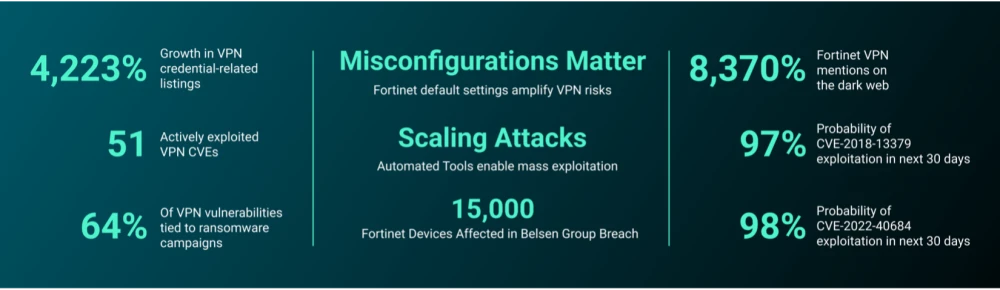
The report discusses persistent vulnerabilities in VPN infrastructures, specifically CVE-2018-13379 and CVE-2022-40684, which remain critical targets for cybercriminals and state-sponsored actors. The analysis highlights a surge in discussions about Fortinet VPN exploits, revealing a 4,223% increase in related chatter on cybercriminal forums and emphasizing the need for improved defenses. Affected: VPN infrastructures, organizations using Fortinet, Ivanti, Cisco, SonicWall, Citrix.
Keypoints :
- VPN-related vulnerabilities like CVE-2018-13379 and CVE-2022-40684 are key tools for attackers.
- There has been a significant 4,223% increase in discussions around exploited Fortinet VPNs since 2018.
- Attackers primarily use credential theft and administrative control methods to exploit VPNs.
- Stolen VPN credentials are highly marketable on the dark web.
- CVE-2018-13379 enables unauthenticated access to sensitive system files.
- CVE-2022-40684 allows attacker access to Fortinet devices without credentials, leading to administrative control.
- State-sponsored groups and cybercriminals exploit VPN vulnerabilities for varying objectives.
- Automation and AI are increasing the scale and sophistication of VPN attacks.
MITRE Techniques :
- Credential Dumping (T1003): Attackers use exploits to steal credentials stored in plaintext.
- Exploitation of Vulnerability (T1203): Attackers exploit CVE-2018-13379 to execute credential theft.
- Application Layer Protocol Abuse (T1071): Attackers manipulate administrative APIs using CVE-2022-40684 to bypass authentication.
- Automated attacks (T1059): Using automated scripts to exploit vulnerabilities en masse.
Indicator of Compromise :
- No IoCs Found
Full Story: https://reliaquest.com/blog/threat-spotlight-credential-theft-vs-admin-control-two-devastating-paths-to/