Researchers uncovered a series of critical vulnerabilities in the Windows Kernel Streaming (KS) components, focusing on a previously overlooked attack surface beyond the well-known MSKSSRV driver. Their findings enabled a successful exploit of Windows 11 during Pwn2Own Vancouver 2024 by leveraging a proxy-based logical vulnerability that bypasses common validation checks. #MicrosoftWindows #KernelStreaming #MSKSSRV
Keypoints
- Windows Kernel attack surfaces have shifted from Win32k to CLFS, with recent focus on the smaller MSKSSRV driver leading to the discovery of multiple vulnerabilities.
- Two notable MSKSSRV vulnerabilities, CVE-2023-29360 (logical vulnerability) and CVE-2023-36802 (type confusion), were analyzed but more issues were found in the broader Kernel Streaming components.
- Kernel Streaming architecture includes core drivers ks.sys and ksthunk.sys, which manage forwarding and compatibility functions and are critical for multimedia device interactions.
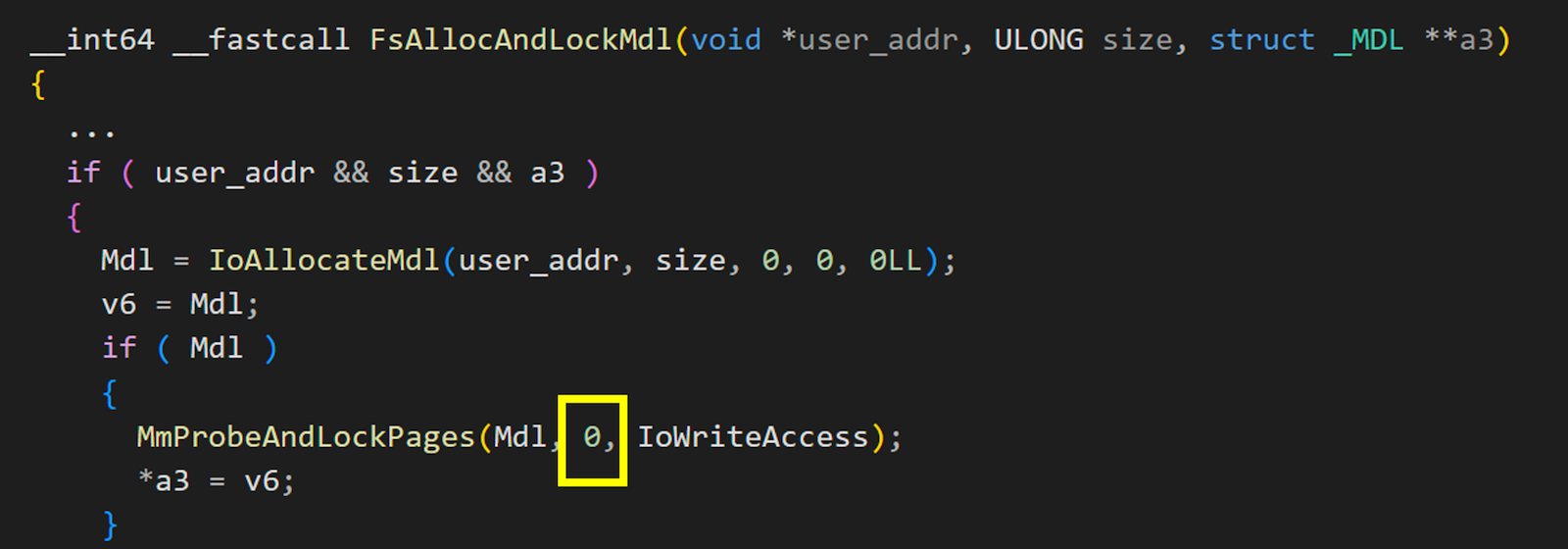
- A logical bug class involving incorrect usage of RequestorMode in IOCTL calls allowed bypassing of security checks, leading to CVE-2024-35250, the critical vulnerability exploited at Pwn2Own 2024.
- Exploitation leveraged a double-fetch vulnerability to alter property sets dynamically, enabling arbitrary IOCTL calls with kernel-mode privileges on audio devices supporting KSPROPSETID_DrmAudioStream.
- The exploit bypassed kernel protections like kCFG by utilizing a legitimate kernel function (RtlSetAllBits) to perform arbitrary writes, facilitating privilege escalation.
- This vulnerability has existed since Windows 7 and demonstrated 100% exploitation reliability, prompting urgent recommendations for Windows updates and ongoing research into Kernel Streaming.
MITRE Techniques
- [T1210] Exploitation of Vulnerability – Exploited logical and type confusion vulnerabilities in the Kernel Streaming driver to achieve arbitrary kernel memory write (“…allowing to write data to any address in the kernel”).
- [T1105] Ingress Tool Transfer – Used arbitrary IOCTLKSPROPERTY calls to interact dynamically with kernel driver functions for privilege escalation (“…use IOCTLKSPROPERTY of Kernel Streaming to perform arbitrary operations”).
- [T1055] Process Injection (Privilege Escalation) – Leveraged a legitimate kernel API (RtlSetAllBits) to modify token privileges and bypass kernel mitigations like kCFG (“…create an arbitrary write primitive from a legitimate function… to achieve EoP”).
- [T1203] Exploitation for Credential Access – Bypassed kernel security checks by exploiting RequestorMode mishandling (“…Irp->RequestorMode was properly set here… but subsequent processing relied incorrectly on this value”).
Indicators of Compromise
- [File Names] Critical Windows drivers analyzed: msksrv.sys (Microsoft Kernel Streaming Service), ks.sys, ksthunk.sys, portcls.sys (audio driver library).
- [CVE Identifiers] Major vulnerabilities: CVE-2023-29360, CVE-2023-36802, CVE-2024-35250, CVE-2024-38054, CVE-2024-38055, CVE-2024-38056, CVE-2024-38057.
- [GUIDs] Exploited properties: KSPROPSETIDDrmAudioStream, KSPROPSETIDService used in IOCTL property set manipulation.
- [Vulnerability Types] Logical vulnerabilities including double-fetch bugs and access mode mismatches.