The article analyzes recent cyber campaigns by the GRU Unit 26165 targeting Western logistics and technology firms, focusing on their post-compromise tactics using built-in Windows tools and malware like HEADLACE and MASEPIE. It also highlights detection strategies and mitigation recommendations to defend against their espionage and disrupt operations supporting Ukrainian aid. #GRUUnit26165 #HEADLACE #MASEPIE
Keypoints
- GRU Unit 26165 conducts cyber espionage and sabotage against supply chains linked to Ukraine by leveraging built-in Windows tools like PowerShell, PsExec, and RDP post-compromise.
- Initial access vectors include exploitation of vulnerabilities such as CVE-2023-23397 (Outlook NTLM flaw), multiple Roundcube CVEs, and a WinRAR vulnerability (CVE-2023-38831).
- Post-compromise tactics involve credential harvesting, lateral movement using Impacket and PsExec, dumping Active Directory databases with NTDSUTIL, and data exfiltration with tools like Certipy and ADExplorer.
- GRU operators employ defense evasion by clearing event logs using wevtutil and abusing DLL search order hijacking to execute malicious code stealthily.
- Persistence mechanisms include scheduled tasks, autorun registry modifications, and payload drop via Startup folders, detected through specific alerts and log monitoring.
- Heads-up detection signatures for malware families HEADLACE (backdoor with headless browser automation) and MASEPIE (exfiltration tool) are provided with hunting queries.
- Mitigation advice includes social engineering resilience training, enforcing least privilege, multi-factor authentication, network segmentation, centralized logging, deploying EDR/NDR, incident response readiness, and robust backups.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – GRU used PowerShell, PsExec, and Wscript/Cscript for script execution and lateral movement (“…using built-in tools like PowerShell, PsExec, or RDP to explore the network…”).
- [T1003] Credential Dumping – Active Directory database dumping with NTDSUTIL to harvest credentials (“…use Windows’ built-in ntdsutil.exe to extract the NTDS.dit database…”).
- [T1070] Indicator Removal on Host – Clearing event logs with wevtutil to evade detection (“…use native Windows utilities like wevtutil to wipe event logs after gaining access…”).
- [T1547] Boot or Logon Autostart Execution – Persistence through scheduled tasks, autorun registry keys, and startup folder payloads (“…rely on tried-and-true persistence methods including scheduled tasks, Run-key modifications, and Startup folder payloads…”).
- [T1071] Application Layer Protocol – Detection of exfiltration and command-and-control traffic via network telemetry (“…Network Detection and Response (NDR) can detect command-and-control traffic or data exfiltration…”).
- [T1486] Data Encrypted for Impact – Use of volume shadow copy manipulation tools like vssadmin.exe indicative of attempts to disrupt recovery (“…manipulate volume shadow copies to disable backup and forensic recovery…”).
- [T1110] Brute Force – Detection of RDP brute force activity from external sources (“…RDP brute force external to internal detection…”).
Indicators of Compromise
- [File Hashes] Malware samples related to HEADLACE and MASEPIE – hashes not specified in detail but referenced as detected in GRU campaigns.
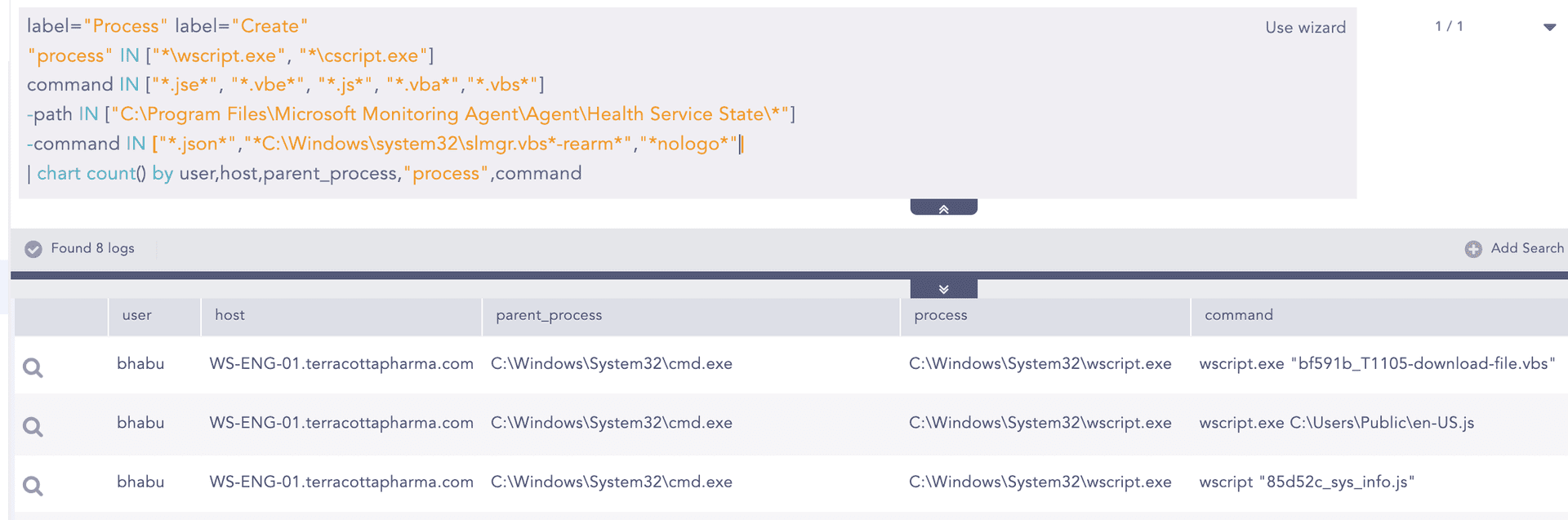
- [Processes] Process names and commands associated with suspicious behavior – for example: wscript.exe, cscript.exe executing .jse, .vbe, .vbs scripts; SCHTASKS.exe with XML task creation; ntdsutil.exe invoking “activate instance ntds”.
- [Domains/IPs] Network-based telemetry detection (NDR) hints at monitoring RDP brute force, SMB lateral movement, and DarkNet or Tor activity as network IOCs.
- [Registry Keys] Modifications to autorun registry paths such as HKCU/HKLM Run keys and Windows Scheduled Task cache registry trees.
Read more: https://www.logpoint.com/en/blog/frontline-intel-pinpointing-grus-ttps-in-the-recent-campaign/