Proactive threat hunting focuses on detecting and neutralizing cyber threats before attacks occur by analyzing early indicators such as newly registered domains and malicious hosting activity. Silent Push supports this approach with advanced intelligence and tools that provide deep visibility into adversarial infrastructure, enhancing organizational cyber defenses. #SilentPush #Cybersecurity
Keypoints
- Traditional detection models are reactive, relying on alerts after attacks have started, whereas proactive threat hunting seeks to identify threats early during their planning phases.
- Proactive hunting uses external signals like domain registrations, certificate anomalies, and hosting patterns to detect adversarial infrastructure before exploitation.
- Silent Push offers a comprehensive DNS and content-based threat intelligence database that delivers finished intelligence and reduces manual investigative work.
- Key proactive elements include external visibility, threat attribution, automation, scale, and preemptive disruption of threat campaigns.
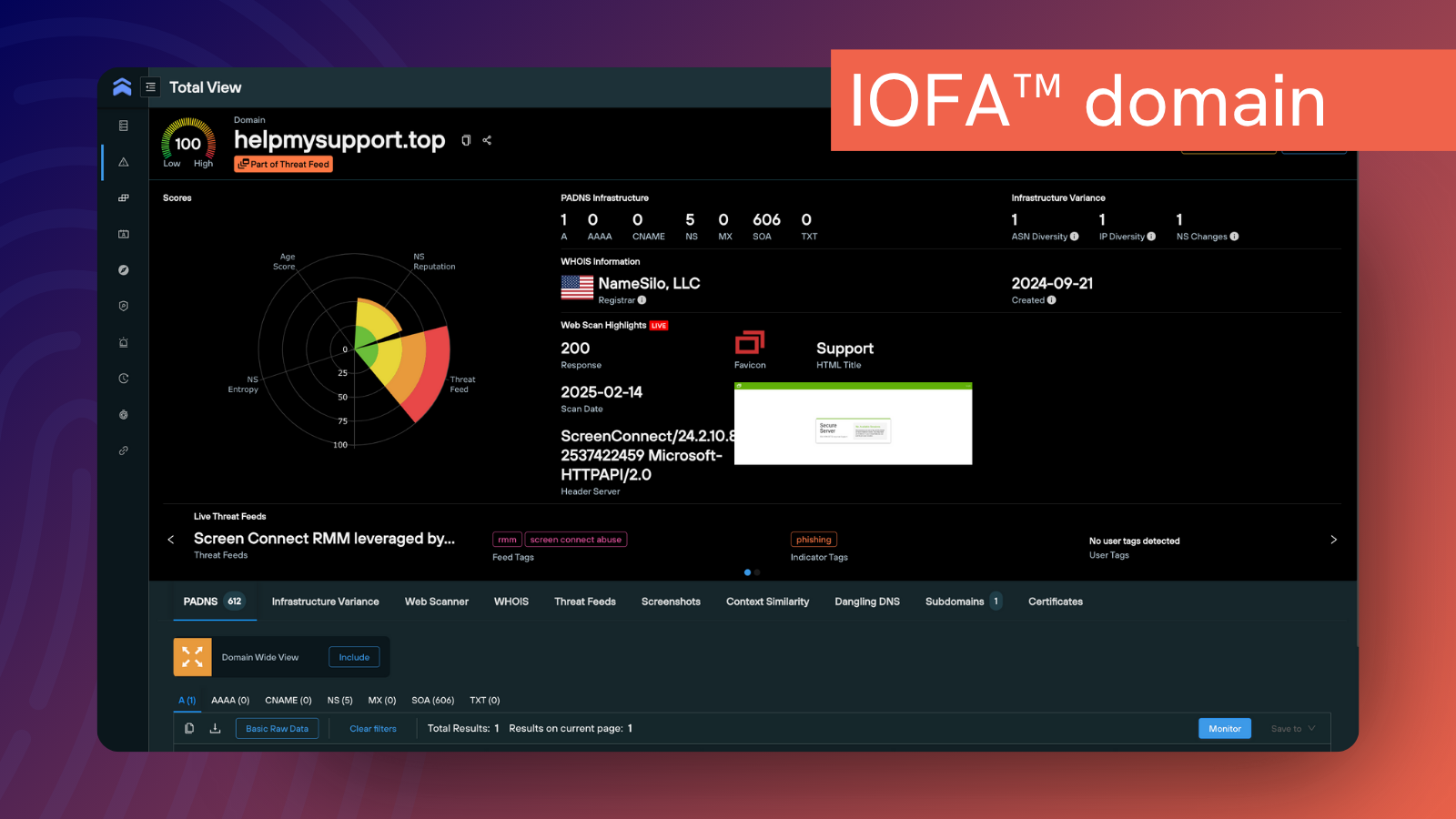
- Silent Push’s IOFA™ intelligence provides forward-looking, actionable data weeks or months before traditional feeds detect threats.
- The platform supports flexible custom threat hunting through APIs and enrichment tools, enabling detailed investigation into malware families and attacker techniques.
- Silent Push empowers even small SOC and IR teams to perform rapid threat discovery at scale, mitigating critical gaps in defenses.