The Sosano backdoor is a sophisticated malware strain targeting critical sectors using polyglot files and spear-phishing via compromised email accounts. This article details how to detect and remove Sosano on Windows endpoints using Sysmon integration and customized Wazuh rules with Active Response automation. #Sosano #INDICEMSElectronics #Wazuh
Keypoints
- The Sosano backdoor emerged in late 2024, targeting aviation, satellite communications, and transportation infrastructure sectors.
- It uses rare polyglot files combining multiple formats (PDF, HTA, ZIP, LNK) to evade detection and execute malicious payloads.
- Attackers compromised an Indian company’s email (INDIC EMS Electronics) to send spear-phishing emails with URLs pointing to fake domains hosting Sosano.
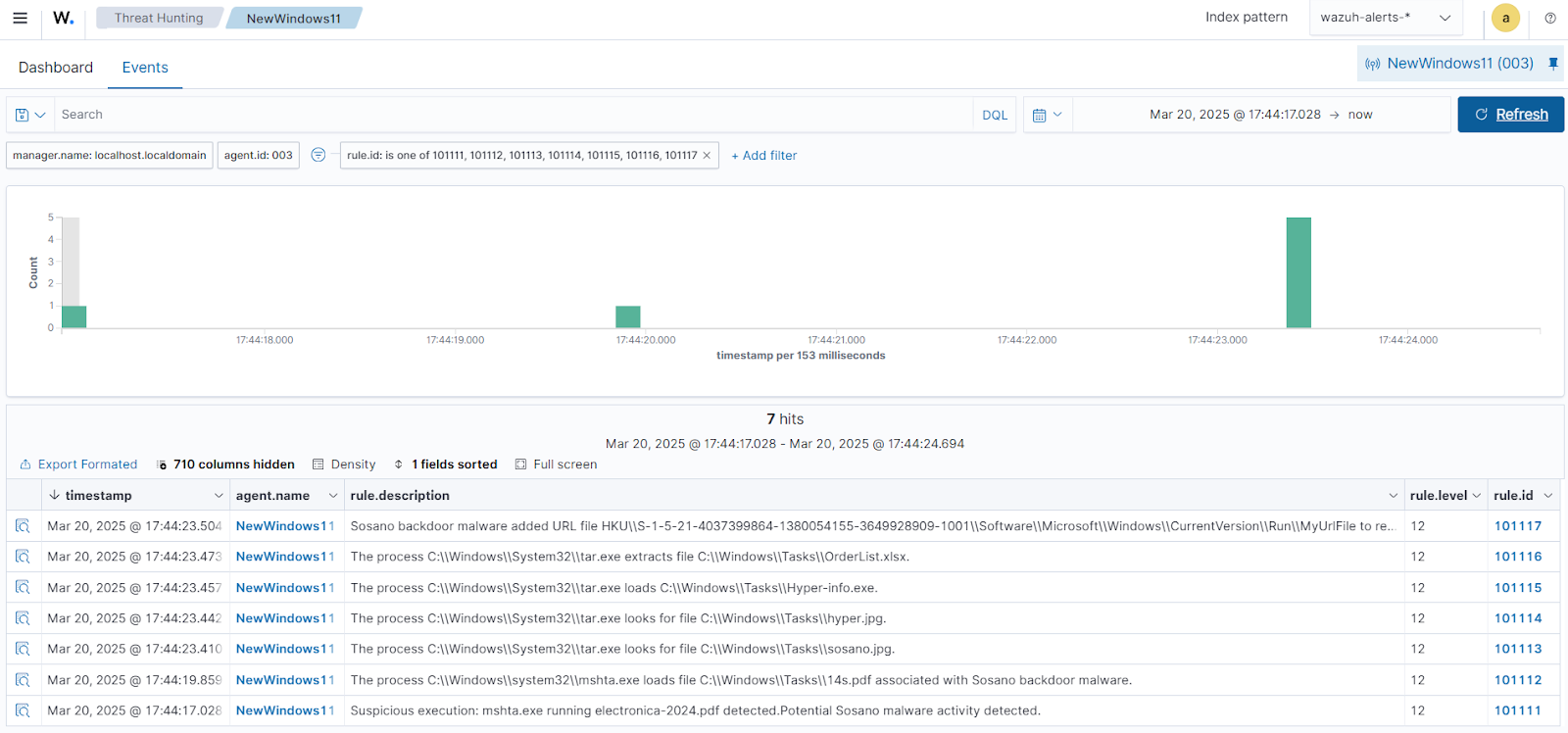
- The malware executes via an LNK file launching mshta.exe to run a PDF/HTA polyglot file and establishes persistence via registry runkey.
- Detection leverages Sysmon logs forwarded to Wazuh server, implementing custom rules to identify Sosano-specific behaviors and files.
- Known Sosano malware file hashes are maintained in Wazuh’s CDB list for file integrity monitoring and detection.
- Wazuh’s Active Response module automates removal of Sosano files on Windows endpoints using a custom Python-based executable script triggered on detection.
MITRE Techniques
- [T1218.005] Mshta Abuse – The malware uses mshta.exe to execute embedded HTA code inside a PDF/HTA polyglot file (“The LNK file launches cmd.exe and uses mshta.exe to execute the first PDF/HTA polyglot file.”)
- [T1204.002] User Execution: Malicious File – Sosano backdoor involves user execution of spear-phishing emails containing malicious URLs leading to infection (“phishing emails containing URLs that directed recipients to a counterfeit domain… designed to deploy the Sosano backdoor”).
Indicators of Compromise
- [File Hashes] Known Sosano malware hashes used for detection – SHA256: 336d9501129129b917b23c60b01b56608a444b0fbe1f2fdea5d5beb4070f1f14, 394d76104dc34c9b453b5adaf06c58de8f648343659c0e0512dd6e88def04de3, and 5 more hashes.
- [File Names] Malicious payload components within OrderList.zip archive – OrderList.xlsx (disguised LNK file), sosano.jpg, hyper.jpg, Hyper-info.exe, 14s.pdf.
- [Domains] Fake domain impersonating INDIC EMS Electronics hosting the malicious ZIP archive (exact domain not provided).
- [Registry Key] Persistence registry runkey – HKUSoftwareMicrosoftWindowsCurrentVersionRunMyUrlFile points to malicious URL file (youtube.url).
Read more: https://wazuh.com/blog/detecting-and-removing-sosano-backdoor-malware-with-wazuh/