Flax Typhoon, a Chinese state-sponsored APT group, has shown a significant evolution in its cyber espionage activities since mid-2021, primarily targeting Taiwanese entities while expanding globally to North America, Africa, and Southeast Asia. The group’s strategic focus aligns with Chinese government objectives, utilizing sophisticated techniques to maintain prolonged access to compromised networks. Affected: Taiwan, North America, Africa, Southeast Asia, government agencies, educational institutions, critical manufacturing facilities, and information technology organizations.
Keypoints :
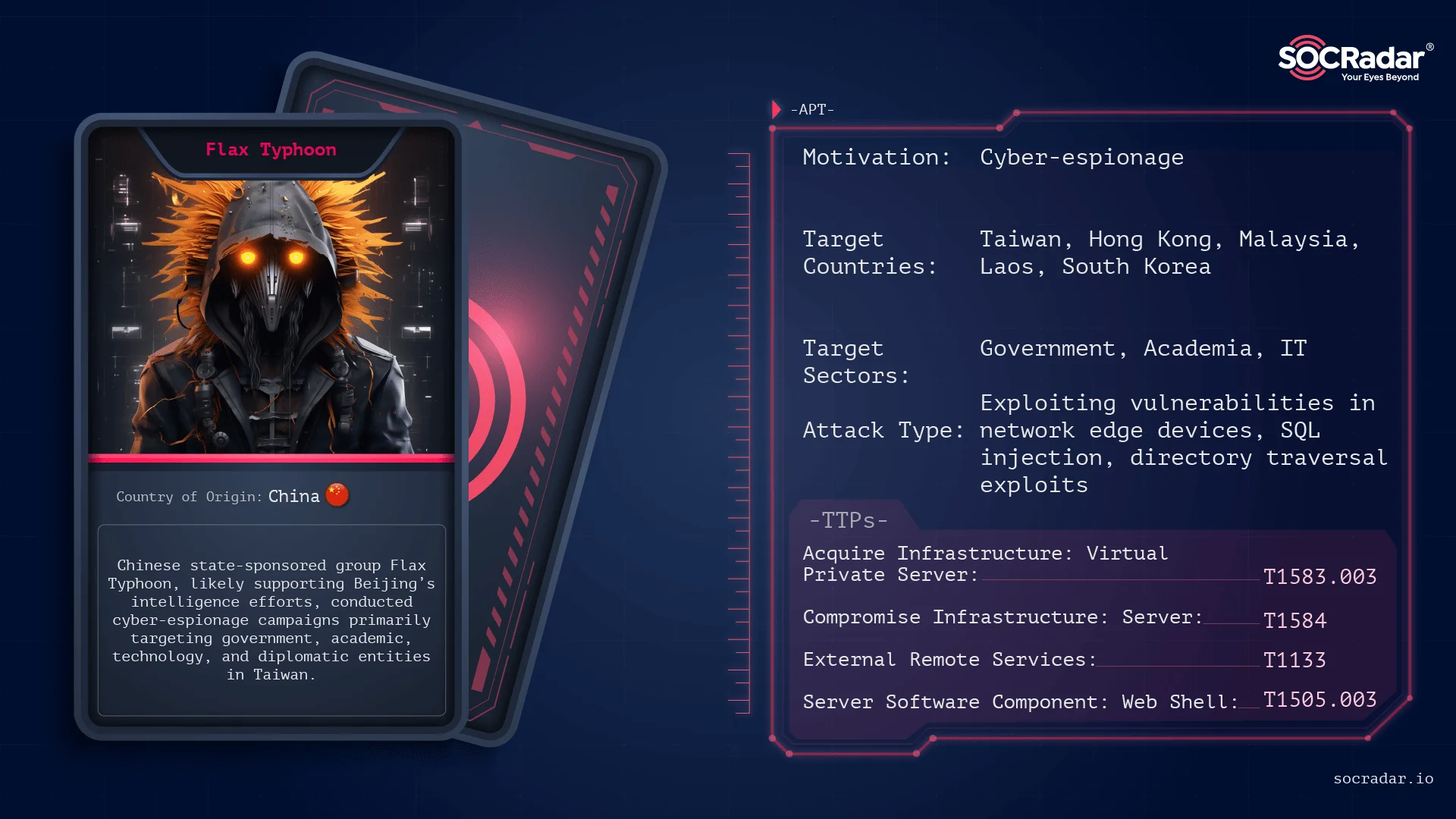
- Flax Typhoon is a state-sponsored APT group from China, operational since 2021.
- Primarily targets Taiwanese entities but has expanded operations globally.
- Focuses on cyber espionage across various sectors including government, education, and technology.
- Employs minimal malware deployment while maintaining extended network access.
- Utilizes techniques such as exploiting public-facing server vulnerabilities for initial access.
- Maintains persistence through advanced methods, including manipulating system processes and services.
- Utilizes VPN connections and renames executables to avoid detection.
- The group is linked to the Raptor Train botnet, integrating cyber intrusion capabilities.
- Mitigation strategies include robust patch management and continuous monitoring.
MITRE Techniques :
- Active Scanning: Vulnerability Scanning (T1595.002) – Scans for vulnerabilities in targets.
- Acquire Infrastructure: Virtual Private Server (T1583.003) – Utilizes VPS for operations.
- Compromise Infrastructure: Server (T1584.004) – Targets servers for potential exploitation.
- Exploit Public-Facing Application (T1190) – Exploits vulnerabilities in public-facing applications for access.
- Command and Scripting Interpreter (T1059) – Executes commands via interpreters.
- External Remote Services (T1133) – Uses external remote services to maintain persistence.
- Server Software Component: Web Shell (T1505.003) – Deploys web shells for remote access.
- Accessibility Features: Event Triggered Execution (T1546.008) – Manipulates accessibility features for unauthorized execution.
- Create or Modify System Process: Windows Service (T1543.003) – Alters Windows services for persistent access.
- Exploitation for Privilege Escalation (T1068) – Exploits vulnerabilities to gain higher privileges.
- Masquerading: Match Legitimate Name or Location (T1036.005) – Renames files to appear legitimate.
- Use Alternate Authentication Material: Pass the Hash (T1550.002) – Employs pass-the-hash techniques for credential access.
- OS Credential Dumping: LSASS Memory (T1003.001) – Dumps LSASS memory to collect credentials.
- OS Credential Dumping: Security Account Manager (T1003.002) – Targets the SAM to extract hashed passwords.
- Ingress Tool Transfer (T1105) – Transfers tools into the target environment for control.
- Protocol Tunneling (T1572) – Utilizes tunneling techniques to obscure command and control communications.
Indicator of Compromise :
- [Domain] w8510.com
Full Story: https://socradar.io/dark-web-profile-flax-typhoon/