This article reveals a new kernel vulnerability in the Windows Kernel Streaming (KS) subsystem that enables privilege escalation on Windows 11 through exploitation of IOCTLKSENABLE_EVENT handling in WoW64 processes. The research demonstrates a previously overlooked bug class and introduces a novel method to bypass privilege checks by modifying the global SeDebugPrivilege variable, impacting Windows 11 kernel security. #Windows11 #KernelStreaming
Keypoints
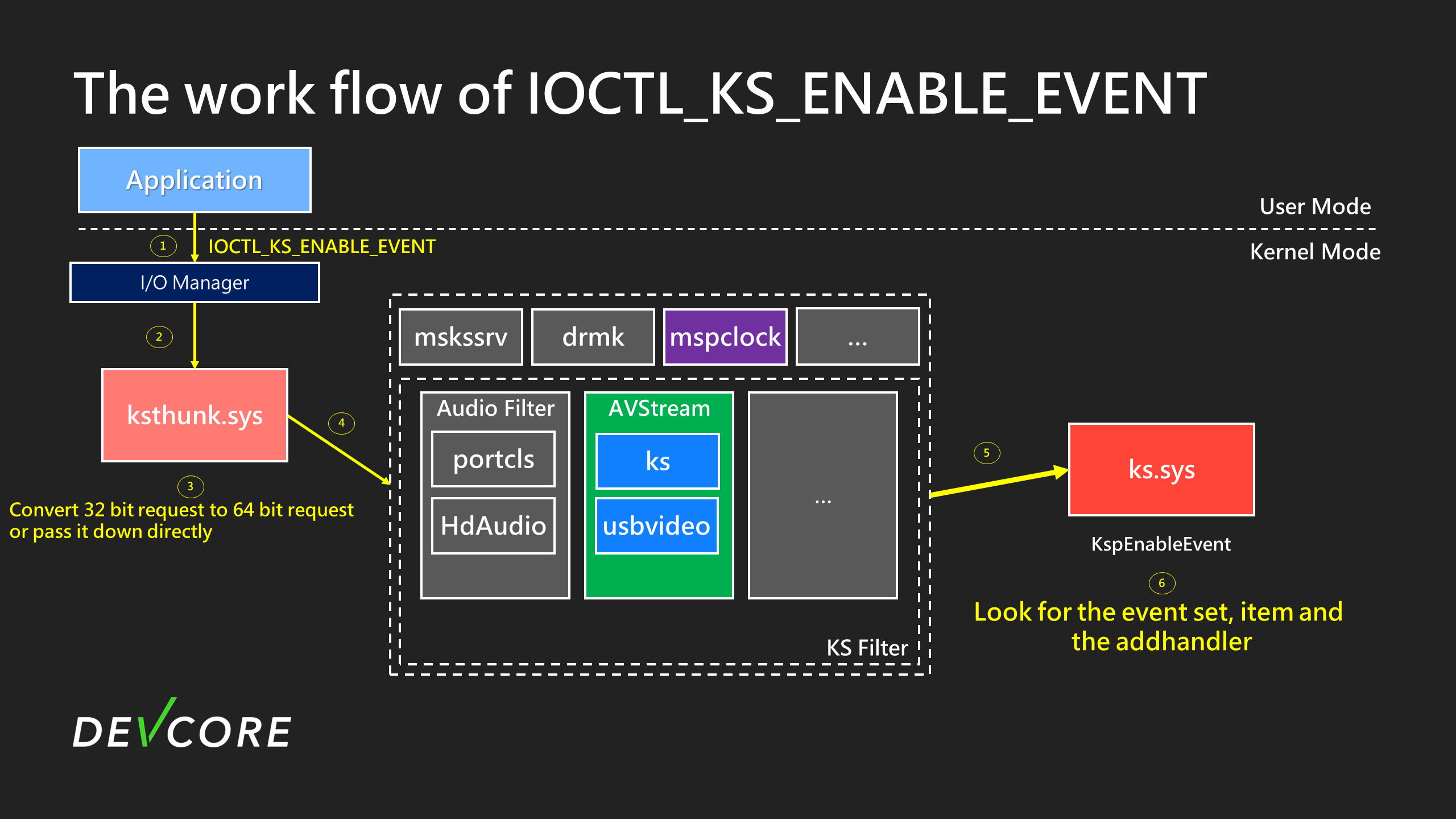
- New vulnerability CVE-2024-30090 was discovered in the Kernel Streaming (KS) IOCTLKSENABLE_EVENT interface related to 32-bit to 64-bit request conversion in WoW64 processes.
- The bug involves a double fetch and incorrect handling of KSEVENTTYPEQUERYBUFFER flags, allowing user-controlled kernel memory operations via crafted IOCTL calls.
- An arbitrary kernel memory increment primitive was achieved by exploiting event registration with kernel objects and triggering kernel event callbacks.
- Traditional privilege escalation techniques such as abusing token privileges or IoRing were either unstable or caused system crashes in this context.
- A new exploitation method was developed by manipulating the global nt!SeDebugPrivilege variable to point to a privilege (SeChangeNotifyPrivilege) already granted to normal users, allowing them to gain PROCESSALLACCESS on high-privilege processes.
- This vulnerability is a design flaw in Windows, particularly in handling IRP RequestorMode and kernel streaming event processing, likely affecting other privilege-related bugs in the kernel.
- The research recommends updated Windows versions and further kernel driver fuzzing, especially targeting audio and video drivers like Hdaudio.sys and Usbvideo.sys.
MITRE Techniques
- [T1213] Exploitation for Defense Evasion – The vulnerability allowed bypassing typical privilege checks by modifying the global SeDebugPrivilege variable, enabling normal users to obtain high access permissions. (‘changing nt!SeDebugPrivilege from 0x14 to 0x17 allows normal users with SeChangeNotifyPrivilege to get PROCESSALLACCESS’)
- [T1068] Exploitation of Kernel Vulnerability – The kernel streaming IOCTL handling flaw allowed execution of arbitrary kernel increment primitive by triggering KS events. (‘constructing a kernel object and queuing a DPC or worker item to increment arbitrary kernel memory’)
- [T1203] Exploitation of Privilege Escalation Vulnerability – The attacker used crafted IOCTL requests in WoW64 process context to escalate privileges leveraging the double fetch bug. (‘a primitive allowing arbitrary IOCTLKSENABLE_EVENT with KernelMode based on 32-bit to 64-bit conversion bug’)
Indicators of Compromise
- [CVE IDs] Vulnerabilities exploited – CVE-2024-35250, CVE-2024-30084, CVE-2024-30090
- [Function names] related to exploitation – CKSAutomationThunk::ThunkEnableEventIrp, KsSynchronousIoControlDevice, KsGenerateEvent
- [IOCTL Codes] Kernel streaming control codes – IOCTLKSENABLEEVENT, IOCTLKSDISABLEEVENT