An active phishing campaign is targeting high-profile X accounts to exploit credentials for fraudulent activities. The campaign focuses on various sectors including U.S. political figures, journalists, technology firms, and cryptocurrency organizations. Notably, the attacker utilizes sophisticated techniques to evade detection while pursuing financial gains. Affected: X accounts, U.S. political figures, large technology organizations, cryptocurrency organizations
Keypoints :
- Phishing campaign targets high-profile X accounts.
- Victims include U.S. political figures, journalists, and tech firms.
- Campaign linked to previous successful phishing operations.
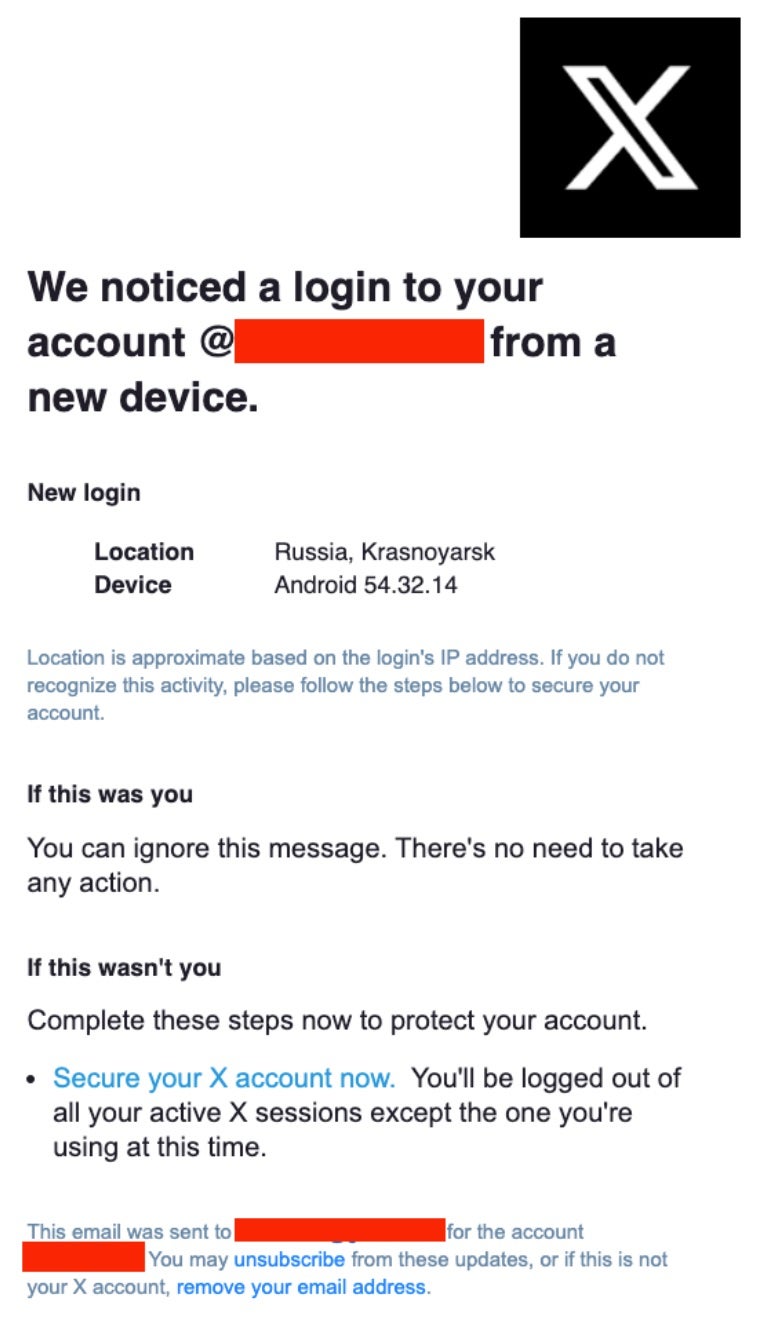
- Attackers exploit credential phishing via fake login notices.
- Attacker utilizes Google’s “AMP Cache” to evade detection.
- Compromised accounts used for spreading fraudulent cryptocurrency content.
- Domains like securelogins-x[.]com and x-recoverysupport[.]com host phishing pages.
- Malicious activities are linked to an IP address associated with Belize-based VPS.
- FASTPANEL service is frequently abused for rapid phishing site deployment.
- Emerging account intrusions observed, including the Tor Project compromise.
- Various domains are used interchangeably for delivery of phishing emails.
- Threat actors are adapting and evolving their tactics continuously.
- Recommendations include using unique passwords, enabling two-factor authentication, and verifying URLs.
MITRE Techniques :
- Phishing (T1566) – Employed phishing emails using fake login notices to steal credentials.
- Credential Dumping (T1003) – Gained access to accounts by harvesting login credentials through phishing.
- Exploitation of third-party software (T1190) – Used Google’s AMP Cache to redirect users to phishing pages.
- Account Manipulation (T1098) – Once accounts are compromised, used them to initiate fraudulent cryptocurrency schemes.
Indicator of Compromise :
- [Domain] buy-tanai[.]com
- [Domain] dataoptimix[.]com
- [Domain] gamecodestudios[.]com
- [Domain] securelogins-x[.]xyz
- [SHA-1] e2221e5c58a1a976e59fe1062c6db36d4951b81e
Full Story: https://www.sentinelone.com/labs/phishing-on-x-high-profile-account-targeting-campaign-returns/