This blog discusses a new campaign by the APT group Earth Kasha, detected in March 2025, targeting government agencies and public institutions in Taiwan and Japan using spear-phishing to deliver a modified version of the ANEL backdoor. The campaign raises concerns about potential espionage and data theft. Recommendations for organizations include implementing a zero-trust policy and monitoring DNS over HTTPS abuse. Affected: Taiwan, Japan, government agencies, public institutions
Keypoints :
- Earth Kasha’s campaign detected in March 2025 targets Taiwan and Japan.
- Utilizes spear-phishing emails to deliver modified ANEL backdoor.
- Victims include government agencies and public institutions.
- Potential impact involves information theft and data compromise.
- Recommendations include a zero-trust approach and monitoring for DNS over HTTPS abuse.
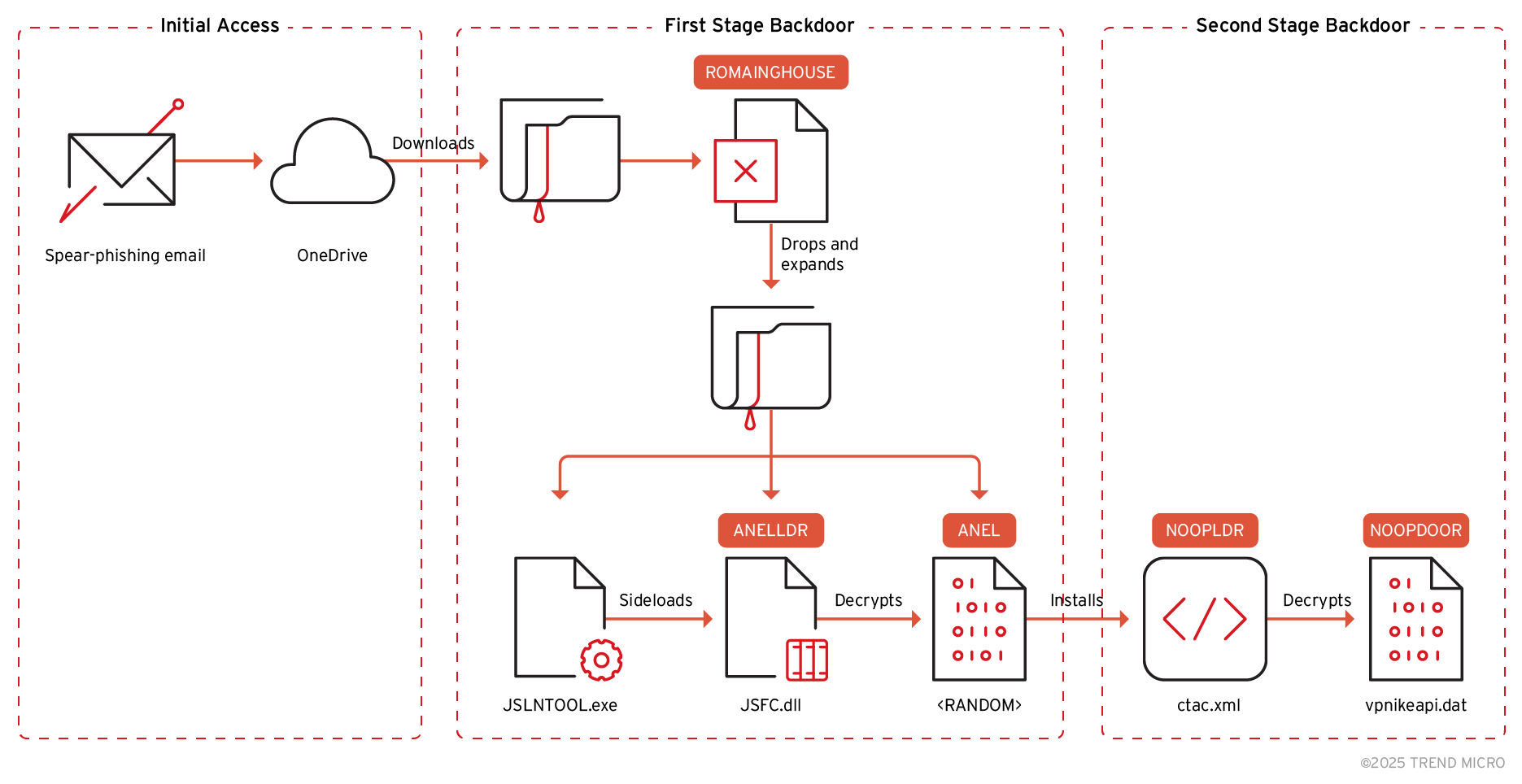
- First stage backdoor identified as ANEL, second stage as NOOPDOOR.
- New command for BOF execution added to ANEL file.
- Proactive measures such as user education on OneDrive links recommended.
MITRE Techniques :
- Initial Access (T1566.001): Utilized spear-phishing via emails embedding OneDrive links to deliver malicious content.
- Execution (T1203): Maro execution via the malicious Excel file (ROAMINGMOUSE) triggering attacks on user interaction.
- Persistence (T1547.001): Achieved by using SharpHide for launching NOOPDOOR and hiding its UI on autorun.
- Exfiltration (T1041): Utilized the ANEL backdoor for the collection of system information and potential data theft.
Indicator of Compromise :
- [URL] OneDrive links embedded in spear-phishing emails (e.g., OneDrive link to ZIP file)
- [File] ROAMINGMOUSE Excel file (malicious dropper)
- [File] ANEL (malware) as part of the payload
- [File] JSFC.dll (malicious loader)
- [IP Address] 172.233.73.249, 172.105.62.188, 192.46.215.56, 139.162.38.102
Full Story: https://www.trendmicro.com/en_us/research/25/d/earth-kasha-updates-ttps.html