Keypoints
- The Lotus Blossom group launched cyber espionage attacks primarily targeting government, manufacturing, telecommunications, and media organizations.
- Attackers used new variants of the Sagerunex tool leveraging a combination of conventional C&C servers and legitimate third-party cloud services like Dropbox, Twitter, and Zimbra for command-and-control communication.
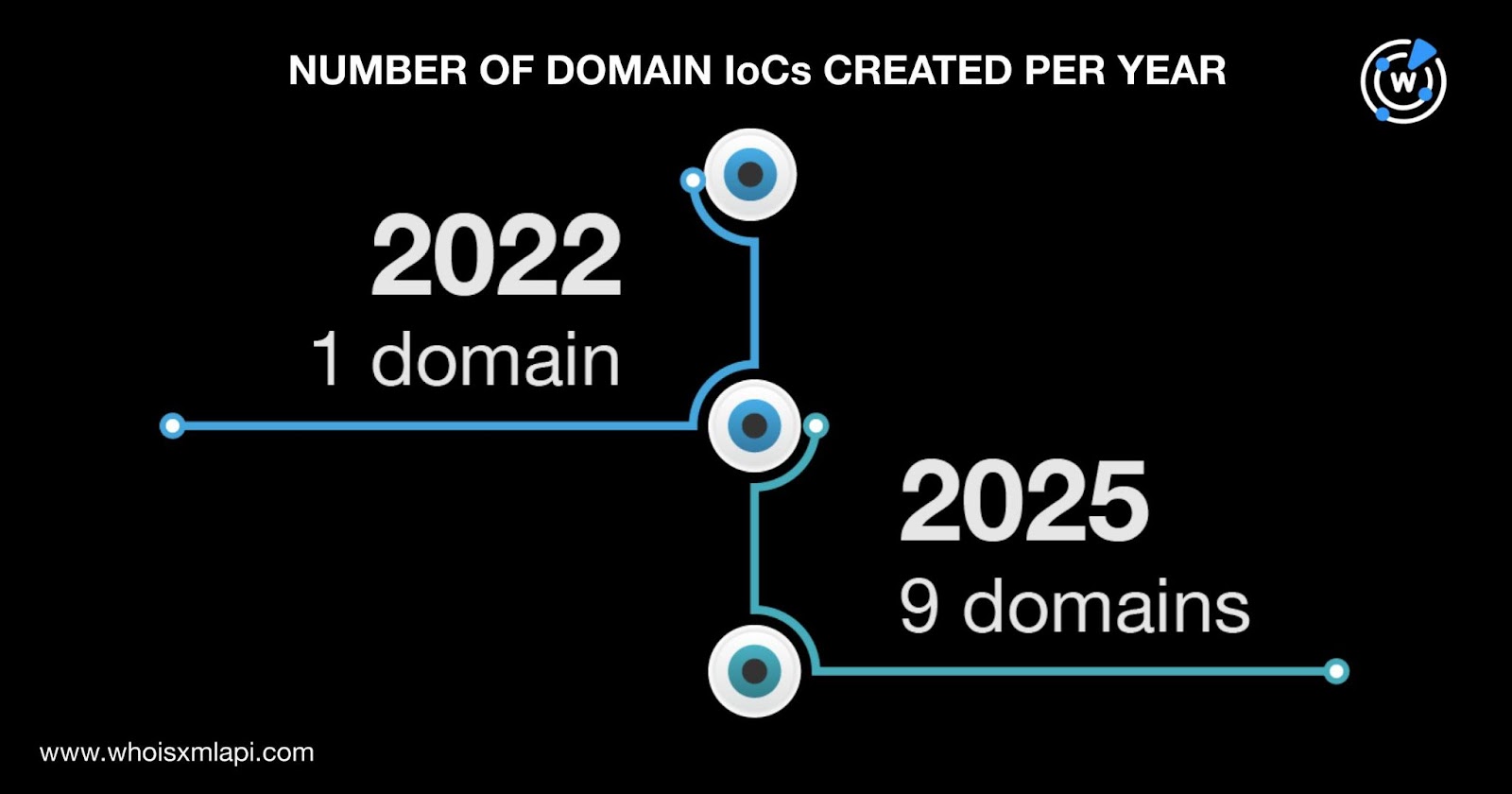
- Cisco Talos identified 10 domains and 28 IP addresses as initial indicators of compromise (IoCs), which were expanded to include over 200 email-connected, IP-connected, and string-connected domains.
- The majority of malicious domains were registered recently (between 2022 and 2025), predominantly through the registrar Netowl and mostly located in Japan.
- IP addresses linked to the campaign were geolocated mainly in China, with additional addresses in Germany, Singapore, Thailand, and the U.S., many belonging to telecommunications and cloud service ISPs.
- Numerous historical domain-to-IP and IP-to-domain resolutions suggest ongoing and evolving infrastructure for the campaign’s operations.
- Further analysis revealed multiple public email addresses linked to the IoCs, which connected to dozens of related domains, highlighting the depth of the infrastructure behind the attacks.
MITRE Techniques
- [T1071] Application Layer Protocol – Lotus Blossom used legitimate third-party cloud services like Dropbox, Twitter, and Zimbra as command-and-control tunnels to blend malicious traffic with normal application layer communications (‘used a combination of traditional command-and-control (C&C) servers and legitimate third-party cloud services…’).
- [T1105] Ingress Tool Transfer – The group deployed custom Sagerunex variants to infiltrate and maintain access to target networks by transferring tools and malware (‘Lotus Blossom developed new Sagerunex variants…’).
- [T1587] Develop Capabilities – Creation and use of customized hacking tools like new Sagerunex variants demonstrates Lotus Blossom’s development of their own capabilities to achieve their objectives (‘The researchers believe Lotus Blossom developed new Sagerunex variants…’).
Indicators of Compromise
- [Domains] Initial 10 malicious domains (e.g., acdserv[.]com, davoport[.]org, sensor-data[.]online), plus 90 email-connected and 106 IP-connected domains indicating extensive domain infrastructure.
- [IP Addresses] 28 IP addresses including 160[.]124[.]251[.]105, 103[.]213[.]245[.]95, 160[.]16[.]200[.]77 (malicious, linked to malware distribution), geolocated primarily in China and other countries.
- [Email Addresses] 14 email addresses found in historical WHOIS records linked to IoCs, with 5 public email addresses tied to 90 additional domains showing connection to the threat actor’s registration infrastructure.
Read more: https://circleid.com/posts/unearthing-the-dns-roots-of-the-latest-lotus-blossom-attack