The March 2025 Monthly Intelligence Insights from Securonix Threat Labs highlights significant malware threats, including OBSCURE#BAT, StilachiRAT, XCSSET, and CoffeeLoader, which utilize advanced evasion techniques and target various sectors. Additionally, the report outlines increasing cyberattacks from groups like UNC3886 and MirrorFace, as well as the exploitation of vulnerabilities related to Windows LNK files and Fortinet devices. Affected: Malware, Cybersecurity, Telecommunications, Government, Financial, Defense, Healthcare, Education, Manufacturing
Keypoints :
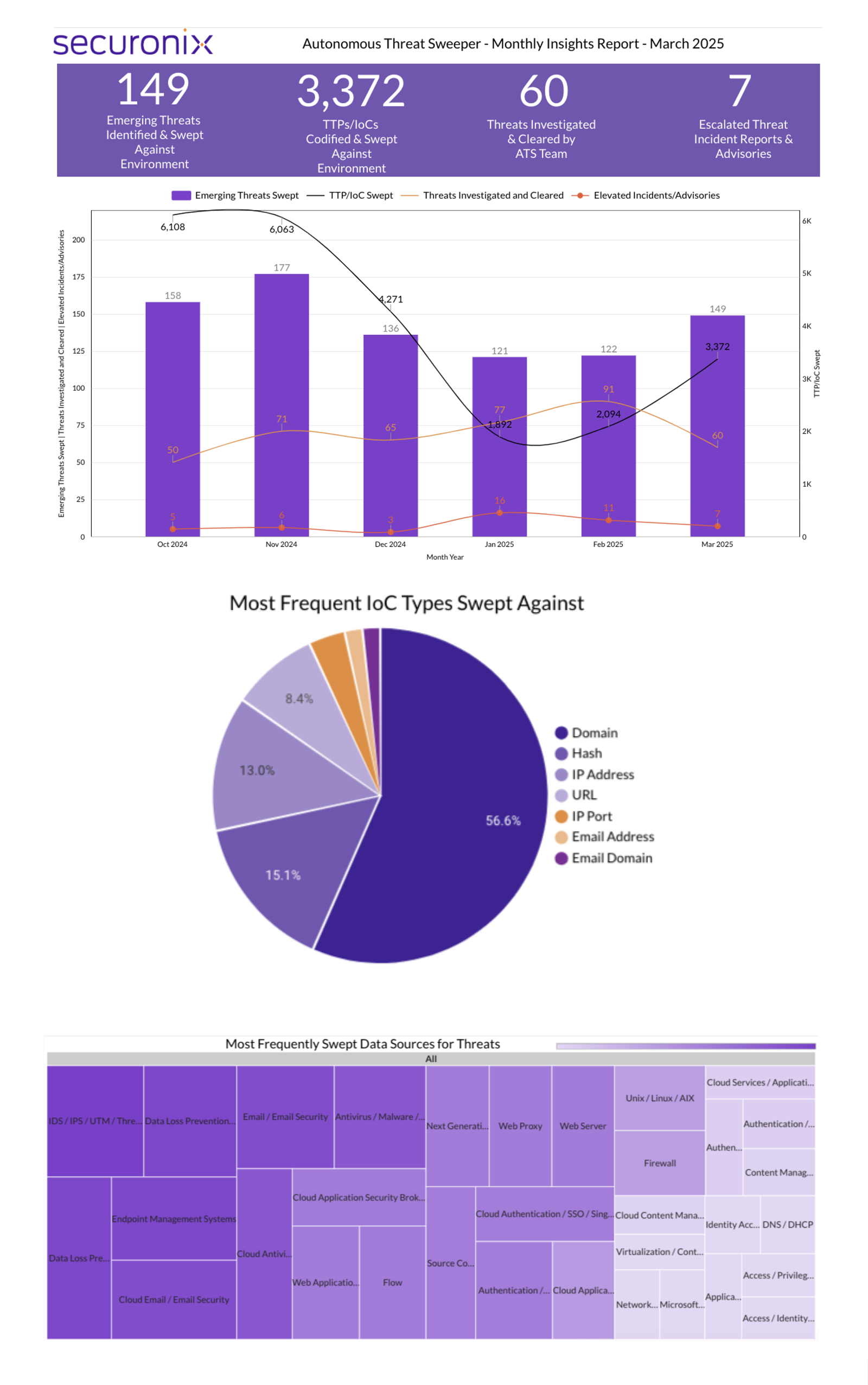
- Securonix identified 3,372 TTPs and IoCs and analyzed 149 emerging threats in March 2025.
- Malware campaigns are increasing, particularly with new strains like OBSCURE#BAT and StilachiRAT.
- Cybercriminals use sophisticated techniques such as obfuscation and API hooking to evade detection.
- UNC3886 is exploiting outdated Juniper routers, while MirrorFace targets diplomatic organizations using advanced tactics.
- New vulnerabilities have been exploited, including a zero-day in Windows LNK files, affecting various critical sectors.
- Ransomware campaigns like VanHelsing and Medusa show evolving tactics with double extortion methods.
MITRE Techniques :
- T1071.001 – Application Layer Protocol: StilachiRAT communicates using DNS and HTTPS protocols (Ports 53 and 443).
- T1076 – Remote Services: CoffeeLoader uses the Windows Task Scheduler to establish persistence.
- T1135 – Access Token Manipulation: OBSCURE#BAT hides its processes by manipulating API calls.
- T1036 – Masquerading: OBSCURE#BAT disguises batch files with unnecessary characters for detection evasion.
- T1069 – Permission Groups Discovery: UNC3886 uses base64-encoded commands to gain insight into system permissions.
- T1218 – Signaling: MirrorFace leverages Visual Studio Code remote tunnels for malware delivery.
Indicator of Compromise :
- [File] OBSCURE#BAT (batch files with obfuscated characteristics)
- [Domain] example.com (for command-and-control fallback)
- [File] StilachiRAT.exe (remote access Trojan executable)
- [File] XCSSET.dmg (malicious macOS installer)
- [File] CoffeeLoader.dll (malware loader)
Full Story: https://www.securonix.com/blog/securonix-threat-labs-monthly-intelligence-insights-march-2025/