The Outlaw group, primarily active in Brazil, utilizes a Perl-based crypto mining botnet targeting Linux environments through weak SSH credentials. This analysis presents empirical data from an incident report by Kaspersky, detailing the tactics employed by the attackers, including the use of malicious scripts and techniques for evasion and persistence. Recommendations for fortifying server security against such threats are also provided. Affected: Linux environments, United States, Germany, Italy, Thailand, Singapore, Taiwan, Canada, Brazil
Keypoints :
- Outlaw is identified as a Perl-based crypto mining botnet focusing on Linux vulnerabilities.
- The botnet exploits weak or default SSH credentials for unauthorized access.
- A case study analyzed reveals the use of malicious scripts to establish persistence and perform various functions.
- The group utilizes evasion techniques like obfuscation of files and hidden directory structures.
- Affected regions include the United States, Germany, Italy, Thailand, Singapore, Taiwan, Canada, and Brazil.
- Recommendations include strengthening SSH configurations and monitoring processes.
MITRE Techniques :
- Execution: Command and Scripting Interpreter: Unix Shell (T1059.004) – Uses shell scripts for execution tasks.
- Persistence: Scheduled Task/Job: Cron (T1053.003) – Implements scheduled jobs to maintain presence.
- Persistence: Account Manipulation: SSH Authorized Keys (T1098.004) – Modifies SSH keys for continued access.
- Defense Evasion: Obfuscated Files or Information (T1027) – Uses obfuscated scripts to avoid detection.
- Defense Evasion: Indicator Removal: File Deletion (T1070.004) – Deletes files to hide traces of activity.
- Defense Evasion: File and Directory Permissions Modification (T1222) – Modifies permissions to restrict access.
- Defense Evasion: Hide Artifacts: Hidden Files and Directories (T1564.001) – Conceals malicious files within hidden directories.
- Defense Evasion: Obfuscated Files or Information: Software Packing (T1027.002) – Packages the code to avoid signature detection.
- Credential Access: Brute Force (T1110) – Attempts to guess weak passwords for access.
- Discovery: System Information Discovery (T1082) – Gathers system specifications to identify weak points.
- Discovery: Process Discovery (T1057) – Monitors running processes for resource-heavy applications.
- Discovery: Account Discovery (T1087) – Checks for existing users and their privileges.
- Discovery: System Owner/User Discovery (T1033) – Identifies system admin accounts.
- Discovery: System Network Connections Discovery (T1049) – Scans for active network connections.
- Lateral Movement: Remote Services: SSH (T1021.004) – Moves laterally across systems via SSH.
- Collection: Data from Local System (T1005) – Collects information from compromised systems.
- Command and Control: Application Layer Protocol (T1071) – Communicates with standards-compliant applications.
- Command and Control: Ingress Tool Transfer (T1105) – Transfers tools to the compromised system.
- Exfiltration: Exfiltration Over Alternative Protocol (T1048) – Uses alternative protocols for data extraction.
- Impact: Resource Hijacking (T1496) – Hijacks system resources for cryptocurrency mining.
- Impact: Service Stop (T1489) – Stops essential services to maintain control over the system.
Indicator of Compromise :
- [File] tddwrt7s.sh
- [File] dota.tar.gz
- [File] b/run
- [File] a/kswapd0
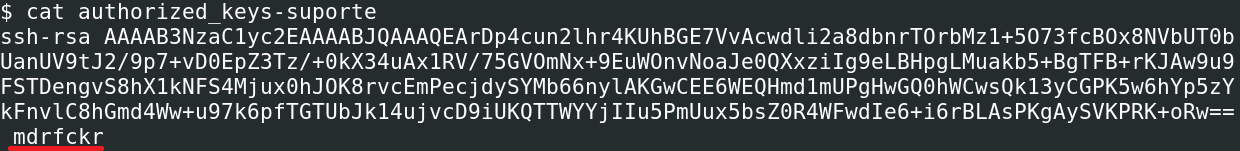
- [SSH Key] ssh-rsa AAAAB3NzaC1yc2EAAAABJQAAAQEArDp4cun2lhr4KUhBGE7VvAcwdli2a8dbnrTOrbMz1+5O73fcBOx8NVbUT0bUanUV9tJ2/9p7+vD0EpZ3Tz/+0kX34uAx1RV/75GVOmNx+9EuWOnvNoaJe0QXxziIg9eLBHpgLMuakb5+BgTFB+rKJAw9u9FSTDengvS8hX1kNFS4Mjux0hJOK8rvcEmPecjdySYMb66nylAKGwCEE6WEQHmd1mUPgHwGQ0hWCwsQk13yCGPK5w6hYp5zYkFnvlC8hGmd4Ww+u97k6pfTGTUbJk14ujvcD9iUKQTTWYYjIIu5PmUux5bsZ0R4WFwdIe6+i6rBLAsPKgAySVKPRK+oRw== mdrfckr
Full Story: https://securelist.com/outlaw-botnet/116444/