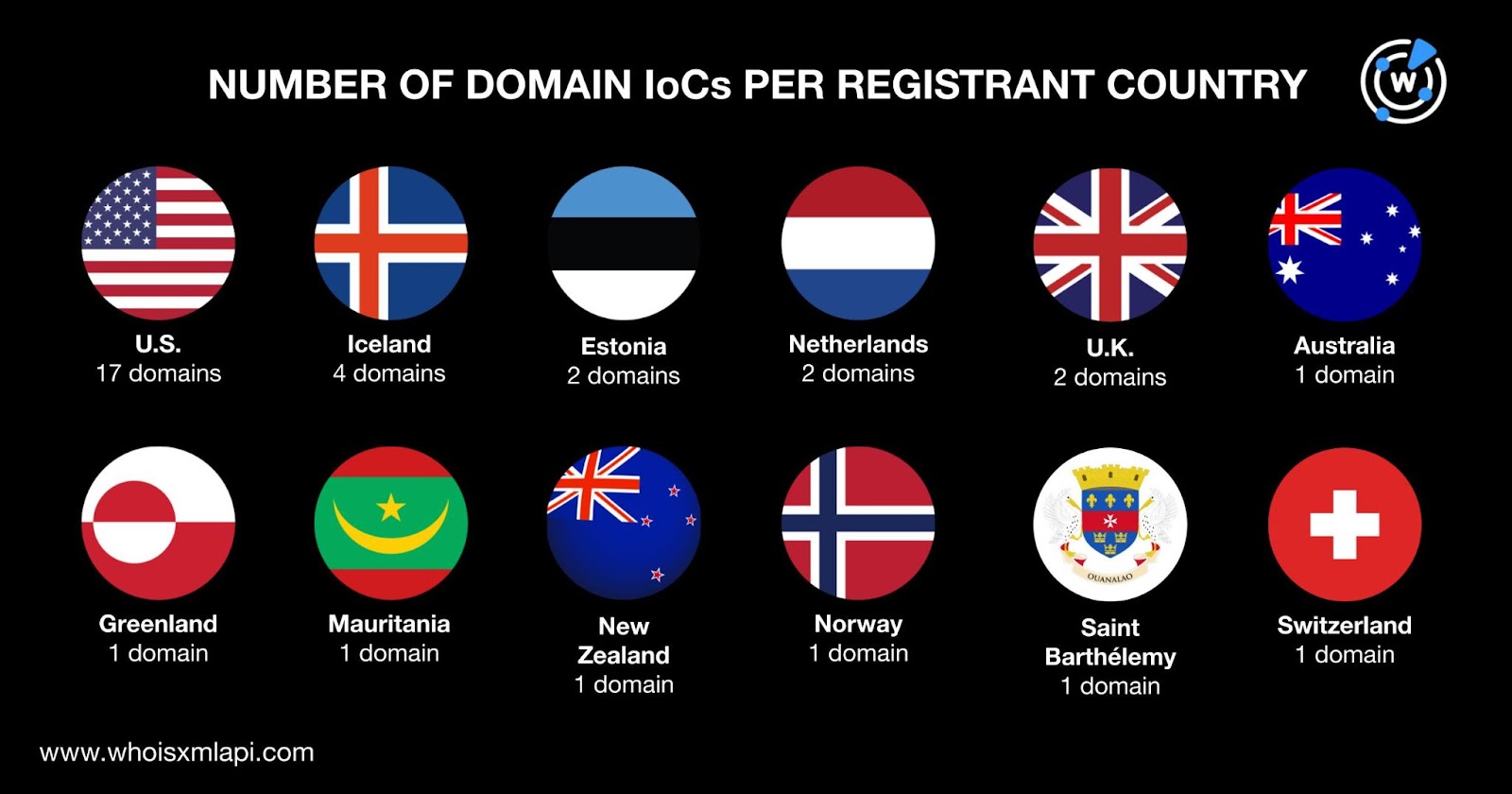
- The 34 domains with current WHOIS records were all created in 2024 and registered mostly in the U.S. across six registrars.
- One IP address, 91[.]195[.]240[.]12, was weaponized and linked to phishing, command and control, malware distribution, and suspicious activity.
- Several domains showed historical domain-to-IP resolutions dating back to 2020, indicating potential domain re-registration for attacks.
MITRE Techniques
- [T1071] Application Layer Protocol – SideWinder used multiple domains and IP addresses to manage malware spread and command and control operations (“…weaponized in connection with phishing, command and control (C&C), attacks…”).
- [T1588] Obtain Capabilities – The group updated toolsets and created new infrastructure for expanded attacks (“…the threat actors updated their toolset and created new infrastructure to spread malware…”).
- [T1070] Indicator Removal on Host – Domains were re-registered such as documentviewer[.]info to evade detection (“…domain documentviewer[.]info was created on 8 August 2024, indicating possible re-registration for the attack…”).
Indicators of Compromise
- [Domains] 35 IoC-linked domains created in 2024, e.g., documentviewer[.]info, aliyum[.]email, depo-govpk[.]com.
- [IP Addresses] Two IPs found; notably 91[.]195[.]240[.]12 linked to malware distribution and command and control.
- [Email Addresses] Six domains linked to 10 email addresses found in WHOIS records, including two public emails used in historical domain registrations.
Read more: https://circleid.com/posts/exploring-the-dns-flipside-of-sidewinder