This article explores multiple vulnerabilities discovered in the Windows Kernel Streaming (KS) framework, focusing on frame-related buffer handling and Memory Descriptor List (MDL) misuse. It reveals several bug classes leading to memory corruption, arbitrary physical memory writes, and privilege escalation, directly impacting the Windows kernel streaming subsystem. #WindowsKernelStreaming #WindowsKernel
Keypoints
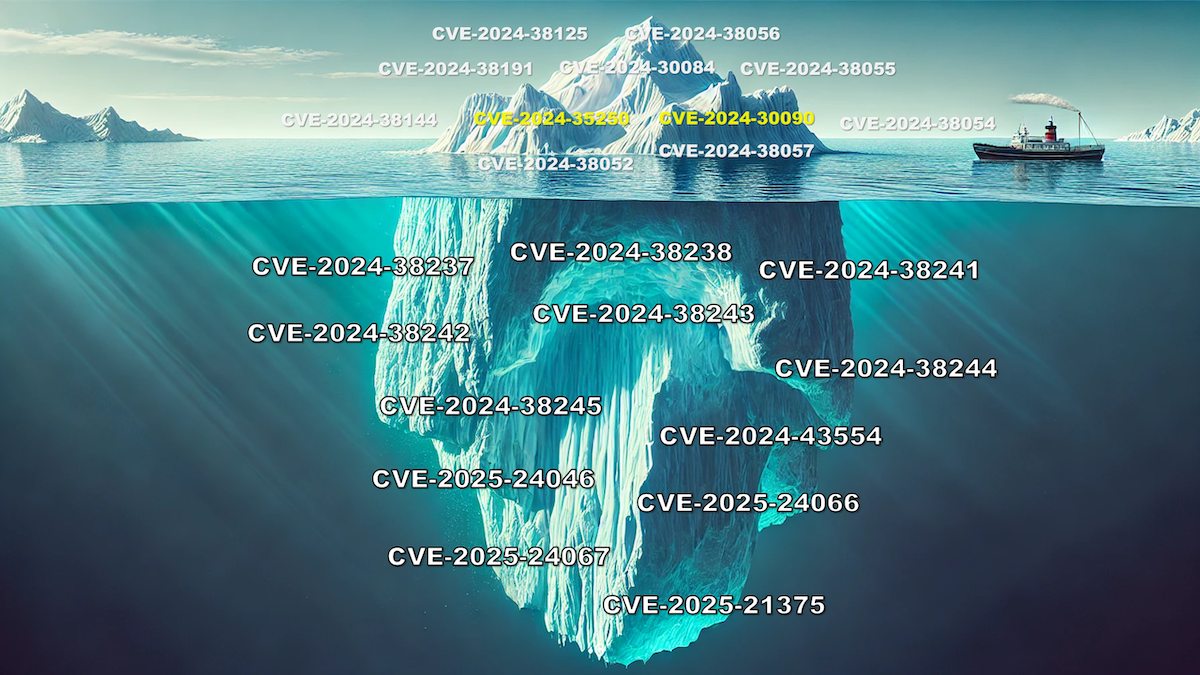
- Over 20 Kernel Streaming vulnerabilities were identified between late 2023 and 2024, mainly related to AVStream frame handling.
- MDL mismatch causes buffer overflow by linking KSSTREAM_HEADER structures to incorrect MDLs, demonstrated by CVE-2024-38237 and CVE-2025-21375.
- The Forgotten Lock bug arises from improperly locked MDLs leading to uninitialized PFN arrays and arbitrary physical memory writes, as seen in CVE-2024-38238.
- Arbitrary physical memory writes enable privilege escalation via overwriting kernel code, such as modifying PsOpenProcess security checks.
- Frame Buffer Misalignment exposes LookasideList corruption, allowing arbitrary memory write primitives by exploiting invalid pointer alignment and list traversal logic.
- Kernel Streaming’s default allocator uses padding and alignment that can be manipulated to build fake linked lists for exploitation.
- Misuse and misunderstanding of common kernel APIs like MmProbeAndLockPages and MmMapLockedPagesSpecifyCache are central to these vulnerabilities.
MITRE Techniques
- [T1176] Browser Extensions – The attacker exploits kernel streaming frame buffer handling bugs during streaming IOCTL requests to gain memory corruption.
- [T1218] System Binary Proxy Execution – ksthunk.sys impersonates 32-bit requests to 64-bit ks.sys leading to proxying vulnerabilities (“…improper handling of user-controlled KSSTREAM_HEADER… may lead to memory corruption”).
- [T1055] Process Injection – The physical memory write primitive is used to patch kernel functions like PsOpenProcess for privilege escalation (“…overwrite a security check inside PsOpenProcess…”).
- [T1068] Exploitation for Privilege Escalation – Exploiting uninitialized MDL PFN arrays allows arbitrary physical memory writes that facilitate EoP attacks.
- [T1203] Exploitation of Remote Services – Vulnerabilities revealed through reading streams from webcams suggest exploitation via device streaming interfaces.
Indicators of Compromise
- [CVE Identifiers] Vulnerabilities identified include CVE-2024-38054 (proxying mishandling), CVE-2024-38237 and CVE-2025-21375 (MDL mismatch buffer overflow), CVE-2024-38238 and CVE-2024-38241 (Forgotten Lock with arbitrary physical memory write), CVE-2025-24046 (double free), and CVE-2024-38245 (frame buffer misalignment).
- [Kernel Driver Files] Involved system files include ksthunk.sys and ks.sys, which handle IOCTLKSREAD_STREAM requests and MDL allocations.
- [Structures & Flags] KSSTREAMHEADER structures with OptionsFlags like KSSTREAMHEADEROPTIONSFPERSIST_SAMPLE (0x8000) used to manipulate MDL allocation flow.
Read more: https://devco.re/blog/2025/05/17/frame-by-frame-kernel-streaming-keeps-giving-vulnerabilities-en/