The latest findings from Kaspersky indicate a resurgence of the Triada Trojan, which has now evolved to infect Android devices by embedding malicious software directly into firmware. This sophisticated multi-stage loader can compromise system processes and applications, leading to severe security risks, including the theft of cryptocurrency and sensitive user data. Victims include users across multiple countries and various Android devices, particularly counterfeit models.
Affected: Android devices, cryptocurrency wallets, messaging and social media applications
Affected: Android devices, cryptocurrency wallets, messaging and social media applications
Keypoints :
- Older Android vulnerabilities enabled attacks for root access, exploited by malware.
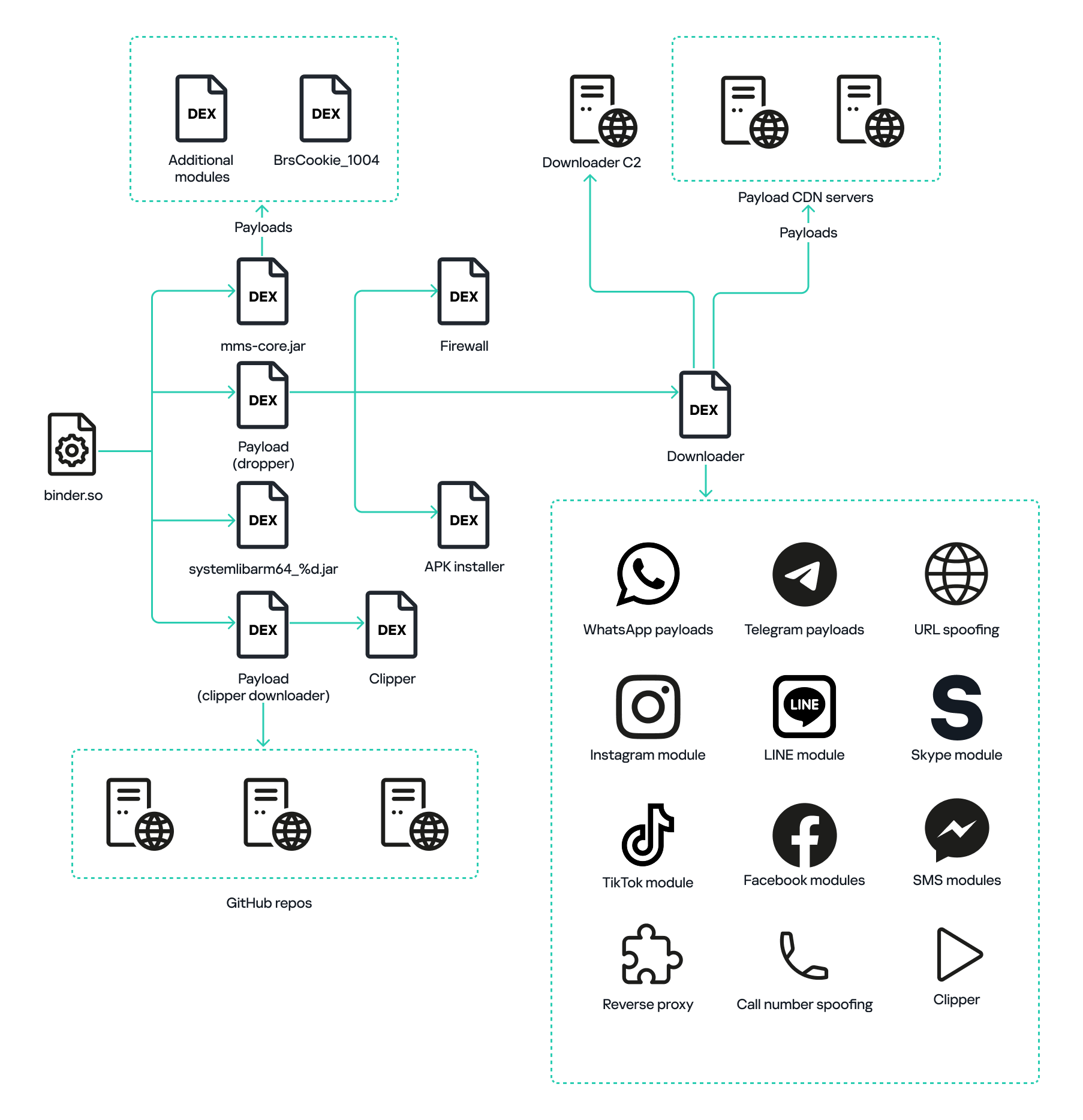
- New Triada Trojan versions infect devices even before sale by embedding malicious components in firmware.
- The malware targets popular applications, intercepting their functionalities and routing communications through compromised processes.
- The payloads demonstrate various malicious behaviors, including modifying financial transactions and stealing user credentials.
- Kaspersky detected over 4,500 infected devices globally, with significant impacts in several countries.
MITRE Techniques :
- Persistence (T1547.001) – Implementing malicious code in the firmware and system libraries to maintain access through the Zygote process.
- Command and Control (T1071) – Communication with C2 servers to receive instructions, download modules, and exfiltrate data.
- Credential Dumping (T1003.001) – Extracting stored credentials from applications such as Instagram and WhatsApp.
- Data Encrypted for Impact (T1486) – Using encryption techniques to hide communication and payloads from analysis.
- Exploitation of Remote Services (T1210) – Exploiting vulnerabilities in applications to execute malware and access sensitive user data.
Indicator of Compromise :
- [Hash] f468a29f836d2bba7a2b1a638c5bebf072cbbc58776ddc44abaa557325440bfbfb937b1b15fd56c9d8e5bb6b90e0e24a2ac4d8e1077dce6f4d2ba9875b987ca77b8905af721158731d24d0d06e6cb27e9dd92503bd21d12ff0f2b9740fb6e529
- [Hash] 89c3475be8dba92f4ee7de0d981603c101dff60fbf8cdf98980150eb15617e4118fef4b6e229fc01c8b9921bb0353bb021be50a028a505b1d23955abfd2bdb3e43adb868af3812b8f0c47e38fb93746a511443977de2d07c3ee0cee3edae8dc8716f0896b22c2fdcb0e3ee56b7c5212f83dbc4b95f9ae8a83811163b301fe8c78892c6decebba3e26c57b20af7ad4ccaa7127978fac175c9a14cd8d894192f78a9a106b9df360ec9d28f5dfaf4b1f0b5c30c309e175905ffcbd17adb55009240c4efe3733710d251cb041a916a46bc44e9029811df1dd8acacfe69450b033804e961cb0c7d317ace2ff6159efe30276a
- [URL] http://ompe2.7u6h8.xyz/tgzip/44a08dc22b45b9418ed427fd24c192c6.zip
- [URL] https://app-file.b-cdn.net/poctest/pc2215202501061400.zip
- [Domain] g.sxim.me
Full Story: https://securelist.com/triada-trojan-modules-analysis/116380/