This article provides a comprehensive guide on using WinDBG for debugging buffer overflow vulnerabilities in the Vulnserver application. It covers the steps necessary to exploit this security flaw, including preparing the Vulnserver, fuzzing, taking control of the EIP, generating shellcode, and executing the exploit successfully. The knowledge shared is beneficial for exploit development practice in secure environments.
Affected: Vulnserver
Affected: Vulnserver
Keypoints :
- Vulnserver is intentionally designed to be insecure for exploit development practice in isolated environments.
- Initial setup includes downloading Vulnserver and connecting via Telnet on port 9999.
- Fuzzing is initiated to understand the buffer size that leads to a crash.
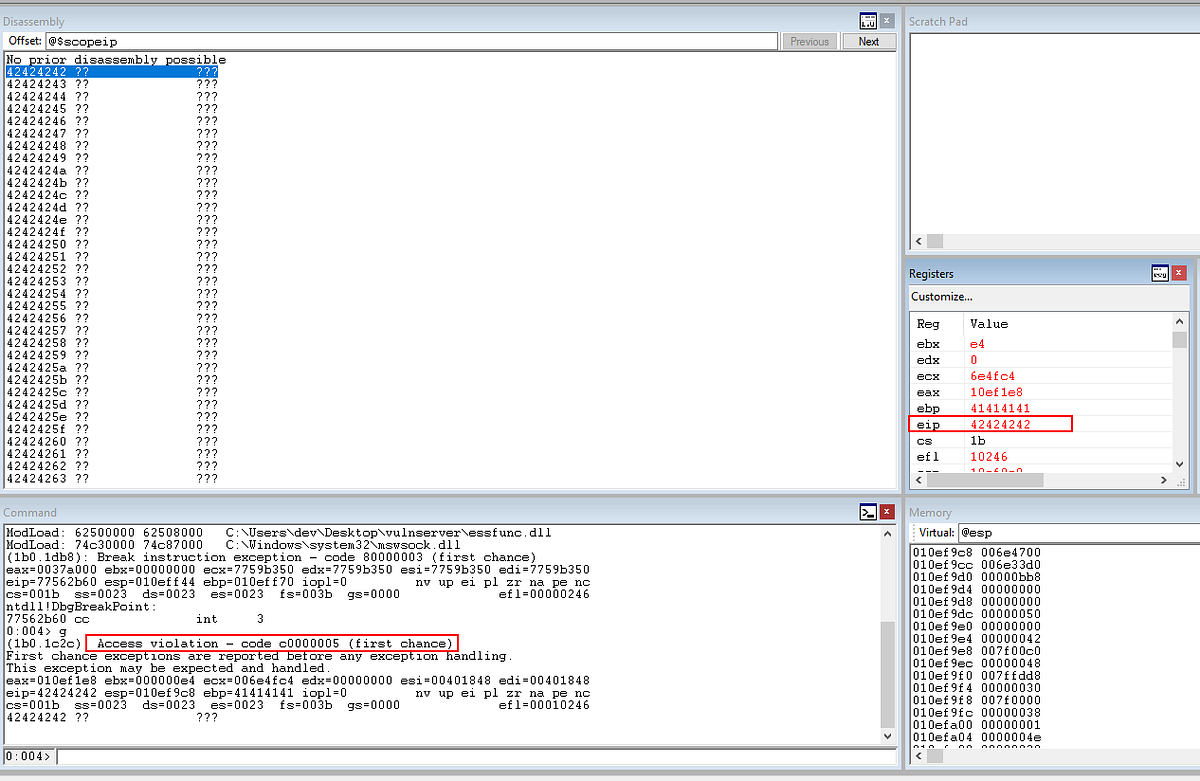
- Identification of the EIP overflow point is achieved using WinDBG and pattern generation tools.
- Code snippets provided for fuzzing payload to test buffer limits and observe application behavior.
- Determination of bad characters that can interfere with shellcode execution.
- Shellcode is generated using msfvenom, taking into account bad characters.
- Reverse shell access is established after finding a suitable address for EIP redirection.
- Final successful exploitation leads to acquiring a reverse shell using crafted payload.