InvisibleFerret is a Python-based backdoor malware used by North Korean threat actors like the Lazarus Group, targeting Windows and Linux systems through social engineering disguised as recruitment schemes. This article explains how to detect and mitigate InvisibleFerret on Linux endpoints using Wazuh’s custom detection rules, CDB lists, and Active Response automation. #InvisibleFerret #LazarusGroup #Wazuh #SysmonForLinux
Keypoints
- InvisibleFerret is a backdoor malware delivered as a second-stage payload by the BeaverTail loader, primarily targeting technology, financial, and cryptocurrency sectors.
- The malware collects internal IP, geolocation, system details, creates and deletes obfuscated temporary files, and maintains persistence by downloading AnyDesk for remote access.
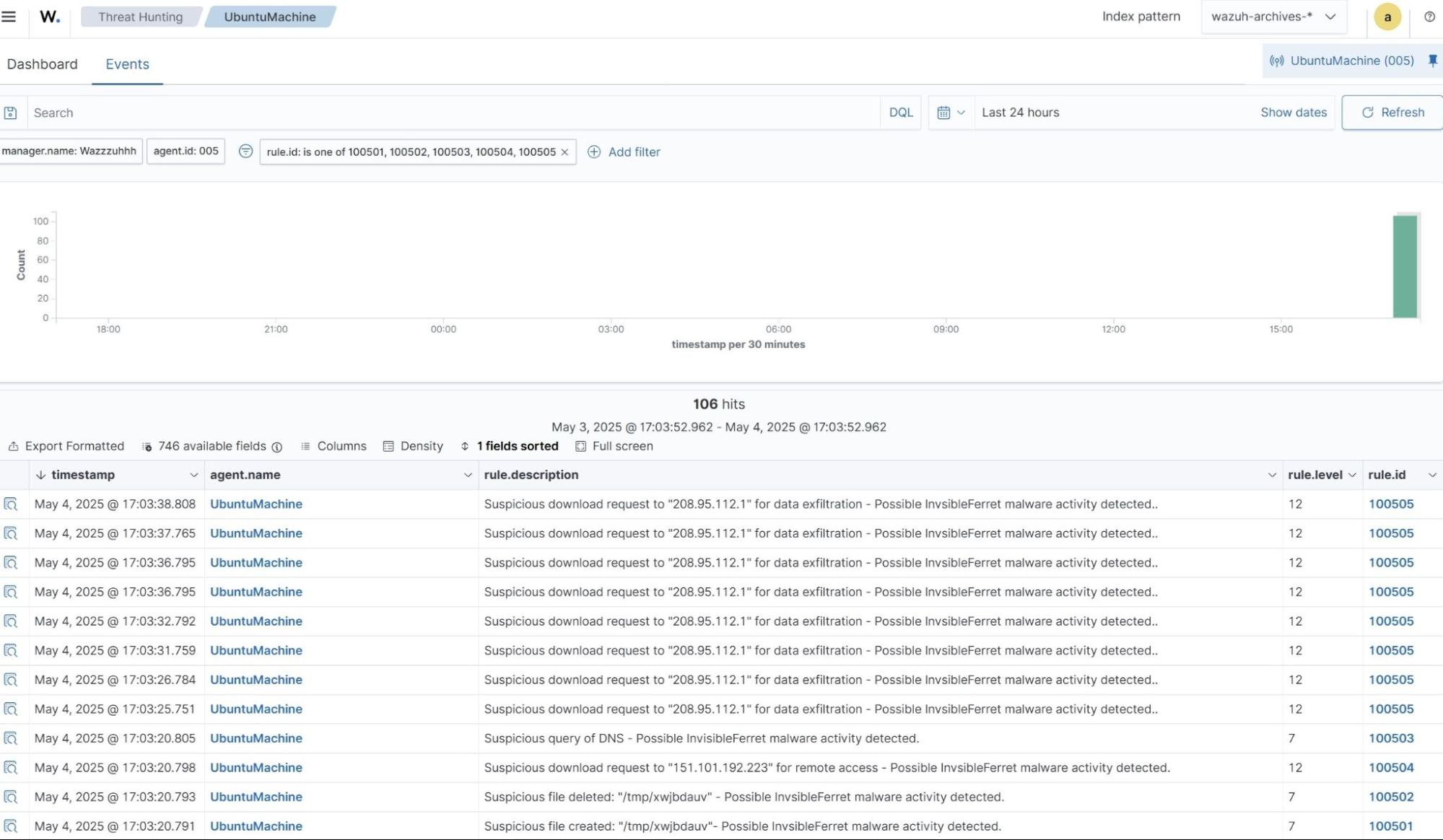
- Detection on Linux endpoints is enhanced by integrating SysmonForLinux to generate rich event logs analyzed by custom Wazuh decoders and rules tailored to InvisibleFerret behaviors.
- Wazuh rules monitor suspicious file creation and deletion in /tmp/, DNS queries, and network requests linked to malware command-and-control and data exfiltration activities.
- A CDB list containing known InvisibleFerret file hashes enables real-time detection via Wazuh File Integrity Monitoring in monitored directories such as user Downloads folders.
- The Wazuh Active Response module automates malware removal by executing a custom Python script to delete detected InvisibleFerret malicious files immediately upon detection.
- Detailed instructions are provided to configure Wazuh components, SysmonForLinux, detection rules, CDB lists, and Active Response for comprehensive InvisibleFerret threat mitigation on Linux.
MITRE Techniques
- [T1044] File System Permissions Weakness – Triggered by rule ID 100501 which detects suspicious file creation in the /tmp directory (“Suspicious file created…Possible InvisibleFerret malware activity detected”).
- [T1107] File Deletion – Triggered by rule ID 100502 monitoring immediate deletion of suspicious files to cover malware tracks (“Suspicious file deleted…Possible InvisibleFerret malware activity detected”).
- [T1485] Data Destruction – Also linked to rule 100502 detecting deletion of files used by malware for operational security.
- [T1043] Commonly Used Port – Detected by multiple rules (100503, 100504, 100505) when malware performs suspicious DNS queries and makes network connections for C2 communication and data exfiltration (“Suspicious query of DNS”, “Suspicious download request for remote access”, “Suspicious download request for data exfiltration”).
- [T1204.002] User Execution: Malicious File – Triggered by rule 100510 when detection occurs based on known malware file hashes in the CDB list (“A known InvisibleFerret malware hash detected”).
Indicators of Compromise
- [File Hashes] Known InvisibleFerret malware hashes used in detection – SHA256 hashes: 2012f6f7d8add86ebbc6629815832554fca37cc3e1edab68a51f57e345365f85, a2de54fbfbca6e1715b2621ab382e9c1c645fdb0723a410e8775d2ac026897c8, and 11dde438e1a636073e79c81d4c2543708cc0a2922e7c42c38b1b588e17545f96.
- [File Names] Temporary files with 8-character random alphanumeric names created and deleted in /tmp/ directory as part of malware activity.
- [IP Addresses] Examples of destination IPs involved in suspicious downloads: 151.101.x.x (AnyDesk C2 server), 208.95.x.x (data exfiltration endpoint).
- [File Paths] Malicious files dropped or executed in user Downloads directories monitored via Wazuh FIM.
Read more: https://wazuh.com/blog/detecting-and-responding-to-invisibleferret-with-wazuh/