Threat actors are exploiting the popularity of online learning platforms by launching a phishing campaign that spoofs Coursera and redirects victims to a fake Meta login page. This campaign uses enticing offers of free certificates to lure users into submitting their credentials on fraudulent sites. #Coursera #MetaPhishing #ProLearningAcademy
Keypoints
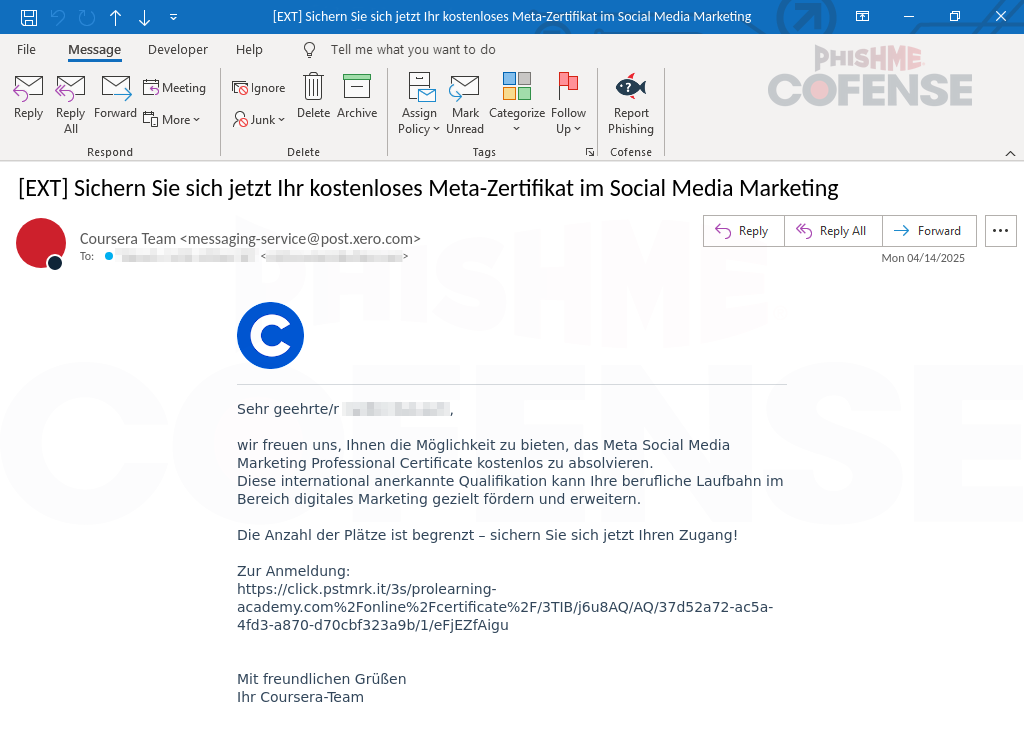
- The phishing campaign begins with an email pretending to be from the “Coursera Team” offering a free Meta Social Media Marketing Professional Certificate.
- The sender’s email address is suspicious and does not match Coursera’s official domain, indicating a phishing attempt.
- The email creates urgency and excitement by emphasizing limited free enrollment on an internationally recognized course.
- Victims are directed to a fake course enrollment page on the domain prolearning-academy[.]com, which mimics Coursera’s legitimate site.
- Upon clicking “Enroll for Free,” users are prompted to log in using Facebook, further leading to a fake Facebook login page to harvest credentials.
- The final phishing page collects victims’ email/phone numbers and passwords, which are sent to the attackers’ command-and-control server.
- The campaign illustrates how attackers exploit trusted platforms and social engineering tactics to steal sensitive information.
MITRE Techniques
- [T1192] Spearphishing Link – The phishing email entices victims with a fake online course offer leading to a malicious URL (“‘We are pleased to offer you the opportunity to complete the Meta Social Media Marketing Professional Certificate free of charge…’”).
- [T1204] User Execution – Victims are tricked into clicking the enrollment and login buttons, initiating credential theft (“‘Enroll for Free’ button clicked to continue and finalize enrollment”).
- [T1566.001] Phishing: Spearphishing Attachment – The use of a spoofed email with deceptive content mimics legitimate Coursera communications to gain trust (“‘Email coming from “Coursera Team” with a subject that translates to “Get your free Meta Certificate in Social Media Marketing now.”’”).
- [T1078] Valid Accounts – Attackers harvest legitimate user Facebook credentials through a fake login page (“‘Users are presented with a fake Facebook login page, expected to type their email and password…’”).
Indicators of Compromise
- [Domain] Malicious landing page – prolearning-academy[.]com used to host fake Coursera enrollment page.
- [IP Address] Infection server – 52.38.173.188 associated with the phishing landing page.
- [Payload URL] Credential exfiltration endpoint – hxxps://six.anotherlevel.app/api/send_login/67fd232e7901ae64481ec04a/
- [IP Address] Payload server – 67.81.214.146 hosting the C2 server receiving stolen credentials.
Read more: https://cofense.com/blog/fake-course-real-threat-learning-a-phishing-lesson-the-hard-way
.png)