A North Korean hacking group, Konni, disguised malware within a fraudulent VAT payment document. The malware, disguised as a HWP file, utilizes a hidden LNK file to execute malicious commands, targeting sensitive information from victims, particularly related to communications companies. (Affected: Communication sector, victims of malware attacks)
Keypoints :
- The malware is disguised as a VAT payment document named ‘부가세납부서(국세징수법 시행규칙-별지 제1호서식)’.
- It uses the HWP file extension while actually being a malicious LNK file.
- Several file hashes (MD5, SHA-1, SHA-256) are provided for the malware variants.
- The malware includes commands that allow the attacker to collect sensitive information from infected systems.
- The commands can delete evidence of infiltration and gather data on user files and system information.
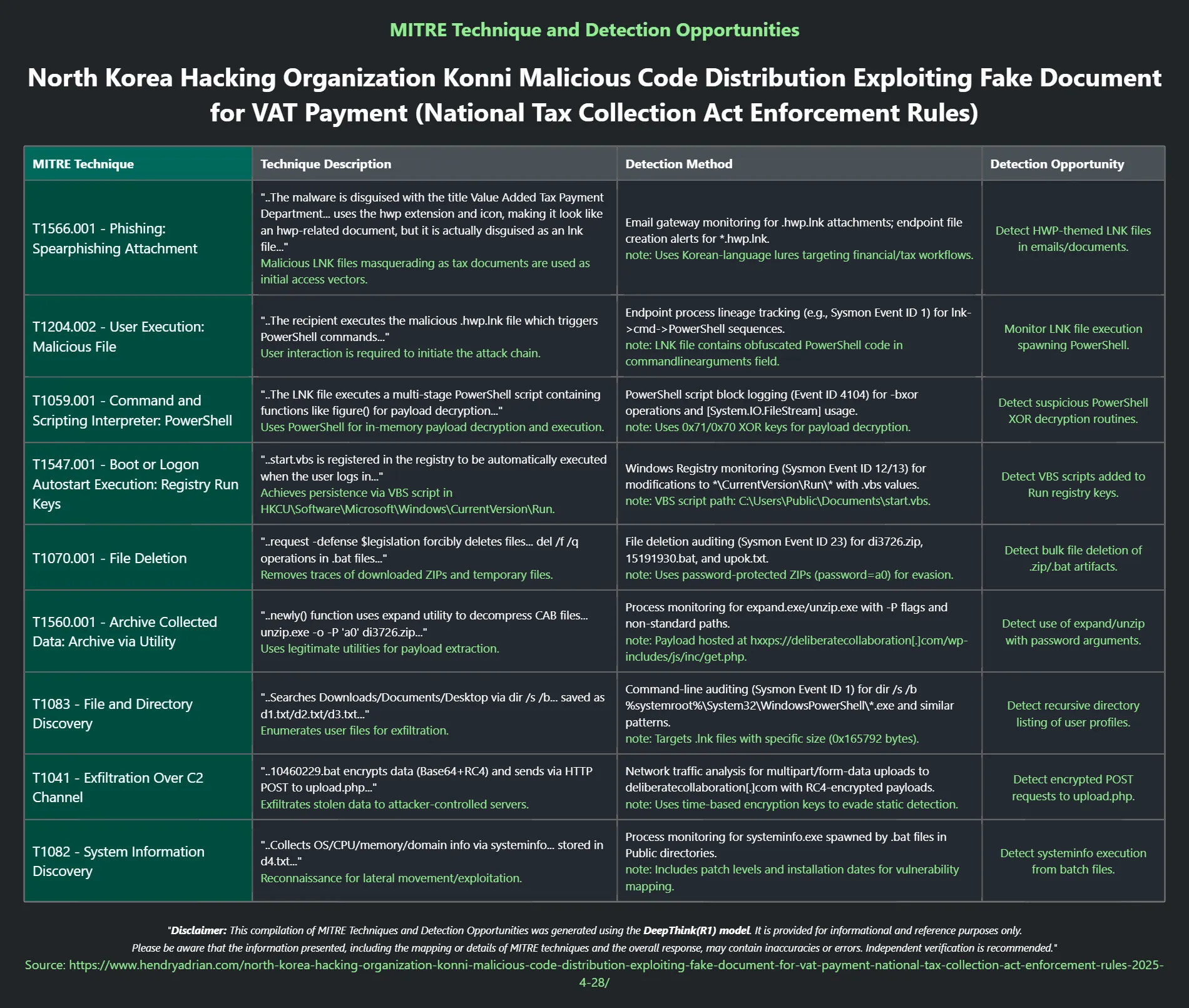
MITRE Techniques :
- T1560.001 (Archive Collected Data): The malware uses the command ‘expand’ to extract payloads from CAB files.
- T1070.001 (File Deletion): The malware employs the ‘del’ command to remove files and erase traces of its activities.
- T1083 (File and Directory Discovery): The malware searches for specific file types in various directories.
- T1041 (Exfiltration Over Command and Control Channel): The malware sends collected data to a remote server through HTTP POST requests.
- T1082 (System Information Discovery): The malware collects system information including OS, CPU, and memory details.
Indicator of Compromise :
- The article states specific file hashes (MD5, SHA-1, SHA-256) that can be used to identify the malware variants.
- File names related to the malicious activities, such as ‘부가세납부서(국세징수법 시행규칙-별지 제1호서식).hwp.lnk’, serve as indicators of malicious intent.
- The malware uses command line arguments which can be tracked as an IOC for unusual activity linked to its functions.
- There are various indicators related to the download and execution of batch files that facilitate further malicious actions.
Full Story: https://wezard4u.tistory.com/429478