AkiraBot is a sophisticated spam framework that targets website contact forms and chat widgets, promoting dubious SEO services. Since September 2024, it has targeted over 400,000 websites and successfully spammed at least 80,000, employing AI-generated messages and multi-layered evasion tactics to bypass CAPTCHA protections. Affected: websites, small to medium-sized businesses, SEO sector
Keypoints :
- AkiraBot is designed to spam website contact forms and chat widgets with AI-generated messages.
- The framework has successfully targeted over 400,000 websites, with reports of more than 80,000 successful spam incidents.
- It utilizes OpenAI for generating spam messages tailored to individual websites.
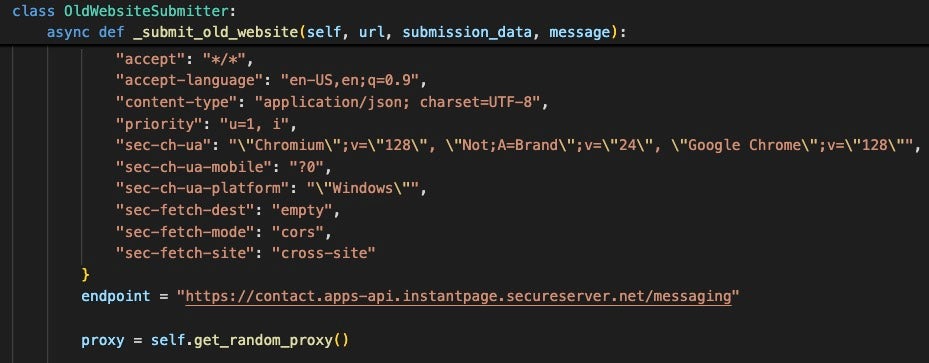
- AkiraBot is modular and employs multiple methods to evade CAPTCHA and network detection.
- The bot has origins traced back to September 2024 and was initially referred to as “Shopbot” targeting Shopify sites.
- It later expanded to GoDaddy, Wix, and generic contact forms used by small businesses.
- The bot’s architecture allows complete customization of targeting options and spamming tactics.
- CAPTCHA bypass methods include the use of hCAPTCHA, reCAPTCHA, and specialized JavaScript for browser fingerprinting.
- It employs proxy services like SmartProxy to obfuscate its traffic and evade detection.
- Operators track success rates and failed attempts through logging capabilities in CSV files and Telegram bot notifications.
- The AkiraBot infrastructure rotates domains to minimize detection, leveraging SEO brand names like Akira and ServiceWrap.
MITRE Techniques :
- T1071.001: Application Layer Protocol – AkiraBot uses HTTP requests to communicate with targeted websites.
- T1070.001: Indicator Removal on Host – The bot logs success in ‘submissions.csv’ while clearing logs on failed attempts.
- T1071.003: Application Layer Protocol – The bot uses the OpenAI API to generate custom spam messages.
- T1560.001: Archive Collected Data – It archives various bot versions and scripts to facilitate spamming from different environments.
- T1019: Remote Access Tools – The bot includes communication and logging tools to monitor sessions and report to a Telegram bot.
Indicator of Compromise :
- [Domain] akirateam[.]com
- [Domain] servicewrap-go[.]com
- [Domain] useakira[.]com
- [IP Address] 91.195.240[.]94
- [IP Address] 86.38.202[.]110
Full Story: https://www.sentinelone.com/labs/akirabot-ai-powered-bot-bypasses-captchas-spams-websites-at-scale/