SAP disclosed a critical vulnerability in SAP NetWeaver Visual Composer, identified as “CVE-2025-31324,” which allows unauthorized code execution through unrestricted file uploads. Customers are urged to apply the security patch released on April 24, 2025, immediately to mitigate the risk. Affected: SAP NetWeaver, Government Agencies, Enterprises
Keypoints :
- ReliaQuest published an investigation uncovering a critical vulnerability in SAP NetWeaver on April 22, 2025.
- Vulnerability CVE-2025-31324 has a severity score of 10 and allows for unauthorized file uploads.
- SAP acknowledged ReliaQuest’s findings and released a patch immediately.
- Attackers exploited previous vulnerabilities, including potential old ones like CVE-2017-9844.
- ReliaQuest implemented detection mechanisms to identify exploitation attempts against SAP NetWeaver.
- Security risks are exacerbated by unsatisfactory patch management in on-premises SAP systems.
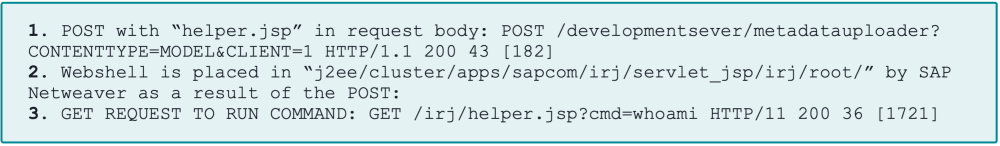
- Attackers used JSP webshells to execute code on compromised systems.
MITRE Techniques :
- Command and Control (T1071): Attackers utilized Brute Ratel framework to maintain control over the systems.
- Privilege Escalation (T1068): Attackers leveraged existing vulnerabilities for gaining increased access rights.
- Exploitation for Client Execution (T1203): Malicious JSP files allowed remote code execution by exploiting a vulnerable endpoint.
- Input Data Manipulation (T1203): Attackers uploaded crafted JSP webshells through malicious POST requests.
- Remote File Inclusion (RFI): Initial exploitation suspected to revert to RFI, allowing execution of arbitrary code.
Indicator of Compromise :
- [Hash] 1f72bd2643995fab4ecf7150b6367fa1b3fab17afd2abed30a98f075e4913087
- [Hash] 794cb0a92f51e1387a6b316b8b5ff83d33a51ecf9bf7cc8e88a619ecb64f1dcf
- [Filename] Helper.jsp
- [Filename] Cache.jsp