This article outlines the discovery of multiple security vulnerabilities through a bug bounty program, emphasizing issues such as CORS misconfiguration, subdomain takeover, and XSS, along with recommendations for remediation.
Keypoints :
- Reported vulnerabilities were discovered during a bug bounty program and are redacted due to an NDA.
- Initial passive reconnaissance is suggested to avoid detection during vulnerability exploration.
- CORS misconfiguration allows session cookie reflection, increasing the risk of cookie theft via subdomains.
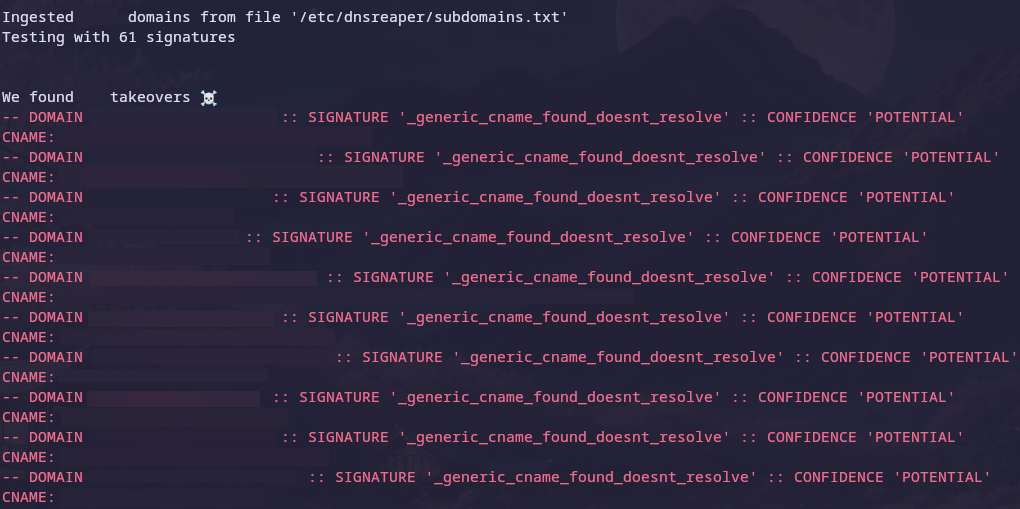
- Chaining vulnerabilities, including subdomain takeover and XSS, can lead to account takeover (ATO) scenarios.
- Tools such as Burp, Waymore, subfinder, and dnsReaper were utilized for reconnaissance and vulnerability analysis.
- Identified an unprotected subdomain that failed to sanitize user input, making it vulnerable to XSS.
- JWT forgery vulnerability was found, allowing circumvention of user checks through a mass assignment flaw.
- The attack sequence outlined demonstrates how attackers could exploit these vulnerabilities for ATO.
- Recommendations for remediation include implementing an origin allow-list, ensuring proper cookie security, adding WAF protections, and validating JWT regions.